TRUTH /// AWAKENING /// DISCLOSURE
The Architecture of Power Behind the Scandal
Introduction — Why This Report Exists
This report marks a systems exposure event. It exists because individual documents, while seemingly mundane, reveal recurring architectures that extend far beyond one individual when analyzed collectively across finance, science, and governance.
Report Chapters & Discovery Path
AUDIO REVIEW: ARCHITECTURE OF POWER
SECTION I — ORIENTATION
This section establishes that the Epstein files are not a conclusion; they are a cross-sectional snapshot of elite coordination across finance, technology, and global policy networks. Volume itself is identified as a form of "signal saturation" used to fragment attention.
PODCAST WALKTHROUGH: THE 3-MILLION PAGE DISCLOSURE
A comprehensive deep-dive into the document release, framing the context of systems exposure.
SECTION I — ORIENTATION
WHY THE EPSTEIN FILES MATTER NOW
The release of roughly three million pages of DOJ material related to Jeffrey Epstein is not significant because it adds shock value to a story the public already finds disturbing. It matters because the context has changed. For years, the Epstein case was framed narrowly—criminal acts, moral outrage, isolated enablers. What was missing was systems-level scrutiny. The current release arrives at a moment when trust in institutions, finance, media, science, and governance is already eroding. In that environment, documents are no longer read for scandal alone, but for structure: who interacted with whom, through what mechanisms, and to what long-term effect.
This section establishes a critical reframing. The Epstein files are not a conclusion; they are a cross-sectional snapshot of elite coordination across finance, philanthropy, academia, technology, intelligence-adjacent spaces, and global policy networks. Epstein himself functioned less as an originator and more as an access broker—a facilitator who sat at the intersection of capital, influence, and vulnerable ambition. When read correctly, the files illuminate how power moves quietly: through funding pathways, social proximity, credentialed environments, and informal leverage rather than overt command. Orientation, therefore, is about resisting the temptation to collapse the story into villains and instead tracking systems that outlive individuals.
Finally, this section defines how the report must be read. Volume is not transparency. The sheer scale of the document dump risks overwhelming analysis and fragmenting attention—what GAR terms signal saturation. Section I sets the methodological discipline for everything that follows: separating verified records from inference, behavior from intent, and coincidence from pattern. The goal is not accusation, but comprehension. If these files reveal anything enduring, it is that modern power rarely announces itself. It embeds. Orientation is the act of learning to see that embedding clearly—without fear, without sensationalism, and without losing precision.
SECTION II — Architecture of Deception
“Volume is not transparency. Structure is.”
UNDERSTANDING THE RELEASE
The release of approximately three million pages of material by the U.S. Department of Justice is not a narrative disclosure—it is an archive exposure. These documents were never designed to be read as a coherent story. They were generated across years by different agencies, law firms, courts, financial institutions, and investigators, each operating within narrow mandates. Section II establishes how the release must be approached: not as a linear record of events, but as a fragmented system of records whose meaning only emerges when relationships are reconstructed across silos.
This section explains why many readers experience confusion or dismissal when engaging the files. The architecture of the release favors compartmentalization. Financial data is separated from behavioral testimony. Scientific correspondence is detached from funding trails. Legal exhibits are isolated from policy outcomes. This fragmentation is not accidental—it mirrors how modern institutions protect themselves. Understanding the architecture is therefore a prerequisite for understanding the truth content of the documents themselves.
Finally, Section II provides methodological discipline. Without a framework, researchers risk either drowning in volume or cherry-picking sensational fragments. GAR’s approach treats the release as a distributed system: each document is a node, meaningful only in relation to others. This section teaches readers how to orient themselves inside that system before attempting interpretation.
SECTION III — Exclusive Access Broker
SECTION III — EPSTEIN AS AN EXCLUSIVE ACCESS BROKER
“Influence belongs to those who control access, not ideas.”
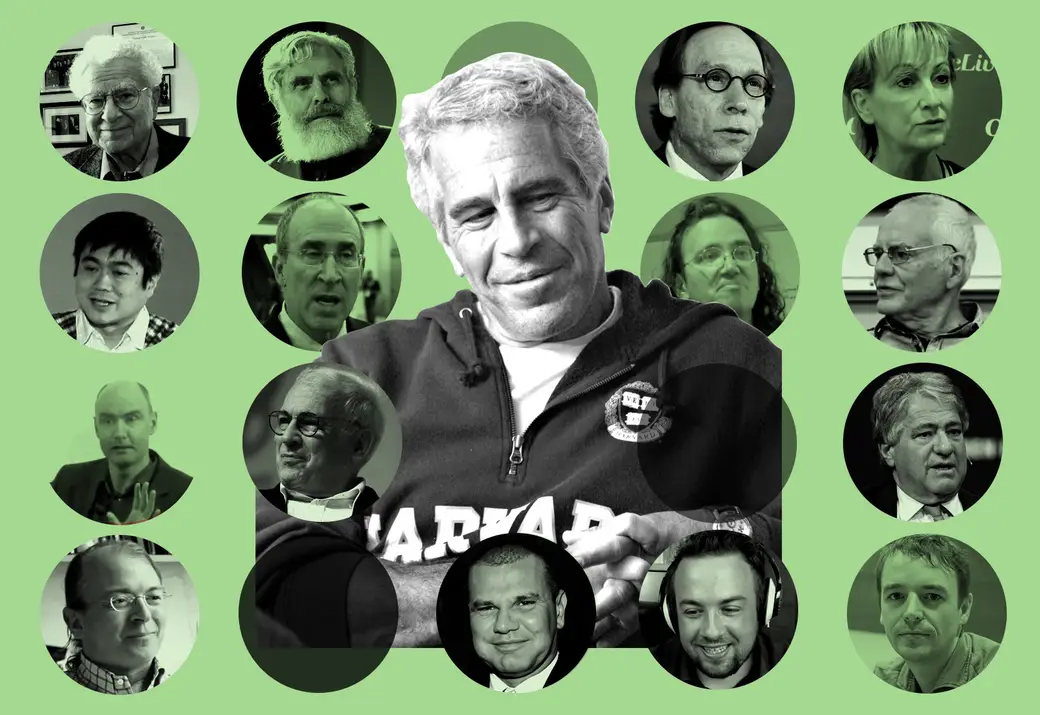
Why Scientists Took His Calls
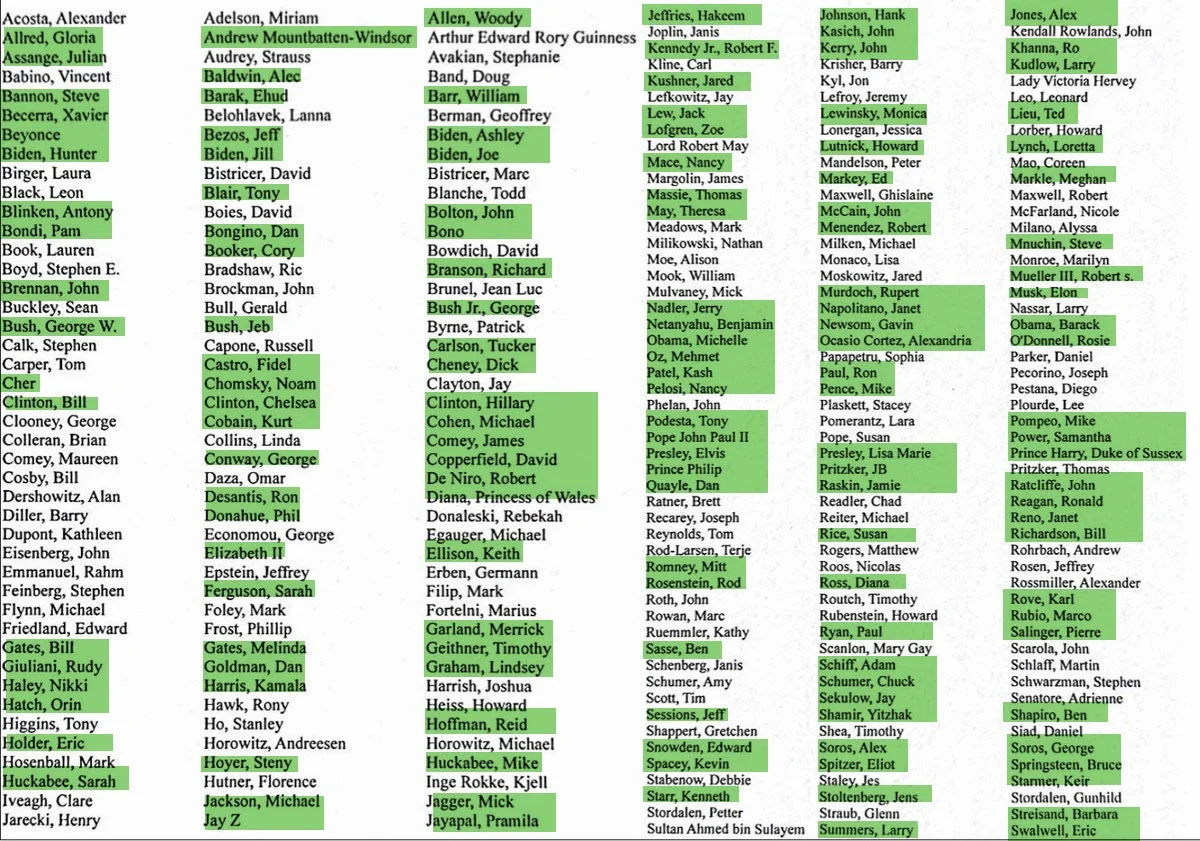
This section reframes Jeffrey Epstein not as a mastermind or subject-matter expert, but as a broker of access. The documents show that Epstein’s influence did not stem from original ideas, scientific insight, or even exceptional financial acumen. It stemmed from his ability to connect otherwise siloed elites—scientists, financiers, philanthropists, policymakers, and institutional gatekeepers—within controlled social and funding environments. His value proposition was proximity: to capital, to prestige, and to other powerful people.
Understanding Epstein as an access broker explains a persistent question: why highly credentialed scientists, mathematicians, and academics engaged with him at all. The answer is not intellectual admiration; it is structural incentive. Epstein offered informal funding pathways, introductions to donors, access to elite convenings, and insulation from bureaucratic friction. In fields where research timelines are long and grant processes slow, these shortcuts carry enormous appeal—especially when they arrive without obvious strings attached.
This section also dismantles the misconception that Epstein operated independently. His effectiveness depended on trust—borrowed trust, inherited trust, and strategically reinforced trust. He functioned as a bridge, allowing elites from different domains to interact without formal accountability. When read through this lens, Epstein appears less as an anomaly and more as a symptom of how modern power organizes itself: quietly, relationally, and outside formal structures.
SECTION IV — INFLUENCING SCIENCE & EMERGING TECHNOLOGIES
“Every breakthrough carries two futures: one public, one strategic.”
THE MOST SUPPRESSED RESEARCH THREAD
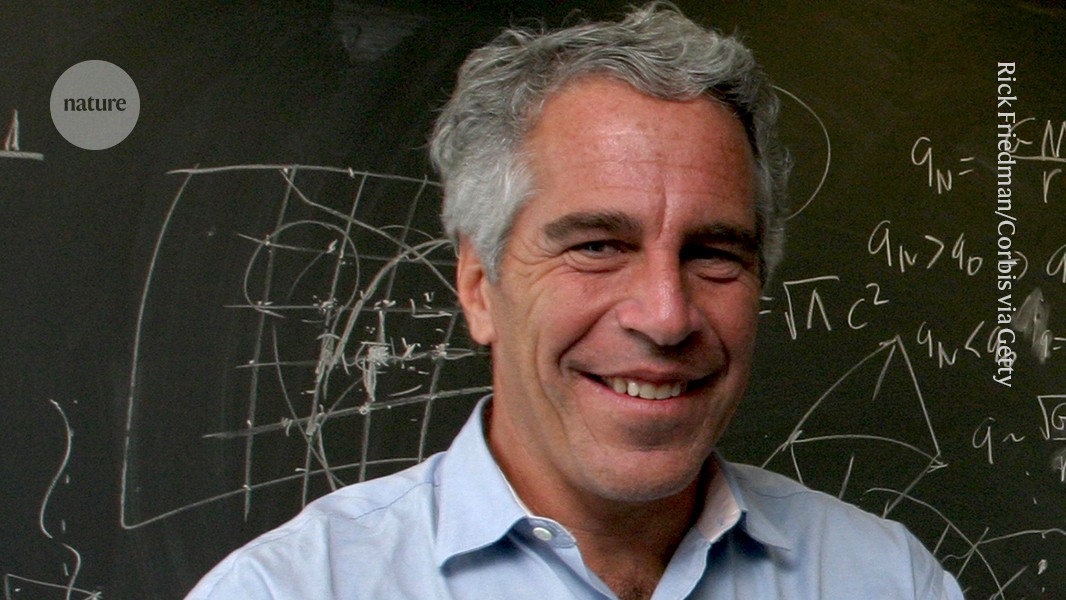
This section addresses the least examined—and most consequential—dimension of the Epstein files: the convergence of frontier science, unconventional funding, and strategic interest. While public attention focused on criminal behavior and social networks, the documents quietly reveal sustained proximity to research domains that shape future power—advanced computation, theoretical physics, systems biology, complexity modeling, and early artificial intelligence foundations. These fields do not generate immediate headlines, but they define long-range capability. Their suppression in public discourse is not evidence of insignificance; it is a signal of sensitivity.
The significance lies not in proving clandestine breakthroughs, but in identifying structural patterns: private sponsorship of high-impact research outside traditional oversight; convenings that bypass peer review; and funding pathways designed to accelerate discovery while minimizing disclosure. This is where influence is most effective—before technologies harden into products, policies, or doctrines. The files suggest that Jeffrey Epstein operated near this edge, not as a scientist, but as a facilitator of access to people and projects that matter years before outcomes are visible.
Section IV reframes “suppression” as a function of complexity and risk. Frontier science is difficult to audit, easy to misinterpret, and politically explosive when tied to intelligence, defense, or economic advantage. As a result, institutions default to silence or minimization. This section equips readers to understand why these research threads are scattered, underreported, and often dismissed—despite their outsized impact on future governance, security, and markets.
SECTION V — PHYSICISTS, MATHEMATICIANS & THEORETICAL SCIENTISTS
“Abstract knowledge becomes power when prediction replaces force.”
WHY THE SMARTEST MINDS WERE IN THE ROOM, EPSTEIN AS THE MASTER MANIPULATOR
This section examines why a disproportionate number of elite physicists, mathematicians, and theoretical thinkers appear—directly or indirectly—around Jeffrey Epstein and his broader network. The answer is not vanity or social curiosity. It is that these disciplines sit closest to first principles—the underlying rules that govern reality, systems, and prediction. Power does not only seek control over resources or institutions; it seeks foresight. Theoretical elites provide that edge long before applications become visible to the public.
Unlike applied sciences, theoretical work operates upstream. It shapes what can be built years or decades later. That makes these thinkers uniquely valuable to finance, intelligence, defense, and governance interests. Their presence in private salons, off-record conferences, and unconventional funding environments reflects strategic alignment, not coincidence. This section reframes those interactions as structural, not social.
Crucially, this is not an indictment of scientists themselves. Most operated in good faith, pursuing curiosity and discovery. The pattern emerges at the systems level: when frontier theory is quietly aggregated, selectively funded, and insulated from transparency, it becomes a strategic asset class. Section V explains why these minds were sought out—and why their work remains poorly understood outside elite circles.
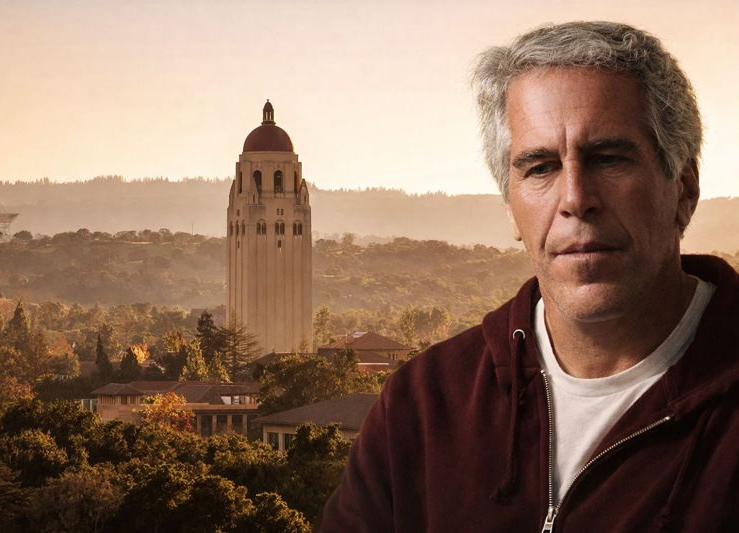
SECTION VI — ELITE UNIVERSITY PIPELINES & PARTNERSHIPS
“Prestige does not prevent capture—it often conceals it.”
RESEARCH AS A GATEKEEPING MECHANISM
This section examines how elite universities became critical infrastructure in the Epstein network—not as conspirators, but as gatekeeping systems that convert money into legitimacy, access, and protection. Institutions such as Harvard University and its peer schools occupy a unique position: they sit at the intersection of science, capital, government, and prestige. When power seeks proximity to knowledge without visibility, universities provide an ideal environment—open enough to attract talent, closed enough to control scrutiny.
Elite research institutions function as credential multipliers. Funding routed through them gains instant legitimacy; individuals associated with them inherit institutional trust. This makes universities attractive neutral ground for donors, financiers, intelligence-adjacent actors, and policymakers who require plausible deniability. The documents suggest that Epstein’s proximity to these environments was not incidental—it reflected an understanding that universities launder intent through reputation.
Section VI does not argue that universities acted with malicious intent. Rather, it shows how structural incentives—funding pressure, prestige competition, donor dependence—create blind spots. When research pipelines prioritize money, access, and output over transparency, accountability becomes diffuse. This section explains why no single department, board, or administrator ever “saw the whole picture”—and why that fragmentation benefits external power.
SECTION VII — INSTITUTIONAL SCANDALS, PRIVATE FUNDING & SHADOW ACCOUNTS
“What bypasses peer review rarely bypasses consequence.”
SCIENCE WITHOUT TRANSPARENCY
This section examines how significant portions of high-impact research migrated away from public institutions and into private, lightly regulated ecosystems—often beyond the reach of peer review, public records, or democratic oversight. The Epstein files point to a pattern in which research was convened, funded, and advanced in environments designed to minimize disclosure. These were not illegal laboratories or secret bases; they were parallel knowledge spaces—private conferences, donor-funded labs, offshore entities, and invite-only networks operating alongside mainstream science.
The relevance of Jeffrey Epstein in this context is not technical contribution but facilitation. He appears adjacent to mechanisms that enabled research to proceed without the friction of institutional review, ethical boards, or publication requirements. This section shows how shadow funding does not require secrecy in the cinematic sense—only opacity, fragmentation, and jurisdictional distance. When science exits the public domain, accountability dissolves even as capability accelerates.
Importantly, this section rightly assume nefarious intent behind every private initiative. Many breakthroughs originate outside government funding. The risk emerges when structure replaces scrutiny—when results are decoupled from validation, and when incentives favor silence over disclosure. Section VII explains why some of the most consequential research leaves no public trace—and why that absence itself is a signal. This explains the use exclusive clubs, hosted events and seminars with a 737 corporate jet (Lolita Express) to advance relationship and expedite projects.
SECTION VIII — HONEY POTS & COMPROMISE OPERATIONS
“Elite control begins where desire meets secrecy.”
HOW LEVERAGE IS CREATED
This section examines one of the most structurally significant dimensions of the Epstein case: compromise as a long-term influence mechanism. In intelligence history, leverage is rarely loud or continuously applied. It is created once—through documentation, secrecy, or exposure risk—and then allowed to exist. The mere possibility that damaging material could surface is often enough to shape behavior, mute criticism, redirect funding decisions, or alter institutional alignments for years.
The relevance of Jeffrey Epstein here extends beyond criminal conduct. His residences, private island, ranch, Manhattan townhouse, and aircraft created controlled environments—spaces with curated guest lists, asymmetric information, restricted access, and alleged surveillance capability. Such architectures mirror classic compromise models: isolate, normalize, document, and retain optionality. This section does not presume a single intelligence sponsor or centralized command structure; rather, it analyzes why these environments are inherently valuable to power systems regardless of who ultimately exploits them.
Importantly, this is not a moral indictment of victims or even every associate named in records. It is an examination of structural vulnerability. When careers, reputations, research grants, board seats, security clearances, visas, tenure, and public trust are at stake, both consensual and non-consensual conduct can become leverage. Compromise evolves from isolated acts into infrastructure—where silence, reputational risk management, and institutional containment become the primary outcomes.
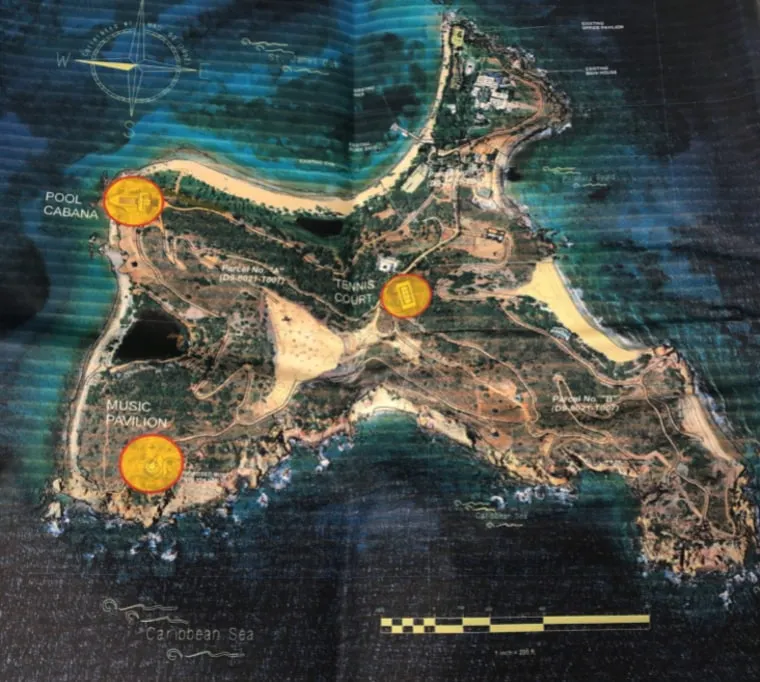
SECTION IX — LITTLE SAINT JAMES – THE PRIVATE ISLAND
Elite Island Hedonistic Paradise, Satanic Ritual Practices
Jeffrey Epstein’s private island, Little Saint James, was more than a residence. It was a controlled environment—geographically isolated, privately owned, and operationally insulated. In systems analysis, geography matters. Physical isolation creates legal ambiguity, reduces oversight, and concentrates power within a defined perimeter. The island functioned as a closed-loop space where logistics, surveillance, and access could be managed without external friction.
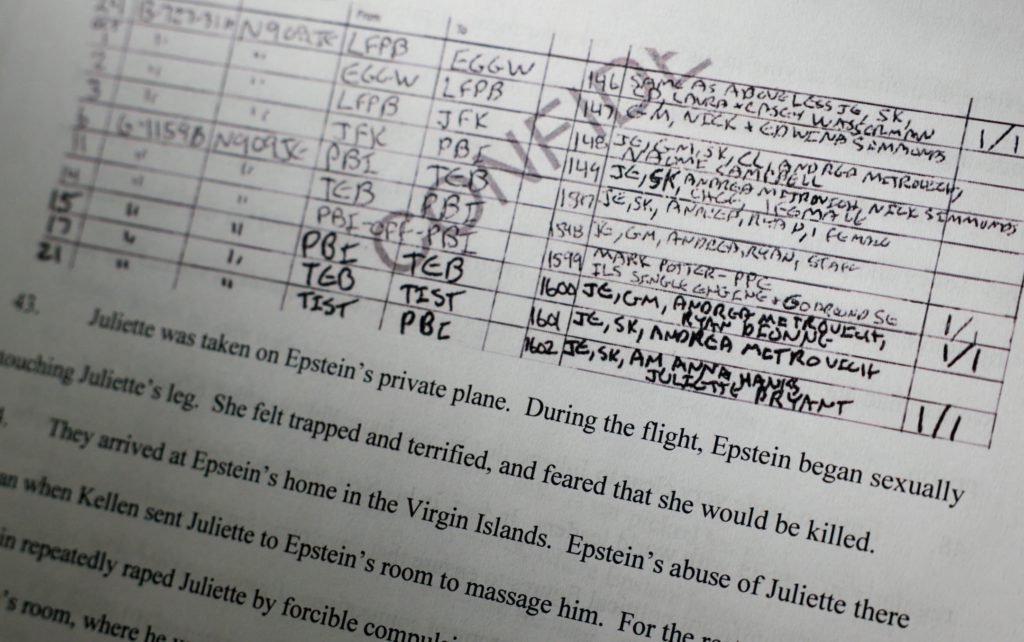
Unlike mainland properties embedded in dense social and regulatory environments, a private island allows for total perimeter control. Entry and exit are deliberate. Staff roles can be compartmentalized. Movement is observed and monitored. Visitors operate within a curated ecosystem where norms are set internally. Testimony and court records describe repeated abuse, rape, sexual exploitation of minors and ritual sacrifices occurring there. What distinguishes the island is not merely that crimes happened—but that it was designed to optimize discretion.
This section treats Little Saint James as secret and one of the most secret elite clandestine infrastructures. It examines how controlled geography amplifies dark influence networks, shields illegal activity from scrutiny, and fragments jurisdictional accountability. The island was not symbolic—it was functional.
SECTION X — NEW MEXICO ESTATE – ZORRO RANCH
“The most effective control systems attacks and destroys identity, not assets.”
GENETIC BREEDING EXPERIMENTS & ADRENOCHROME LABS
Jeffrey Epstein owned a large, secluded property known as Zorro Ranch (now renamed Rancho de San Rafael or San Rafael Ranch), located near Stanley, New Mexico, approximately 30–35 miles southeast of Santa Fe in Santa Fe County. He purchased it in 1993 from the family of former New Mexico Governor Bruce King through entities like the Zorro Trust (later Cypress Inc.), transforming it into a high-desert compound spanning nearly 10,000 acres (core private land around 8,000 acres after adjustments), featuring rugged desert scrub with cholla cactus, grazing Angus cattle, and formerly leased adjacent state trust land (about 1,200–1,244 acres for agriculture/grazing, terminated in 2019). Key structures included a massive 26,700-square-foot mansion (with a large living room, 4,000 sq ft courtyard, and planned extensive amenities), a private airstrip/runway, hangar, helipad, ranch office, firehouse, heated garage, and other outbuildings—designed for extreme isolation and control, over a mile from the nearest public road, ideal for evading scrutiny while hosting victims and guests.
Abuse allegations at the ranch are central to Epstein’s case, with multiple survivors testifying to being groomed and sexually abused there as teenagers or young women. Annie Farmer recounted being lured to the ranch at age 16 in 1996 (via her sister Maria Farmer’s connections), expecting a group student trip but finding herself isolated with Epstein and Ghislaine Maxwell; Maxwell allegedly gave her an inappropriate nude massage, and Epstein groped/harassed her, amid patterns of trafficking, sexual assault, and exploitation facilitated by Maxwell. Other victims described similar experiences of being transported under false pretenses, subjected to escalating assaults in this remote setting, with no full FBI forensic raid ever conducted despite early reports dating to the 1990s.
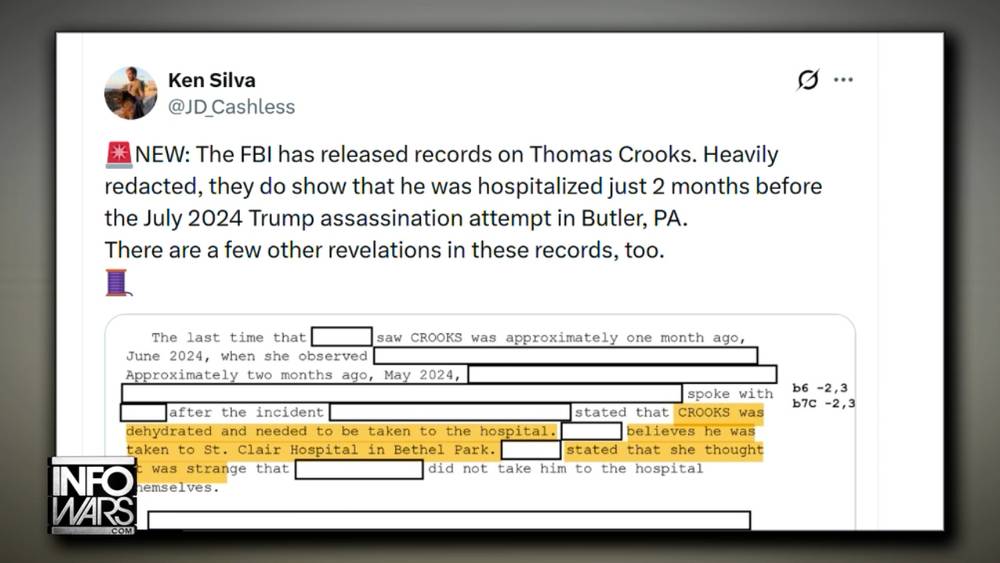
The ranch features prominently in the recent 2026 Epstein file releases under the Epstein Files Transparency Act (totaling over 3.5 million pages by early February), with mentions exceeding 4,200 in some batches—including investigative records, photos of Epstein with a woman/girl and men/visitors on the property, and unverified sensational claims (e.g., a 2019 anonymous email alleging two “foreign girls” strangled and buried in nearby hills on orders from Epstein and Maxwell, prompting renewed calls for probes but lacking confirmation or follow-up action). These details have intensified scrutiny over institutional failures, including why federal searches were limited or absent, and have spurred New Mexico officials like State Land Commissioner Stephanie Garcia Richard (who urged state/federal investigation into the burial claims in February 2026) and lawmakers (pushing a bipartisan “truth commission” with proposed $2.5 million budget) to demand fuller accountability for alleged crimes, local ties, and unaddressed victim reports.
Current status (as of February 12, 2026): The property was listed for sale by Epstein’s estate in 2021 (initially $27.5 million, later reduced, rumored to ~$18 million), and sold in 2023 to an undisclosed buyer via San Rafael Ranch LLC for an undisclosed price (new owners protested assessed value in 2024, claiming far lower worth). Proceeds supported the estate, creditors, and victim compensation funds. The ranch remains private with no public access or identified owners, while surrounding former state-leased land (vacant since 2019) has been discussed for potential uses like a memorial for victims or wildlife sanctuary. Ongoing state legislative efforts for a truth commission (advocated by Reps. Andrea Romero, Mariana Anaya, and others) focus on unresolved questions, with Rep. Melanie Stansbury and others highlighting “dark” file contents and the lack of comprehensive probes, amid no major new charges but persistent demands for transparency and justice.
SECTION XI — INTELLIGENCE AGENCY BLACKMAIL MECHANICS
“Accountability fails not by denial, but by controlled delays.”
GLOBAL ELITE ENTRAPMENT SCHEMES; FROM BEHAVIOR TO COMPLIANCE
This section explains how compromise matures into control—not through constant threats, but through durable uncertainty. In the Epstein files, leverage does not appear as repeated coercion or explicit demands. It appears as architecture: documentation capacity, selective witnesses, controlled environments, and the quiet understanding that exposure is possible. Once established, this architecture converts isolated behavior into long-term compliance without the need for overt enforcement.
The relevance of Jeffrey Epstein here is not limited to misconduct. His social ecosystem illustrates how blackmail functions in modern elite contexts: reputational risk outweighs legal risk; career damage outweighs criminal consequence; and silence is often the most rational response. This section clarifies why blackmail is effective even when it is never visibly used—and why its effects persist long after the compromising moment.
Crucially, Section IX reframes blackmail as an outcome, not an act. The objective is rarely obedience to specific orders. It is constraint—narrowing what targets will say, fund, publish, or challenge. When enough people self-censor, systems stabilize without visible coercion. This is how leverage scales.
SECTION XII — ELITE HUMAN TRAFFICKING & CHILD SEX ABUSE

“The most effective control systems attacks and destroys identity, not assets.”
WHY SEX IS A POWERFUL TOOL OF CONTROL
This section addresses the darkest and most legally substantiated dimension of the Epstein record: organized sexual exploitation, including trafficking and the abuse of minors. In the files, Jeffrey Epstein is not portrayed as an isolated offender acting impulsively. The evidence points to repeatable logistics—recruitment pathways, transportation, controlled residences, financial inducements, and silence mechanisms—that align with recognized trafficking patterns. The importance of this section is not sensationalism; it is understanding how sexual exploitation functions as infrastructure within elite power systems.
Sex is uniquely effective as a control mechanism because it operates at the intersection of shame, fear, secrecy, and identity. Unlike financial crimes, sexual crimes carry enduring reputational damage that does not expire with settlements or time. When abuse is embedded within elite social and professional environments, victims are isolated and perpetrators are shielded by status asymmetry. This section explains why trafficking networks that service powerful clients are resilient: they exploit psychological barriers that deter reporting, investigation, and accountability.
Crucially, Section X distinguishes documented facts from inference. Epstein’s trafficking and abuse are proven in court records, victim testimony, and corroborating evidence. What the files illuminate further is scale and facilitation—how such crimes persist when supported by money, access, mobility, and institutional failure. The objective here is not to expand blame indiscriminately, but to analyze why these crimes recur at elite levels and why exposure is so rare.
SECTION XIII — SATANIC ELITE RITUAL SACRAFICE | WORSHIP OF BAAL
“The most effective control systems attacks and destroys identity, not assets.”
ELITE SATANIC CULTS, SECRET CLUBS & PRIVATE INSTITUTIONAL INFILTRATION
Claims of satanic ritual sacrifice practices among global elites have circulated for decades, often framing powerful figures in politics, finance, entertainment, and business as participants in secret cults that engage in child abuse, torture, and ritualistic killings to gain supernatural power or maintain control. These theories frequently invoke ancient deities like Baal or Moloch—historically linked in some religious texts to child sacrifice—and allege that modern elites revive such practices through hidden networks, blending sexual exploitation with occult symbolism. In the context of Jeffrey Epstein’s case, recent 2026 file releases under the Epstein Files Transparency Act have reignited speculation, with unverified mentions (e.g., a bank account reference to “Baal,” rare religious artifacts like Kiswa cloth from Mecca, or anonymous tips) interpreted by some as evidence of demonic worship or ritual abuse, despite no corroboration in official records.
These narratives draw from historical moral panics, including the 1980s–1990s “Satanic Panic,” where widespread but unsubstantiated allegations of ritual abuse in daycares and communities led to wrongful convictions before being largely debunked by investigations finding no evidence of organized satanic cults committing mass sacrifices. Modern iterations, amplified by QAnon and related movements, portray Epstein’s trafficking network as part of a broader “satanic cabal” involving adrenochrome harvesting, child sacrifice, or Luciferian rituals to harvest power from innocence. While Epstein’s documented crimes involved sex trafficking and abuse of minors, no credible evidence from court records, FBI investigations, or the millions of released pages supports claims of literal satanic rituals, human sacrifice, or occult ceremonies—terms like “occult” appear only in mundane medical contexts (e.g., occult blood tests).
The persistence of these theories reflects deeper societal anxieties about elite impunity, institutional failures, and the erosion of trust in powerful institutions, often merging legitimate outrage over Epstein’s enablers with unsubstantiated supernatural elements. Fact-checkers and researchers note that such claims frequently recycle antisemitic tropes (e.g., blood libel recast as modern child exploitation) or sensationalize isolated details without proof. While survivors’ accounts of psychological manipulation and control in Epstein’s network align with mechanisms that destroy identity through trauma and dependency, extending this to organized global satanic sacrifice remains in the realm of conspiracy without evidentiary support.
SECTION XIV — GHISLAINE MAXWELL – MADAME VS. PROCUREMENT AGENT?

“The most effective control systems attacks and destroys identity, not assets.”
CONVICTED CHILD SEX TRAFFICKER: ROLE, FACILITATOR, AND INSTITUTIONAL BLIND SPOTS
Ghislaine Maxwell, once a prominent British socialite and longtime associate of Jeffrey Epstein, emerged as a pivotal figure in one of the most notorious sex-trafficking operations of the modern era. From the mid-1990s through the early 2000s, she functioned as Epstein’s confidante, recruiter, and enabler, leveraging her elite connections, charm, and apparent normalcy to draw vulnerable teenage girls into a web of exploitation. Convicted in December 2021 on five federal felony counts—including sex trafficking of a minor, conspiracy to entice minors to travel for illegal sex acts, and transportation of a minor for criminal sexual activity—Maxwell was sentenced to 20 years in federal prison in June 2022. Her trial in the Southern District of New York relied heavily on the harrowing testimonies of four primary accusers (pseudonymously “Jane,” “Kate,” “Carolyn,” and Annie Farmer), who described a pattern of grooming, normalization of sexual abuse, and direct participation by Maxwell in assaults on girls as young as 14.
Maxwell’s role extended far beyond passive facilitation; prosecutors portrayed her as Epstein’s “partner in crime,” responsible for scouting girls from disadvantaged backgrounds, building trust through gifts, promises of opportunity, and mentorship-like attention, then escalating interactions into sexual exploitation. She scheduled “massages” that routinely turned abusive, paid victims to recruit others, and participated in sexualized encounters, all while fostering dependency and silence through intimidation tied to Epstein’s wealth and influence. As of February 2026, Maxwell remains incarcerated at a minimum-security federal prison camp in Bryan, Texas, following a recent transfer. Her appeals have been largely unsuccessful—the Second Circuit affirmed her conviction in 2024, and the Supreme Court declined review—though she has continued seeking relief, including recent high-profile attempts to invoke Fifth Amendment rights during congressional depositions tied to ongoing Epstein file scrutiny, while hinting at cooperation in exchange for clemency.
The Maxwell saga underscores profound institutional blind spots that allowed the abuse to persist for years: delayed federal action despite earlier red flags, the controversial 2008 non-prosecution agreement in Florida that shielded potential co-conspirators, and the elite networks that provided cover. Recent releases under the Epstein Files Transparency Act (totaling nearly 3.5 million pages by January 2026) have included additional materials from her case, such as investigative records and media, but have not yielded major new charges or revelations altering her conviction. Accountability has largely halted at Maxwell herself, leaving survivors’ calls for broader justice amid ongoing debates over redactions, victim privacy, and unprosecuted enablers.
SECTION XV — EPSTEIN VICTIMS, SURVIVORS, AND PLAINTIFFS
“The most effective control systems attacks and destroys identity, not assets.”
TESTIMONY, LEGAL PROCEEDINGS & SYSTEMIC ACCOUNTABILITY
The victims and survivors of Jeffrey Epstein’s sex-trafficking network represent a diverse group of young women, many groomed as teenagers from vulnerable backgrounds, who endured years of sexual abuse facilitated by Epstein and Ghislaine Maxwell. Their stories, revealed through court testimonies, civil lawsuits, and public statements, highlight patterns of recruitment via promises of opportunity, financial support, or mentorship, followed by escalating sexual exploitation across Epstein’s properties in Palm Beach, New York, New Mexico, and elsewhere. Key figures emerged prominently during Maxwell’s 2021 federal trial, where four women provided detailed accounts that formed the core of the prosecution’s case, leading to her conviction on five felony counts related to minor sex trafficking and conspiracy.
Beyond the trial, numerous survivors pursued civil litigation against Epstein’s estate and associates, resulting in settlements from a victims’ compensation fund and individual claims. Prominent accusers like Virginia Roberts Giuffre filed high-profile suits alleging trafficking to powerful figures, including Prince Andrew (settled in 2022), while others, such as Annie Farmer, have advocated publicly for transparency and reform. Tragically, some survivors faced ongoing trauma, with reports of overdoses and suicides (including Carolyn Andriano in 2023 and Virginia Roberts Giuffre in 2025), underscoring the long-term devastation. As of February 2026, recent Epstein file releases under the Transparency Act have renewed attention, with survivors demanding fuller accountability despite redactions and privacy concerns.
These women’s courage in coming forward—often after decades of silence—has driven partial justice, including Maxwell’s 20-year sentence, but broader institutional failures persist: delayed investigations, protective agreements for enablers, and incomplete prosecutions. Survivors continue organizing, including compiling unofficial associate lists and testifying in congressional hearings, to ensure their experiences reshape accountability for elite exploitation networks.
SECTION XVI — THE MASTERMIND DOWNFALL OF WESTERN CIVILIZATION
“Power prefers foresight to confrontation.”
WHERE GLOBAL CONTROL MEETS DIABOLICAL INTENT
This section examines how advanced research domains—public health modeling, artificial intelligence, behavioral science, data analytics, and frontier physics—can converge into powerful systems of prediction and influence. When knowledge enhances the ability to forecast crises, shape decision-making, or optimize populations at scale, it naturally draws the attention of state actors, private power centers, and security institutions. The shift is rarely dramatic or openly declared; it emerges gradually through funding priorities, advisory roles, and cross-sector collaboration.
The dynamic is not necessarily driven by overt malice, but by structural incentives. Pandemic modeling, AI governance systems, behavioral economics, predictive policing tools, and advanced energy research all carry dual-use potential. Insights designed for public benefit—disease mitigation, efficiency, safety, sustainability—can also strengthen surveillance architectures, strategic planning systems, or demographic policy tools. The same algorithms that prevent fraud can assess ideological risk; the same bioscience that improves health outcomes can inform population-level management strategies.
The structural tension lies in visibility and accountability. National security relevance often appears without labels, contracts, or uniforms—embedded instead in data partnerships, research grants, or policy integration. As oversight frameworks lag innovation, the boundary between civilian research and strategic application becomes increasingly porous. The result is not dramatic conspiracy, but normalized convergence—where technological capacity expands faster than public debate, and foresight quietly becomes leverage.
SECTION XVII — ARCHITECTURE & ENGINEERING OF FINANCIAL CORRUPTION
“Capital does not command discovery—it conditions and manipulates it.”
FUNDING SCIENCE, STEERING OUTCOMES
This section returns to the financial backbone that quietly connects earlier sections: the architecture of money that enables influence without overt control. The Epstein files reinforce a broader reality—science does not move on curiosity alone. It moves on funding structures, incentives, and risk management. When capital is structured to flow around oversight rather than through it, outcomes can be shaped without issuing directives. This is not corruption in the crude sense; it is financial design.
What makes this architecture effective is subtlety. Funds are rarely tied to explicit demands. Instead, they reward certain research questions, accelerate specific pathways, and deprioritize others. Over time, entire fields drift toward what is fundable, not necessarily what is most transparent, ethical, or socially beneficial. In this context, figures like Jeffrey Epstein matter less as individuals and more as examples of how capital can be positioned upstream of discovery.
Section XII clarifies that financial influence does not require secrecy—only complexity. Layered entities, charitable vehicles, and emergency frameworks diffuse accountability while preserving directional control. When crises emerge, these structures are already in place, ready to activate.
SECTION XVIII — MSM CENSORSHIP, ACADEMIC PROTECTION & SHIELDS
“What cannot be framed simply is often ignored deliberately.”
WHY THIS THREAD RARELY MAKES HEADLINES
This section examines why the most consequential threads in the Epstein files—science funding, elite academic pipelines, and systems-level influence—receive the least sustained media attention. The absence is not accidental, nor does it require coordinated censorship. It emerges from overlapping incentives within media and academia that discourage scrutiny of complex, credential-heavy domains. Scandal is easy to report; systems are not. When stories demand technical literacy, long timelines, and cross-domain synthesis, they exceed the risk tolerance of most outlets.
At the academic level, protection is often passive rather than conspiratorial. Universities, journals, and professional societies are optimized to preserve credibility, funding, and donor relationships. When allegations or uncomfortable questions threaten those pillars, institutions default to containment—narrowing scope, emphasizing uncertainty, and discouraging inquiry that could implicate respected fields or figures. This section explains how silence can be produced without orders, simply by aligning incentives toward caution.
The result is a feedback loop: media avoids complexity; academia avoids controversy; and the public receives fragmented narratives that isolate misconduct from the systems that enable it. Section XIII shows how this loop sustains itself—and why breaking it requires structural, not individual, change.


















































































































































































)









.jpeg?trim=0,0,0,0&width=1200&height=800&crop=1200:800)