Epstein Files Topic Titles
SECTION I — ORIENTATION
Why the Epstein Files Matter Now
- Why This Is a Systems Story, NOT a Crime Recap
- Why the Science Thread Was Ignored for Years
- The Risk of Treating Epstein as an Endpoint
- Volume as Obfuscation: How Truth Gets Lost
- Institutional Incentives to Avoid Pattern Recognition
- Epstein’s History and Hidden Background
SECTION II — FILES & DOCUMENTS; ARCHITECTURE OF DECEPTION
Understanding the Release
- Categories of DOJ Documents
- Financial vs. Behavioral vs. Scientific Records
- Redactions, Sealed Exhibits & Missing Data
- Why Scientific Correspondence Is Scattered
- How to Read Between Document Silos
- Final DOJ Classified Document Release
SECTION III — EPSTEIN AS AN EXCLUSIVE ACCESS BROKER
Why Scientists Took His Calls
- Epstein’s Role as a Non-Expert Intermediary
- Access to Capital, Not Ideas
- Why His Social Power Exceeded His Net Worth
- Epstein as a Trust Bridge Between Elites
- The Myth of the “Lone Self-made Financier”
- Famous Global Figures Connections Exposed
- Who Was Epstein’s Boss & Handlers?
SECTION IV — INFLUENCING SCIENCE & EMERGING TECHNOLOGIES
The Most Suppressed Research Thread
- Why Epstein Targeted Frontier Science
- Funding Outside Traditional Grant Oversight
- Dual-Use Research: Civilian vs. Strategic Applications
- Why These Fields Attract Intelligence Interest
- The Ethics Gap in Cutting-Edge Research
- Early Development of AI, Internet, Bitcoin, Genetics, and Technology
SECTION V — PHYSICISTS, MATHEMATICIANS & THEORETICAL SCIENTISTS
Why the Smartest Minds Were in the Room, Master Manipulator
- The Role of Theoretical Physics & Cosmology
- Advanced Mathematics, Modeling & Prediction Systems
- Complexity Theory, Chaos & System Control
- Artificial Intelligence Foundations (Pre-Boom Era)
- Why These Disciplines Matter to Power
- Leading Scientist Associations & Control
- Private Jets, Secret Clubs, Island, Ranch, NY Brownstone (Who’s Who)
SECTION VI — ELITE UNIVERSITY PIPELINES & PARTNERSHIPS
Research as a Gatekeeping Mechanism
- Ivy League Research Departments & Private Funding
- Why Universities Became Neutral Ground for Power
- Leverage; Grant Capture & Influence Without Oversight
- Academic Prestige as Legitimacy Shield
- Why Institutional Accountability Failed
- Epstein’s Grants, Donations, Private Partnerships, & Gov. Funding
- Physicians Who Are In the Epstein Files!
(Includes research programs connected to Harvard ,Yale, MIT, University and peer institutions)
SECTION VII — INSTITUTIONAL SCANDALS, PRIVATE FUNDING & SHADOW ACCOUNTS
Science Without Transparency
- Institutional Scandals, Fraud & Laundering Money Schemes
- Private Funding Strings & Coercion Strategies
- Private Conferences & Invite-Only Symposia
- Offshore Research Hidden Funding Channels
- Unpublished or Classified Research Outcomes
- When Peer Reviews Disappears
- Why Breakthroughs Remain Unnamed
SECTION VIII — HONEY POTS & COMPROMISE OPERATIONS
How Leverage Is Created
- Honey Pot Theory: Intelligence & Power History
- Sexual Compromise as Control Infrastructure
- Why Scientists Are High-Value Targets
- Consent vs. Coercion vs. Career Destruction
- Epstein’s Properties as Control Environments
Lolita Express Epstein Private Jet
- FAA Flight Logs Disclosure
- Witness Testimonies (flight attendants)
- Victim Reports (massage therapist)
- FBO Ground & Service Crew Reports
- Hidden Manifest
- Secret Flights
SECTION IX — LITTLE SAINT JAMES – THE PRIVATE ISLAND
Elite Island Hedonistic Paradise, Satanic Ritual Practices
- Who’s Who Guest List | “A” List Celebrities
- Exclusive Female & Male Guest, Couples
- Corporate Boondoggles Elite Leaders of Industry
- Top University Department Scientist & Scholars
- Global Financiers & Bankers
- Hidden Camera’s Everywhere, Zero Privacy
- Targets Selected Prior to Arrival
- What Happens on the Island, Never Stays on the Island?
SECTION X — NEW MEXICO ESTATE – ZORRO RANCH
Genetic Breeding Experiments & Adrenochrome Labs
- Military Industrial Complex Boondoggles
- National Acclaimed Scientists and Top U.S. Physicists
- Main Compound 28,000 sf Estate
- Private Jet Airstrip
- Superconducting Maglev Trains Connects to Gov. Facilities
- Los Alamos Laboratories Partnerships
- Sandia National Laboratories
- Major Underground Facility
- Human Genetic Breeding Programs
- Secret Cloning Labs
- Adrenochrome Facilities
SECTION XI — INTELLIGENCE AGENCY BLACKMAIL MECHANICS
Global Elite Entrapment Schemes; From Behavior to Compliance
- How Information Becomes Leverage
- Digital Evidence, Witnesses & Plausible Deniability
- Why Blackmail Doesn’t Require Constant Use
- Self-Censorship as the Real Outcome
- Silence as a Survival Strategy
- Files Expose Top Global Elites (identified)
- Israeli Intelligence Connections
SECTION XII — ELITE HUMAN TRAFFICKING & CHILD SEX ABUSE
Why Sex Is a Powerful Tool of Control
- Sexual Exploitation as a Control Mechanism
- Trafficking as a System, Not an Accident
- Jurisdiction Hopping & Legal Evasion
- Financial Inducements & Dependency
- Institutional Failure & Shielding Effects
- Silencing Mechanisms: NDAs, Settlements, and Intimidation
- Victim Impact & Long-Term Harm
- Why Exposure Is Rare—and Why It Matters
XIII. SATANIC ELITE RITUAL SACRIFICE | WORSHIP OF BAAL’
Elite Satanic Cults, Secret Clubs & Private Institutional Infiltration
- Luciferian vs. Modern Satanism
- Ritual Practices & Transgressive Symbolism
- Power Acquisition & Elite Networking
- Archetypes of “Demonic Entities”
- Baal & Ancient Ritual Symbolism
- Evidence Classification Protocol
SECTION XIV — GHISLAINE MAXWELL — MADAME VS. PROCUREMENT AGENT?
Role, Facilitation, and Institutional Blind Spots
- The Facilitator, Not the Figurehead
- Recruitment, Grooming & Normalization
- Enforcement Through Trust & Threat
- Social Engineering of Silence
- Elite Proximity & Protective Shielding
- Legal Focus Narrowed to One Actor
- Missing Accountability: Clients & Beneficiaries
- Why Her Conviction Was Necessary—but Insufficient
- Structural Lesson in Elite Child Sex Trafficking
SECTION XV — EPSTEIN VICTIMS, SURVIVORS, AND PLAINTIFFS
Testimony, Legal Proceedings & Systemic Accountability
- Documented Victim Testimonies
- Civil Lawsuits & Plaintiff Classifications
- Criminal Charges & Federal Prosecution
- Financial Settlements & Compensation Funds
- Institutional Failures
- Survivor Advocacy & Trauma Recovery
- Sealed Records & Ongoing Litigation
- Public Figures Named vs. Charged
SECTION XVI — THE MASTERMIND DOWNFALL OF WESTERN CIVILIZATION
Where Global Control Meets Diabolical Intent
- Pandemic Modeling & Bio-Systems Research
- Artificial Intelligence & Predictive Governance
- Human Behavior Modeling & Decision Theory
- Human Data Collection, Patterns, & Pre-crime
- Energy, Materials & Exotic Physics
- Why National Security Appears Without Labels
- Eugenics & Population Control
- Cryonics & Transhumanism
SECTION XVII — ARCHITECTURE & ENGINEERING OF FINANCIAL CORRUPTION
Funding Science, Steering Outcomes
- Donor-Advised Funds & Research Influence
- Philanthropy as Risk Shield
- Financial Incentives Embedded in Discovery
- Crisis Monetization & Preparedness Markets
- When Science Serves Capital First
- Global Money Laundering & Hiding $$$ Schemes
- 501.c3 Foundations Used as Front Operations
SECTION XVIII — MSM CENSORSHIP, ACADEMIC PROTECTION & SHIELDS
Why This Thread Rarely Makes Headlines
- The “Too Smart to Question” Bias
- Credential Protection & Career Risk
- Why Journalists Avoid Scientific Complexity
- Narrative Containment Strategies
- Manufactured Disinterest
- Censorship of True Facts & False Stories
SECTION XIX — LAWFARE & INSTITUTIONAL FIREWALLS
Why No One Wants Discovery or Exposure
- Weaponization of Legal System
- Limited Liability Exposure in Scientific Funding
- Civil Settlements & NDA Culture
- Why Universities Avoid Court
- The Risk of Precedent
- Structural Immunity
SECTION XX — EMERGING PATTERNS OF GLOBAL NETWORK
What the Files Reveal Collectively
- Science as a Strategic Asset
- Intelligence Interest Without Fingerprints
- Power Prefers Prediction Over Force
- Control Through Access, Not Orders
- Why This Model Persists
- Key Individuals Involved In Epstein’s Cover-Up
SECTION XXI — QUESTIONS STILL UNANSWERED
The Most Dangerous Unknowns
- What Research Was Never Published?
- What Discoveries Changed Policy Quietly?
- Who Retained Data Control?
- What Technologies Were Shelved—or Weaponized?
- Why Epstein Was Protected for So Long
- Growing Public Awareness of Adrenochrome Production Networks
- Organ Transplant Exploitation & Illicit Trafficking Risks
- Human Trafficking Beyond Sexual Exploitation
- Existing Laboratories of Human Cloning or Experimental Human Research
- Bioweapons Research & Classified Bio-Labs
- Allegations of Human Breeding Farms or Controlled Population Experiments
- Genetic Engineering Research & Transhuman Future Race
- New Evidence Epstein is Still Alive?
- Epstein’s Marriage Proposal Karina SulIak? Assets Left to Her in the Will?
SECTION XXII — DISCLOSURE ORIENTATION FOR TRUTH SEEKERS
Disclosure Without Discipline Becomes Noise.
- How GAR Handles High-Risk Research
- Evidence vs. Inference Discipline
- Avoiding Hero-Villain Simplification
- Emotional Regulation in Dark Material
- Why Precision Matters More Than Outrage
- Staying Grounded While Investigating Power
APPENDICES (Living)
- Appendix A: Scientific Fields Referenced
- Appendix B: Funding Structures Glossary
- Appendix C: Known & Suspected Research Venues
- Appendix D: Methodology & Source Integrity
EPSTEIN FILES RELEASE | 3 MILLION PAGE DISCLOSURE AUDIO REVIEW
“The story is not the individual. The story is the architecture.”
In this audio review, we walk through the key themes of our special report, 3 Million Page Disclosure: The Architecture of Power Behind the Scandal, explaining why the release of millions of Epstein-related documents represents more than renewed attention to a past crime—it marks a systems exposure event. Rather than focusing on personalities or shock value, we examine patterns that emerge across finance, academia, philanthropy, scientific funding, legal structures, and media incentives when the records are read collectively and contextually. The discussion outlines the methodological discipline required to navigate a disclosure of this scale—separating verified record from inference, behavior from intent, and coincidence from pattern—while emphasizing orientation over outrage. The goal is clarity: to understand how modern power embeds itself through networks, incentives, and normalization, and why this moment of disclosure matters now.
PODCAST REVIEW | SPECIAL REPORT: Epstein Files Release | 3 Million Page Disclosure
“Disclosure is not the fall of one man; it is the unveiling of the architecture that sustained him.”
In addition to the audio podcast, we are providing a broader overview of the report in video format. In this video walkthrough of our Special Report: Epstein Files Release — 3 Million Page Disclosure, we frame the document release not as a scandal recap, but as a systems exposure event. Rather than rehashing crimes already established, the discussion maps the architecture of modern power—how finance, academia, philanthropy, science, media, and legal structures intersect through access, funding, credentialing, and silence. The central thesis remains clear: Epstein was not the system—he was a node within it. The video emphasizes that three million pages do not automatically equal transparency; without structure, scale becomes fragmentation. We outline how disciplined truth seekers must approach the material methodologically—distinguishing verified fact from inference, separating behavior from structural design, and recognizing recurring patterns of distributed influence that persist quietly across sectors. As with the written report and audio review, the goal is orientation, not outrage—clarity over sensationalism, and elevated discernment as disclosure unfolds.
SECTION I — ORIENTATION
“Scandal explains behavior. Systems explain premeditated persistence.”
Why the Epstein Files Matter Now
The release of roughly three million pages of DOJ material related to Jeffrey Epstein is not significant because it adds shock value to a story the public already finds disturbing. It matters because the context has changed. For years, the Epstein case was framed narrowly—criminal acts, moral outrage, isolated enablers. What was missing was systems-level scrutiny. The current release arrives at a moment when trust in institutions, finance, media, science, and governance is already eroding. In that environment, documents are no longer read for scandal alone, but for structure: who interacted with whom, through what mechanisms, and to what long-term effect.
This section establishes a critical reframing. The Epstein files are not a conclusion; they are a cross-sectional snapshot of elite coordination across finance, philanthropy, academia, technology, intelligence-adjacent spaces, and global policy networks. Epstein himself functioned less as an originator and more as an access broker—a facilitator who sat at the intersection of capital, influence, and vulnerable ambition. When read correctly, the files illuminate how power moves quietly: through funding pathways, social proximity, credentialed environments, and informal leverage rather than overt command. Orientation, therefore, is about resisting the temptation to collapse the story into villains and instead tracking systems that outlive individuals.
Finally, this section defines how the report must be read. Volume is not transparency. The sheer scale of the document dump risks overwhelming analysis and fragmenting attention—what GAR terms signal saturation. Section I sets the methodological discipline for everything that follows: separating verified records from inference, behavior from intent, and coincidence from pattern. The goal is not accusation, but comprehension. If these files reveal anything enduring, it is that modern power rarely announces itself. It embeds. Orientation is the act of learning to see that embedding clearly—without fear, without sensationalism, and without losing precision.
Why the Epstein Files Matter Now
1. Why This Is a Systems Story, Not a Crime Recap
The crimes associated with Jeffrey Epstein are real, documented, and reprehensible—but they are not analytically sufficient to explain the scope of what the files reveal. Focusing exclusively on criminal acts collapses the story into individual pathology and moral failure. A systems lens, by contrast, examines how finance, academia, philanthropy, intelligence-adjacent networks, and governance structures intersected around Epstein and continued functioning before, during, and after his prosecution. Crimes expose individuals; systems explain persistence.
2. Why the Science Thread Was Ignored for Years
Epstein’s proximity to elite scientists, mathematicians, and research institutions was long dismissed as eccentric patronage or social curiosity. That dismissal served as a convenient filter: science is complex, technical, and intimidating to interrogate publicly. As a result, media and legal scrutiny gravitated toward salacious details rather than examining why frontier research—physics, biology, AI foundations, complexity modeling—was being privately funded outside normal oversight. The science thread was ignored not because it was unimportant, but because it was difficult and potentially destabilizing to examine.
3. The Risk of Treating Epstein as an Endpoint
Positioning Epstein as the final villain creates false closure. It implies that once he was arrested or died, the problem ended. In reality, Epstein functioned as a node, not a source. The networks he facilitated—financial structures, research funding pathways, social leverage mechanisms—did not depend on his continued presence. Treating Epstein as an endpoint protects the systems that enabled him by diverting attention away from institutional continuity and toward individual culpability alone.
4. Volume as Obfuscation: How Truth Gets Lost
A three-million-page document release appears transparent but can function as a form of concealment. When information volume exceeds analytical capacity, meaningful signals are buried under noise. Patterns dissolve into fragments; relationships become harder to trace. This dynamic favors institutions with legal teams, data analysts, and time—while overwhelming independent researchers and the public. Volume without guidance does not clarify truth; it often delays it.
5. Institutional Incentives to Avoid Pattern Recognition
No major institution—financial, academic, governmental, or media—benefits from publicly acknowledging systemic failure. Pattern recognition threatens reputations, funding streams, legal exposure, and public trust. As a result, there are strong incentives to isolate misconduct, narrow timelines, and discourage cross-domain analysis. This creates a bias toward compartmentalization: crimes are prosecuted, but systems are preserved. Recognizing patterns is not dangerous because it is speculative—it is dangerous because it is implicating.
6. Epstein’s History and Hidden Background
Public records show that Jeffrey Epstein maintained close financial and social relationships with powerful individuals, most notably retail magnate Leslie Wexner, who granted him unusual authority over his finances. However, no court findings or declassified documents have established that Epstein had a confirmed “boss,” intelligence handler, or formal affiliation with an organized “Deep State” or Illuminati structure.
Much of the speculation surrounding handlers stems from the opacity of his wealth, his access to global elites, and the controversial legal protections he received. Distinguishing documented relationships from unproven claims is essential when examining the power networks that enabled his activities.
The Epstein Files: Explained For Dummies
The DOJ released 3.5 million files on Epstein. Let's dive in. Watch Max Blumenthal explain Epsteins connection to Mossad:https://www.youtube.com/watch?v=1U-m...
The Rise and Fall Of Jeffrey Epstein: The Truth Behind
The Rise and Fall Of Jeffrey Epstein: The Truth BehindDisclaimer: The scenes shown in this video are reenactments and visual representations created for stor...
Tucker Responds to the Epstein Files, Pizzagate & the Demonic Global Crime Network with Ian Carroll
It looks like Pizzagate is basically real. Ian Carroll explains.
The Women Who Kept Jeffrey's Operation Running: THE CORE FOUR
Today, all of these women stay out of the spotlight... but I would be willing to argue that at least a couple of them still live at East 66th Street, which J...
Epstein Files Exposed: The One Mistake That Brought Down His Secret Empire
He thought he was untouchable. For decades, Jeffrey Epstein moved in the shadows of presidents, princes, billionaires, and global elites… until a series of s...
Tucker Reacts to The Newest Release of Epstein Files
Tucker examines the latest batch of Epstein Files and what questions we should really be asking.
Epstein’s Personal Background
Where is Karyna Shuliak now 2026 | Girlfriend Lost Lover Partner?
Today we're exploring the journey of Karyna Shuliak, the Belarusian dentist who became a central figure in the aftermath of the Jeffrey Epstein scandal. Know...
Epstein Files | The Evidence Nobody Can Ignore | Storytime
A billionaire buys a “paradise” island. Locals call it something else: “Pedophile Island.” From a rigged plea deal to a “suicide” with broken cameras and a m...
BREAKING NEWS: Updates & Reports:
Epstein Files Expose the Globalist Script: From Transgenderism to Digital ID
The Sudden Vindication of Conspiracy Theorists For years, those labeled ‘conspiracy theorists’ for speaking of a ruling class operating above governments were mocked, censored, and financially punished. The Department of Justice’s long-delayed, partial release of documents related to Jeffrey Epstein’s network has delivered a staggering vindication. The files confirm the existence of a powerful, supra-governmental […]
Andrew arrested on suspicion of misconduct in public office as King says 'law must take its course' - live updates
It comes after Thames Valley Police said they were assessing a complaint over the alleged sharing of confidential material by the former prince with Jeffrey Epstein.
Ex-Prince Andrew Could Be Charged With TREASON! | Royal Expert Andrew Lownie
Kevin O'Sullivan and Andrew Lownie discuss the extraordinary events surrounding Prince Andrew's arrest at Sandringham. Lownie, author of "The Decline and Fal...
BREAKING: French Police Raid Arab World Institute in Paris as Epstein Probe Expands | AC15
French police have raided the Arab World Institute (Institut du Monde Arabe) in Paris as part of a financial probe linked to former president Jack Lang and h...
Epstein's Crimes Against Humanity
UN Experts classify Epstein files as Crimes Against Humanity!
Knowing what I discovered the past decade about the UN, I never, ever expected a move like this. I still can’t believe it, but as it’s really published on their websites, I have to share it with you. My god, I’m shaking and trembling by the enormity of this news!
Epstein Files: The Next Release Has Everyone TERRIFIED! Could Internet GO DARK?
https://www.bloodflow7.com/NinoStart Reaching Your Weight Loss Goals Now!http://trimwithnino.comGet 44% OFF By Clicking The Link Above^^^Check out David Rodr...
Tom Pritzker steps down as executive chairman of Hyatt Hotels
Tom Pritzker, executive chairman of Hyatt Hotels Corporation and cousin to Illinois Gov. JB Pritzker, is stepping down from his role with the hotel supergian...
Epstein Files: Victim’s Story Takes a Shocking Turn
EVERY single perpetrator AND enabler needs to be held accountable for any crimes committed of CSA. Epstein NOT alone!
Tina Brown on Ghislaine Maxwell, the Royals and the Worst People in Media Right Now | The Interview
Tina Brown was one of the most prominent media figures in the 1980s and ’90s, serving as the top editor at Vanity Fair and then The New Yorker. She later lau...
Les Wexner Deposition
Who Is Leslie Wexner? Narrated by Margaret Cho
Billionaire Midwesterner Leslie Wexner built his empire on fast fashion and, by his own account, has more money than he knows what to do with. And who better...
🚨FULL LES WEXNER VIDEO DEPOSITION ON EPSTEIN COVER UP
MeidasTouch presents the full unedited video deposition of Les Wexner on the House Oversight Committee investigation into Epstein. Visit https://meidasplus.c...
Inside the Les Wexner deposition: What he told congressmembers
The questions that members of Congress asked Ohio billionaire Les Wexner on Wednesday didn’t just touch on his business relationship with convicted sex offen...
BREAKING: Billionaire Les Wexner Testifies To Congress Today About Epstein Files Amid New Emails
Billionaire Leslie Wexner is testifying before the House Oversight Committee Wednesday about his relationship with Jeffrey Epstein, marking the first time on...
Epstein victim says Ohio billionaire Les Wexner engaged in sex acts with her
Epstein victim says Ohio billionaire Les Wexner engaged in sex acts with her. FOR MORE: https://nbc4i.co/3S9IVFcStay informed about Columbus and central Ohio...
New Elite Figures Compromised Epstein Connections
Anand Giridharadas: What the Epstein Documents Reveal About Power in America
In a wide-ranging conversation, Anand Giridharadas joins Terry Moran to examine power, morality, and the elite networks that shape American life — from polit...
17 'High-Profile' Elites Punished for Epstein Ties
Resignations, ridicule, and criminal investigations. The fallout from the Jeffrey Epstein files is intense for high-profile politicians, business leaders, an...
PR NIGHTMARE - Celebrities Go Into Hiding As Files Unleash Hell - Lauren The Insider & Shaun Attwood
Hosted by Lauren The Insider and Shaun Attwood, this explosive show dives into the world’s most controversial headlines, hidden networks, and high-level scan...
Ellen DeGeneres accused of the UNTHINKABLE
In today’s breaking news breakdown, we examine viral online claims and controversies surrounding Ellen DeGeneres and alleged connections being discussed in r...
Hollywood Mogul to Sell his Agency over Epstein Connection
ABC's Olivia Rubin reports on Hollywood heavyweight Casey Wasserman sellinghis business following the release of "suggestive emails" with longtime Epstein a...
Mel Gibson Reveals Epstein's Connection To Sound of Freedom Movie
Mel Gibson Reveals Epstein's Connection To Sound of Freedom MovieSo after years of being blackballed by Hollywood, Mel Gibson just made a major comeback afte...
“The Truth Is Way Worse Than I Thought” | Whitney Webb’s Terrifying Discovery
Check out Whitney Webb's bestselling book exposing the criminal rise of Jeffrey Epstein (One Nation Under Blackmail): https://amzn.to/4kcNCdICredit to Peter ...
Elite figures face growing fallout over Epstein files | NewsNation Live
Several high-profile figures are facing continued fallout after the Department of Justice released files related to its investigation into Jeffrey Epstein. T...
Who is UAE billionaire in the Epstein files? | MEE Live
US Attorney General Pam Bondi defended the justice department (or DOJ)’s handling of the Epstein Files during a congressional hearing on Wednesday. It descen...
Key Architect of ‘Disinformation Dozen’ List Resigns After ‘Epstein Files’ Reveal Tangled Web of Censorship
The 2021 publication of “The Disinformation Dozen” list of 12 “leading online anti-vaxxers” sparked efforts to discredit U.S. Health Secretary Robert F. Kennedy Jr., Sayer Ji and other outspoken critics of COVID-19 pandemic policies and vaccines. Five years later, the release of the “Epstein Files” has led to the resignation of one of the list’s architects — Morgan McSweeney.
BREAKING: Boebert Exposes HORRIFYING Details In Unredacted Epstein Files
Rep. Lauren Boebert revealed what she saw in the "terrifying" unredacted Epstein files. Ana Kasparian discusses on The Young Turks. Do you agree with TYT's t...
Epstein was Really Buying Girls Online...
Follow me on Instagram For Updates - https://www.instagram.com/traploreross/ Watch my videos early and uncut and support the channel on Patreon for just $2 -...
The Exposure of Evil from the Epstein Files and the Rise of the Antichrist – Are You Ready to See What’s Coming?
February 12, 2026 | River Wilde The world is witnessing an unprecedented wave of revelations—powerful leaders, wealthy elites, and institutions long considered untouc…
SECTION II — FILES & DOCUMENTS; ARCHITECTURE OF DECEPTION
“Volume is not transparency. Structure is.”
Understanding the Release
The release of approximately three million pages of material by the U.S. Department of Justice is not a narrative disclosure—it is an archive exposure. These documents were never designed to be read as a coherent story. They were generated across years by different agencies, law firms, courts, financial institutions, and investigators, each operating within narrow mandates. Section II establishes how the release must be approached: not as a linear record of events, but as a fragmented system of records whose meaning only emerges when relationships are reconstructed across silos.
This section explains why many readers experience confusion or dismissal when engaging the files. The architecture of the release favors compartmentalization. Financial data is separated from behavioral testimony. Scientific correspondence is detached from funding trails. Legal exhibits are isolated from policy outcomes. This fragmentation is not accidental—it mirrors how modern institutions protect themselves. Understanding the architecture is therefore a prerequisite for understanding the truth content of the documents themselves.
Finally, Section II provides methodological discipline. Without a framework, researchers risk either drowning in volume or cherry-picking sensational fragments. GAR’s approach treats the release as a distributed system: each document is a node, meaningful only in relation to others. This section teaches readers how to orient themselves inside that system before attempting interpretation.
Understanding the Release
1. Categories of DOJ Documents
The release includes multiple document classes—court filings, depositions, financial records, emails, travel logs, exhibits, and investigative memoranda—each created for a specific procedural purpose. No single category tells the story. Legal filings prioritize liability, not context. Depositions reflect strategy as much as truth. Financial records show movement of capital but rarely intent. Understanding the category of a document is essential before assigning weight or meaning to its contents.
2. Financial vs. Behavioral vs. Scientific Records
The documents fall broadly into three analytical domains. Financial records track money flows, trusts, donations, and banking relationships. Behavioral records—testimony, witness statements, emails—capture actions, relationships, and social dynamics. Scientific records include correspondence, funding discussions, conference planning, and research-related exchanges. These domains are rarely cross-referenced within the release, requiring independent reconstruction to reveal overlap and coordination.
3. Redactions, Sealed Exhibits & Missing Data
Redactions and sealed exhibits are not evenly distributed. They cluster around specific individuals, institutions, and subject areas—particularly finance, intelligence-adjacent material, and research funding. Missing data does not imply absence of activity; it often signals legal sensitivity, ongoing exposure, or institutional protection. Section II trains readers to recognize patterns in what is obscured, not just what is revealed.
4. Why Scientific Correspondence Is Scattered
Scientific and academic communications appear fragmented because they were never central to the original criminal cases. As a result, they are dispersed across exhibits, emails, third-party records, and ancillary filings. This scattering makes the science thread easy to dismiss as incidental. In reality, its dispersion reflects jurisdictional blind spots—science funding and collaboration often fall outside traditional prosecutorial focus, even when strategically significant.
5. How to Read Between Document Silos
The most important signals do not reside within single documents but between them. Reading between silos means correlating funding records with conference invitations, cross-referencing emails with career trajectories, and aligning timelines across financial, academic, and policy domains. This approach does not rely on speculation; it relies on relational analysis. Section II equips readers to move from isolated facts to structural understanding—without collapsing into narrative shortcuts.
6. Final DOJ Classified Document Release
The early development of artificial intelligence, the internet, Bitcoin, genetics, and advanced computing did not emerge randomly — they evolved from decades of military research, academic experimentation, and private-sector innovation. From DARPA-funded networking projects that became the modern internet, to cryptographic breakthroughs that enabled Bitcoin, to genomic mapping and machine learning systems, each field represents a convergence of government funding, scientific curiosity, and technological acceleration.
These parallel innovations reshaped power structures globally — decentralizing information, digitizing value, automating decision-making, and unlocking biological code — laying the foundation for the digitally integrated world that now defines the 21st century.
Epstein Files | Department of Justice | Homepage | United States Department of Justice
Official website of the U.S. Department of Justice (DOJ). DOJ’s mission is to enforce the law and defend the interests of the United States according to the law; to ensure public safety against threats foreign and domestic; to provide federal leadership in preventing and controlling crime; to seek just punishment for those guilty of unlawful behavior; and to ensure fair and impartial administration of justice for all Americans.
Jeffrey Epstein Files | FBI Library
The FBI’s FOIA Library contains many files of public interest and historical value. In compliance with the National Archives and Records Administration (NARA) requirements, some of these records are no longer in the physical possession of the FBI, eliminating the FBI’s capability to re-review and/or re-process this material. Please note, that the information found in these files may no longer reflect the current beliefs, positions, opinions, or policies currently held by the FBI.
JeffTube hosts videos from Epstein Files and looks just like YouTube - Link and details
JeffTube is a platform that looks similar to YouTube and hosts videos from the Epstein Files. It lets you browse through the videos with ease, without having to download them. There are a few things you should keep in mind while browsing JeffTube.
Epstein files lead to fallouts worldwide | Worldwide Connections
The most recent released files on Jeffrey Epstein have prompted a series of fall out among some of the most powerful around the world.
The Epstein Files and the 100 Most Powerful Figures
Archival / Research Title:DOJ Epstein File Releases (2026): Documented Record and Analytical Commentary WorkCommercial Title: The Epstein Files and the 100 M...
Epstein Files: 100 Famous Figures Named (2026 Update) — Some May Shock You
Commercial TitleEpstein Files: 100 Famous Figures Named (2026 Update) — Some May Shock YouArchival / Research TitleA Compilation of Proper Names Appearing in...
New Heavily Redacted FBI Records Reveal That Thomas Crooks Was Hospitalized
Headline USA Editor Ken Silva Breaks Latest Developments On Thomas Crooks, The Pentagon’s Obstruction Of Rep. Eric Burlison’s Visit to Area 51 And MORE!
Epstein files: Epstein-Bannon texts spark MAGA civil war, Wexner gets deposed
Steve Bannon’s newly released text messages with Jeffrey Epstein spark MAGA backlash while Les Wexner, the former owner of Victoria’s Secret and a key player...
Who Had the Most Contact with Jeffrey Epstein?
In the years after Epstein pled guilty to soliciting sex from a minor, he maintained consistent contact with a vast network of rich and powerful figures. The...
Which are the Most Disturbing Epstein Emails?
The Economist used a large language model to analyse 1.4m of Epstein’s emails to identify the most disturbing. It flagged numerous concerning conversations w...
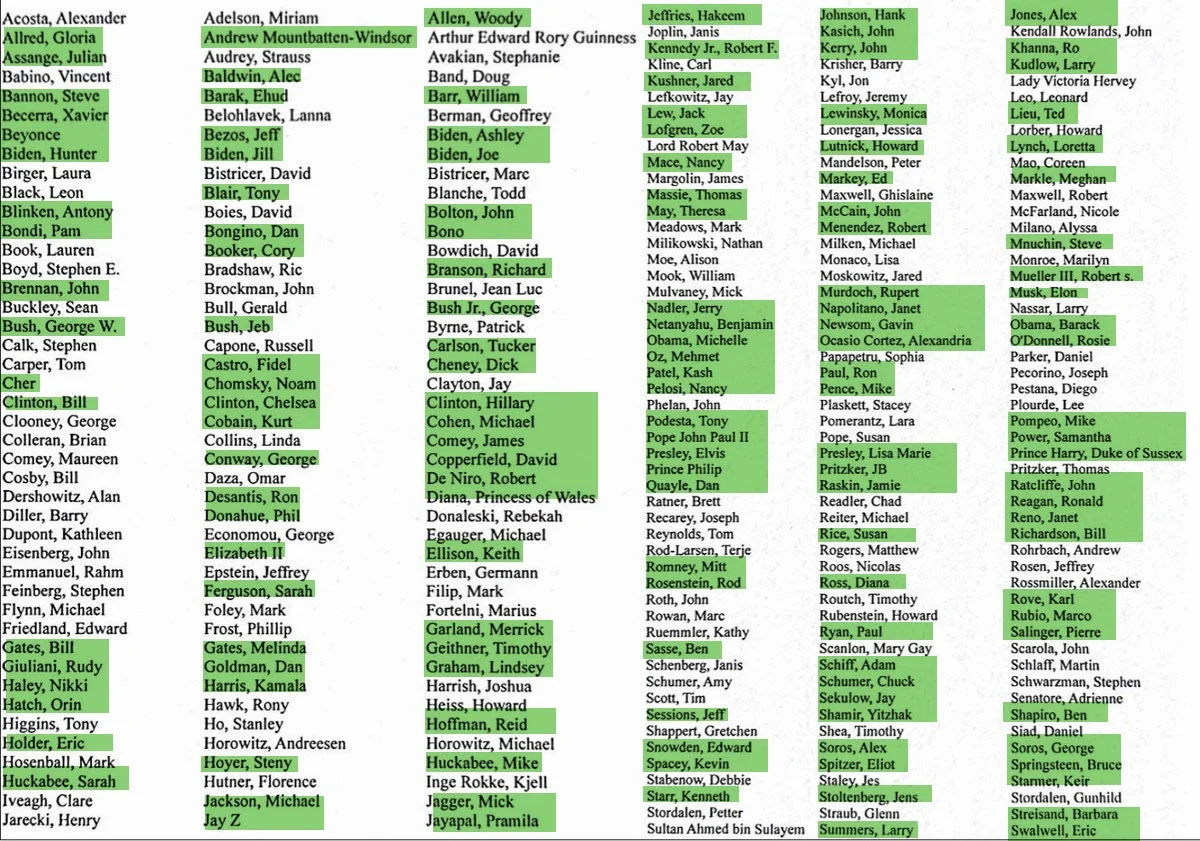
US HOMELAND SECURITY: EPSTEIN LIST OF HIGH PROFILE NAMES
Yesterday, Attorney General Pam Bondi reported by letter to Congress that 3.5 Million documents connected with the criminal investigation(s) of Jeffrey Epstein, have been made public. Below is the list.
Various compilations of the unredacted names on that list are now appearing on social media – but almost NOTHING is appearing on so-called “main stream” media. Now, we seem to know why:
The names on the “list” include very high profile people like Hollywood movie stars, a now-former Assistant FBI Director, two former CIA Directors, several former US Attorneys General, sitting members of Congress, the sitting Attorney General of the United States, the sitting CIA Director, sitting state Governors, three former U.S. Presidents, TWO former U.S. Vice-Presidents, TWO former US Secretaries of State, and a whole slew of others including a deceased Pope and the deceased Queen of England!
Below is a social media posting claiming to show the complete list. It’s a “Who’s Who” of politicos. Did all these people sex minors/children on Epstein Island?
Epstein Photo Files
10 Darkest Celebrity Pictures & Videos in the Epstein Files
The infamous Epstein files have revealed some truly disturbing connections to Hollywood and political elites. Join us as we examine the most unsettling photos and videos released from Epstein's estate and official records.
30 Photos from Epstein Dump That Will Blow Your Mind
A new release of photographs tied to Jeffrey Epstein is raising fresh questions — and a lot of speculation. The images, obtained by House Oversight Committee...
LIVE | Epstein Files MOST DISTURBING VIDEOS| Epstein CHASES Young Girls, SMIRKS During Interrogation
Shocking revelations shake the Epstein case once again as disturbing videos linked to the Epstein files spark global outrage. The footage, now at the center ...
New Epstein files released: Photos of Bill Clinton in hot tub, Kevin Spacey & Chris Tucker included
Former President Bill Clinton is among the celebrities seen appearing in the trove of fresh photos related to the Jeffrey Epstein case that were released Dec...
More photos from Epstein’s estate released by House Democrats as deadline to release DOJ files looms
There are multiple photographs of a woman’s body on which quotes from “Lolita,” the Vladimir Nabokov novel about a man’s sexual obsession with a 12-year-old ...
Epstein Files Videos
I Watched 14 Hours of Epstein Videos. Here’s What I Saw.
On January 30, 2026, the Department of Justice released more than three million files related to Jeffrey Epstein. And buried within that are roughly 2,000 pr...
Epstein’s Little Black Book
New video goes inside Jeffrey Epstein's Florida mansion
Nearly two dozen women who say Jeffrey Epstein abused them have told their stories to a judge, while newly revealed police video takes us inside Epstein's Fl...
SECTION III — EPSTEIN AS AN EXCLUSIVE ACCESS BROKER
“Influence belongs to those who control access, not ideas.”
Why Scientists Took His Calls
This section reframes Jeffrey Epstein not as a mastermind or subject-matter expert, but as a broker of access. The documents show that Epstein’s influence did not stem from original ideas, scientific insight, or even exceptional financial acumen. It stemmed from his ability to connect otherwise siloed elites—scientists, financiers, philanthropists, policymakers, and institutional gatekeepers—within controlled social and funding environments. His value proposition was proximity: to capital, to prestige, and to other powerful people.
Understanding Epstein as an access broker explains a persistent question: why highly credentialed scientists, mathematicians, and academics engaged with him at all. The answer is not intellectual admiration; it is structural incentive. Epstein offered informal funding pathways, introductions to donors, access to elite convenings, and insulation from bureaucratic friction. In fields where research timelines are long and grant processes slow, these shortcuts carry enormous appeal—especially when they arrive without obvious strings attached.
This section also dismantles the misconception that Epstein operated independently. His effectiveness depended on trust—borrowed trust, inherited trust, and strategically reinforced trust. He functioned as a bridge, allowing elites from different domains to interact without formal accountability. When read through this lens, Epstein appears less as an anomaly and more as a symptom of how modern power organizes itself: quietly, relationally, and outside formal structures.
Why Scientists Took His Calls
Scientists took Epstein’s calls because he offered what institutions often could not: discretionary funding, introductions to wealthy patrons, and access to exclusive intellectual circles. He reduced friction in a system defined by scarcity and competition. Importantly, engagement often appeared socially normalized—many assumed that others had already vetted him, creating a cascade of borrowed legitimacy.
1. Epstein’s Role as a Non-Expert Intermediary
Epstein did not contribute technical knowledge. His role was to convene, sponsor, and facilitate. He positioned himself between experts and resources, translating social capital into influence. This intermediary status allowed him to remain indispensable without being accountable for outcomes, while also insulating him from scrutiny typically applied to principal investigators or institutional leaders.
2. Access to Capital, Not Ideas
What Epstein offered was money, or pathways to money—often faster, quieter, and less restrictive than traditional grants. For researchers, this meant freedom from peer-review cycles and institutional constraints. For Epstein, it meant leverage. Capital created dependency, and dependency created influence, even in the absence of explicit demands.
3. Why His Social Power Exceeded His Net Worth
Epstein’s apparent wealth does not fully explain his reach. His social power was amplified by association: elite institutions, high-status individuals, and prestigious venues conferred credibility that money alone could not buy. Each new association reinforced the perception that he was safe, vetted, and valuable—multiplying his influence beyond his balance sheet.
4. Epstein as a Trust Bridge Between Elites
Epstein connected elites who would not ordinarily interact directly—academics with financiers, scientists with policymakers, donors with institutions. By hosting, funding, and facilitating introductions, he became a trust bridge. Once trust flowed through him, his removal would have required elites to confront uncomfortable questions about their own judgment—creating strong incentives for silence.
5. The Myth of the “Lone Financier”
The idea that Epstein acted alone obscures the relational infrastructure that sustained him. Access brokers require environments that reward discretion, value informality, and discourage transparency. Epstein did not invent those conditions; he exploited them. Treating him as a lone actor protects the systems that made his role both possible and profitable.
6. Famous Global Figures Exposed
We examine the Jeffrey Epstein case through primary records, verified documentation, and historical context. It does not engage in ideology, speculation, or accusation. Over several decades and across multiple countries, Epstein’s activities intersected with political, financial, academic, and social institutions of extraordinary influence. Recently unsealed court filings—including depositions, flight logs, contact books, correspondence, and other official records—have made public the names of numerous well-known individuals. These records raise important questions about access, proximity, and institutional oversight.
7. Who Was Epstein’s Boss & Handlers?
Public records show that Jeffrey Epstein maintained close financial and social relationships with powerful individuals, most notably retail magnate Leslie Wexner, who granted him unusual authority over his finances. However, no court findings or declassified documents have established that Epstein had a confirmed “boss,” intelligence handler, or formal affiliation with an organized “Deep State” or Illuminati structure.
Much of the speculation surrounding handlers stems from the opacity of his wealth, his access to global elites, and the controversial legal protections he received. Distinguishing documented relationships from unproven claims is essential when examining the power networks that enabled his activities.
Unmasking the Power Brokers: The Epstein Files' Richest and Most Connected
Unmasking the Power Brokers: The Epstein Files' Richest and Most ConnectedIn this shocking deep dive, we uncover the hidden connections of some of the world'...
Epstein Files | Top 100 Names
100 Celebrities from the Epstein Files | The rot goes DEEP apparently even beyond the human trafficking and child abuse
Epstein Files: 100 Famous Figures Named (2026 Update) — Some May Shock You
Commercial TitleEpstein Files: 100 Famous Figures Named (2026 Update) — Some May Shock YouArchival / Research TitleA Compilation of Proper Names Appearing in...
Kevork Almassian Warns: The Empire Above Jeffrey Epstein
Jeffrey Epstein files, Epstein emails, elite networks, hidden power, leverage, and media narratives—in this Syriana Analysis clip, Kevork Almassian explains ...
WHO THE ELITES WORSHIP - WHO DID EPSTEIN WORK FOR? #epsteinfiles
The Epstein operation was a honey trap operation to entrap politicians, lawmakers, policy makers, academia, millionaires, billionaires, royalties, celebrities, and people in the media eye to become ISRAELS assets.
Epstein Files Expose Ellen DeGeneres As Hollywood's Most 'Prolific Cannibal'
Get your essential medications today at a fraction of the cost: https://affordablerxstore.com/ Promo Code TPV10 for 10% off- Protect your privacy from prying...
How Jeffrey Epstein Gained Power Over The Global Elite
Watch AD FREE here: https://youtu.be/M47DAKVgf3AWhy is the latest release of the Epstein Files bad for people like Donald Trump, Elon Musk, and Bill Gates? A...
Shocking Epstein Tapes: What Was Said About Obama, Iran’s Nuclear Program and Vladimir Putin | APT
Newly surfaced audio recordings reveal private conversations between Jeffrey Epstein and former Israeli Prime Minister Ehud Barak, offering rare behind-the-scenes insight into global politics, leadership, war strategy, and powerful international relationships.
Deepak Chopra & Dalai Lama SCANDALOUS Epstein Files Appearances! w/ Mikki Willis
Two of the perhaps most surprising names to appear in the Epstein files are those of the Dalai Lama and Deepak Chopra. Jimmy and his guest, filmmaker Mikki W...
Epstein Files: Records Detail South Africa Links
US Justice Department records detail Jeffrey Epstein’s links to South Africa, including references to business contacts and efforts to recruit South Africans...
Epstein’s Power Elite | WHO’s The Boss
We Know Who The Real Head Of The Snake Is... (Rare Unreleased Interview) | Whitney Webb
For business inquiries email us here: info@onlythesavvy.comDisclaimer: The content in this video is for informational and entertainment purposes only. It is ...
Epstein’s Israel links and everything else ignored by mainstream media | The Listening Post
The Epstein files dump has led to days of intense media coverage, revealing how powerful elites around the world engaged in either illegal or morally reprehe...
Epstein Administration Assistants & Support Staff
The Women Who Kept Epstein’s Empire Running (The Untouched Inner Circle)
Jeffrey Epstein did not operate alone. Behind the private jets, the Manhattan townhouse, and the island were women who worked inside his organization for yea...
SECTION IV — INFLUENCING SCIENCE & EMERGING TECHNOLOGIES
“Every breakthrough carries two futures: one public, one strategic.”
The Most Suppressed Research Thread
This section addresses the least examined—and most consequential—dimension of the Epstein files: the convergence of frontier science, unconventional funding, and strategic interest. While public attention focused on criminal behavior and social networks, the documents quietly reveal sustained proximity to research domains that shape future power—advanced computation, theoretical physics, systems biology, complexity modeling, and early artificial intelligence foundations. These fields do not generate immediate headlines, but they define long-range capability. Their suppression in public discourse is not evidence of insignificance; it is a signal of sensitivity.
The significance lies not in proving clandestine breakthroughs, but in identifying structural patterns: private sponsorship of high-impact research outside traditional oversight; convenings that bypass peer review; and funding pathways designed to accelerate discovery while minimizing disclosure. This is where influence is most effective—before technologies harden into products, policies, or doctrines. The files suggest that Jeffrey Epstein operated near this edge, not as a scientist, but as a facilitator of access to people and projects that matter years before outcomes are visible.
Section IV reframes “suppression” as a function of complexity and risk. Frontier science is difficult to audit, easy to misinterpret, and politically explosive when tied to intelligence, defense, or economic advantage. As a result, institutions default to silence or minimization. This section equips readers to understand why these research threads are scattered, underreported, and often dismissed—despite their outsized impact on future governance, security, and markets.
The Most Suppressed Research Thread
1. Why Epstein Targeted Frontier Science
Frontier science offers leverage before visibility. Breakthrough domains—where theory precedes application—create asymmetric advantage for those with early access. By positioning himself near researchers working at the edge of knowledge, Epstein gained proximity to optionality: insights, networks, and influence that mature long after initial funding. The appeal was not discovery itself, but timing—being early enough to shape trajectories quietly.
2. Funding Outside Traditional Grant Oversight
Traditional grants impose transparency, milestones, and peer review. The documents indicate alternative funding routes that reduced friction and accelerated work—private donations, discretionary gifts, and invite-only sponsorships. These pathways can empower innovation, but they also bypass accountability. When oversight diminishes, influence concentrates, and the boundary between support and steering becomes ambiguous.
3. Dual-Use Research: Civilian vs. Strategic Applications
Many advanced fields are inherently dual-use. Techniques developed for medicine, modeling, or materials can translate into surveillance, defense, or behavioral prediction. The files point to research environments where this duality was understood but rarely foregrounded. Dual-use is not an allegation; it is a property. Its presence explains why some projects attract attention beyond academia—and why disclosure is often constrained.
4. Why These Fields Attract Intelligence Interest
Intelligence services prioritize prediction, control, and foresight. Frontier sciences—complex systems, AI foundations, network theory, bio-modeling—directly serve those aims. Interest does not require overt sponsorship; proximity is sufficient. Conferences, salons, and private briefings provide soft access without fingerprints. This section clarifies why intelligence interest appears as adjacency, not ownership, within the records.
5. The Ethics Gap in Cutting-Edge Research
Ethical frameworks typically lag innovation. When funding is private, timelines are compressed, and oversight is informal, ethics become discretionary rather than institutional. The files suggest environments where ethical review depended on personal judgment instead of standardized process. The gap is not malice; it is structural latency—rules built for yesterday’s science applied to tomorrow’s capabilities.
6. Early Development of AI, Internet, Bitcoin, Genetics, and Technology
The early development of artificial intelligence, the internet, Bitcoin, genetics, and advanced computing did not emerge randomly — they evolved from decades of military research, academic experimentation, and private-sector innovation. From DARPA-funded networking projects that became the modern internet, to cryptographic breakthroughs that enabled Bitcoin, to genomic mapping and machine learning systems, each field represents a convergence of government funding, scientific curiosity, and technological acceleration.
These parallel innovations reshaped power structures globally — decentralizing information, digitizing value, automating decision-making, and unlocking biological code — laying the foundation for the digitally integrated world that now defines the 21st century.
I’m EXPOSING the Whole Damn Thing!! | Eric Weinstein
“This Was the Moment the Mask Slipped.” Before the arrests. Before the scandals. Before the name Jeffrey Epstein became radioactive — Eric Weinstein came face to face with him. Not by accident. Not casually. But through a carefully arranged meeting. From the first minutes, something felt off.
Tracking Jeffrey Epstein’s Influence on the Cutting Edge of Tech Research
A new tranche of files from the DOJ reveals new details and relationships between the disgraced financier and prominent researchers and academics.
9 Tech Titans in the Epstein Files
Jeffrey Epstein had a network of tech leaders at his fingertips.
Everything you need to know about Bitcoin and the Epstein Files - Blockspace
An inside look into the nexus of Bitcoin and Jeffrey Epstein.
The Epstein Files: The Hidden Money Behind Bitcoin
The Epstein Files just revealed something nobody expected. Jeffrey Epstein's money quietly funded the developers who kept Bitcoin alive.In January 2026, the ...
Jeffrey Epstein and the Secret Program That Built Modern AI
Jeffrey Epstein wasn’t just a financier moving through elite social circles. He was deeply connected to the origins of modern artificial intelligence, throug...
How Epstein Channelled Race Science and 'Climate Culling' Into Silicon Valley’s AI Elite
The Epstein files expose how racial hierarchy, genetic “optimisation” and even climate-driven population culling circulated inside Big Tech circles
Files cast light on Jeffrey Epstein’s ties to cryptocurrency
Newly released documents detail convicted sex offender’s early backing of bitcoin and Coinbase
SECTION V — PHYSICISTS, MATHEMATICIANS & THEORETICAL SCIENTISTS
“Abstract knowledge becomes power when prediction replaces force.”
Why the Smartest Minds Were in the Room, Epstein as the Master Manipulator
This section examines why a disproportionate number of elite physicists, mathematicians, and theoretical thinkers appear—directly or indirectly—around Jeffrey Epstein and his broader network. The answer is not vanity or social curiosity. It is that these disciplines sit closest to first principles—the underlying rules that govern reality, systems, and prediction. Power does not only seek control over resources or institutions; it seeks foresight. Theoretical elites provide that edge long before applications become visible to the public.
Unlike applied sciences, theoretical work operates upstream. It shapes what can be built years or decades later. That makes these thinkers uniquely valuable to finance, intelligence, defense, and governance interests. Their presence in private salons, off-record conferences, and unconventional funding environments reflects strategic alignment, not coincidence. This section reframes those interactions as structural, not social.
Crucially, this is not an indictment of scientists themselves. Most operated in good faith, pursuing curiosity and discovery. The pattern emerges at the systems level: when frontier theory is quietly aggregated, selectively funded, and insulated from transparency, it becomes a strategic asset class. Section V explains why these minds were sought out—and why their work remains poorly understood outside elite circles.
Why the Smartest Minds Were in the Room, Master Manipulator
Elite theorists were present because they operate where uncertainty is converted into structure. Their work reduces complexity into models, equations, and probabilities that can be acted upon. For power centers, this translates into early warning, strategic advantage, and narrative framing before outcomes materialize. Intelligence and capital follow cognition.
1. The Role of Theoretical Physics & Cosmology
Theoretical physics and cosmology explore the fundamental laws of space, time, energy, and matter. Beyond curiosity, these fields influence advanced computation, energy systems, materials science, and long-term technological horizons. They also shape worldview—how reality itself is conceptualized. That makes them quietly influential in both strategic planning and ideological framing.
2. Advanced Mathematics, Modeling & Prediction Systems
Mathematics is the language of prediction. Advanced modeling—statistics, optimization, network theory, game theory—underpins everything from financial markets to logistics, epidemiology, and military planning. Those who fund or access advanced mathematical insight gain leverage not by certainty, but by probabilistic advantage.
3. Complexity Theory, Chaos & System Control
Complexity theory and chaos studies focus on nonlinear systems—economies, ecosystems, societies—where small inputs can trigger large, unpredictable outcomes. These disciplines are essential for understanding systemic risk, cascading failure, and intervention timing. For power, the goal is not perfect control, but adaptive response under uncertainty.
4. Artificial Intelligence Foundations (Pre-Boom Era)
Before AI became a consumer phenomenon, its foundations were theoretical: neural networks, learning theory, optimization, and symbolic reasoning. Early involvement in these domains offered influence over architectures, assumptions, and ethical defaults long before public debate emerged. Pre-boom access equals post-boom advantage.
6. Why These Disciplines Matter to Power
Power in the modern era is less about force and more about anticipation. Disciplines that improve forecasting, modeling, and system understanding directly enhance decision dominance. Physics, mathematics, and theoretical sciences do not command authority—but they quietly shape the terrain on which authority operates. That is why power seeks proximity to them, often without visibility.
6. Leading Scientist Associations & Control
Throughout his career, Jeffrey Epstein cultivated relationships with prominent scientists, researchers, and academic institutions, often presenting himself as a patron of advanced research in physics, genetics, artificial intelligence, and evolutionary theory. While some associations were philanthropic in nature, questions have been raised about influence, reputational laundering, and the extent to which financial support may have shaped access, credibility, or silence within elite academic circles.
7. Private Jets, Secret Clubs, Island, Ranch, NY Brownstone (Who’s Who)
Epstein’s network operated across an ecosystem of exclusive spaces — including his private jets, Manhattan townhouse, New Mexico ranch, Palm Beach estate, and the private island Little Saint James. These locations became hubs where politicians, royalty, academics, celebrities, and financiers intersected. Understanding “who was where” and in what capacity remains central to mapping the broader social and power network that surrounded him.
Private jets, parties and eugenics: Jeffrey Epstein's bizarre world of scientists
The billionaire financier and convicted sex offender famously mixed with presidents, models and film stars. But he also indulged his unorthodox beliefs by cultivating top scientists
Which scientists, labs, or institutions had financial ...
Executive summary Newly released caches of Jeffrey Epstein’s emails and documents show he maintained financial and professional ties or exchanges with a r…
Jeffrey Epstein’s Links To Scientists Are Even More Extensive Than We Thought
Scientists took Epstein’s money or associated with the financier after he was jailed for soliciting an underage girl for prostitution. Some say they are sorry. Others didn’t comment.
Epstein files reveal deeper ties to scientists than previously known
Latest batch of documents show researchers consulting the financier and sex offender on publications, visas and more.
Jeffrey Epstein files shed light on ties to Santa Fe Institute scientists
Epstein had a relationship with Murray Gell-Mann, who won a Nobel Prize in physics. Epstein helped fund Gell-Mann's research.
Andrew Huberman Explains Why Scientists Hung Around Jeffrey Epstein
t’s crazy to me we live in a world where the government will go after regular citizens and throw the book at them but when there is definite evidence of the people who flew on that plane and went to that island multiple times gets completely ignored and all of those monsters get off Scott free. We have a huge problem in this country.
Jeffrey Epstein E-mails Reveal Depth of Ties to High-Profile Scientists
A trove of e-mails from convicted sex offender Jeffrey Epstein was released by a congressional committee on Wednesday
Epstein's Silicon Valley connections went beyond Gates and Musk
The new Epstein files released by the DOJ show that the deceased financier was able to build relationships across Silicon Valley, from Bill Gates to Peter Thiel.
Former CWRU professor Krauss appears in Epstein files
On Nov. 12, the U.S. House Oversight Committee released more than 20,000 documents in connection to the investigation of convicted sex offender Jeffrey Epstein. The files show the extent of the financier’s connections in academia, politics and journalism, including Noam Chomsky and former Harvard University President Lawrence Summers. Among the documents, Case Western Reserve University...
Jeffrey Epstein Had a Bizarre Obsession With "Improving" Human DNA, and He Was Emailing With Top Scientists About It
Jeffrey Epstein corresponded with and funded numerous top scientists, with whom he shared his deranged ideas for improving human genes.
The Epstein Files Just EXPOSED the AI Mind Control Agenda (2026 Warning)
Blocktrust IRA: Get up to $2,500 funding bonus to kickstart your account at https://tomcryptoira.comIncogni: Take your personal data back with Incogni! Use c...
Jeffrey Epstein and the Secret Program That Built Modern AI
Jeffrey Epstein wasn’t just a financier moving through elite social circles. He was deeply connected to the origins of modern artificial intelligence, throug...
SECTION VI — ELITE UNIVERSITY PIPELINES & PARTNERSHIPS
“Prestige does not prevent capture—it often conceals it.”
Research as a Gatekeeping Mechanism
This section examines how elite universities became critical infrastructure in the Epstein network—not as conspirators, but as gatekeeping systems that convert money into legitimacy, access, and protection. Institutions such as Harvard University and its peer schools occupy a unique position: they sit at the intersection of science, capital, government, and prestige. When power seeks proximity to knowledge without visibility, universities provide an ideal environment—open enough to attract talent, closed enough to control scrutiny.
Elite research institutions function as credential multipliers. Funding routed through them gains instant legitimacy; individuals associated with them inherit institutional trust. This makes universities attractive neutral ground for donors, financiers, intelligence-adjacent actors, and policymakers who require plausible deniability. The documents suggest that Epstein’s proximity to these environments was not incidental—it reflected an understanding that universities launder intent through reputation.
Section VI does not argue that universities acted with malicious intent. Rather, it shows how structural incentives—funding pressure, prestige competition, donor dependence—create blind spots. When research pipelines prioritize money, access, and output over transparency, accountability becomes diffuse. This section explains why no single department, board, or administrator ever “saw the whole picture”—and why that fragmentation benefits external power.
Research as a Gatekeeping Mechanism
Research funding determines who advances, which ideas are explored, and which networks form. Elite institutions act as gatekeepers by deciding which projects receive resources and which scholars gain visibility. When private funding enters these pipelines, it can quietly shape intellectual direction without overt interference—steering fields while appearing hands-off.
1. Ivy League Research Departments & Private Funding
Ivy League departments attract private donors precisely because of their prestige and influence. Donations framed as academic philanthropy can bypass public scrutiny while granting donors proximity to leading researchers. The files suggest patterns where private funding supplemented—or circumvented—traditional grant mechanisms, embedding influence inside respected institutions without triggering alarms.
2. Why Universities Became Neutral Ground for Power
Universities are perceived as ideologically neutral, truth-seeking spaces. That perception makes them safe meeting grounds for actors who might attract scrutiny elsewhere. Conferences, advisory boards, visiting scholar programs, and donor events allow elites from different sectors to interact under the cover of academia—without the optics of corporate or governmental coordination.
3. Grant Capture & Influence Without Oversight
Grant capture occurs when funding priorities begin to reflect donor interests more than independent inquiry. Unlike public grants, private donations often lack standardized disclosure, review, or outcome requirements. This creates opportunities for influence without formal oversight—especially in emerging fields where ethical and regulatory frameworks lag behind innovation.
4. Academic Prestige as Legitimacy Shield
Association with elite universities provides reputational armor. Individuals and projects linked to prestigious institutions benefit from a presumption of legitimacy that discourages questioning. This shield does not require explicit protection; it operates socially. Critics risk appearing uninformed, hostile to science, or anti-intellectual—raising the cost of scrutiny.
5. Why Institutional Accountability Failed
Accountability failed not because of conspiracy, but because responsibility was distributed across silos. Donors were vetted by development offices, research by departments, ethics by committees, and reputation by leadership—none of which held a complete view. This fragmentation ensures that when problems surface, no single entity can be held fully responsible, preserving the institution while obscuring systemic vulnerability.
6. Epstein’s Grants, Donations, Private Partnerships, & Gov. Funding
Jeffrey Epstein positioned himself as a patron of science and higher education, directing millions of dollars in donations and private grants to universities and research institutions. His funding reached prominent programs in physics, evolutionary biology, artificial intelligence, and genetics, often through direct relationships with leading academics and institutional development offices.
While most contributions were structured as private philanthropy rather than formal government allocations, questions later emerged about reputational risk, disclosure practices, and whether institutions fully vetted the source of funds. The controversy intensified after his 2008 conviction, as several universities acknowledged continuing to accept donations despite public knowledge of his criminal case.
7. Physicians Who Are In the Epstein Files!
The publicly released Epstein case materials — including court filings, unsealed depositions, and flight logs — reference various medical and scientific professionals who had social or professional contact with Jeffrey Epstein. It’s important to be precise here: the presence of a physician’s name in the files does not automatically indicate criminal conduct. Some physicians reportedly treated Epstein, some attended social gatherings, and others were mentioned in scheduling records or contact books. In certain cases, medical professionals were associated with Epstein through philanthropic or academic connections tied to research funding, conferences, or elite social networks. The files themselves reflect a wide net of contacts, not a confirmed roster of wrongdoing.
There have also been allegations — not criminal convictions — involving claims of questionable medical oversight or unusual practices connected to Epstein’s lifestyle and social circle. However, as of now, no broad criminal prosecutions of physicians specifically for participating in a coordinated “cover-up” have been established in court. When analyzing this category within the Epstein Files, the disciplined approach is to distinguish between documented professional contact, civil allegations, and proven criminal findings. In a case this high-profile, reputational damage can spread faster than verified facts — so separating association from evidence is essential.
BREAKING: Epstein Sought to Establish Behavioral Engineering Institute at Stanford
The Stanford Review has found that Jeffrey Epstein, through his close involvement with world-renowned neuroscientist Stephen Kosslyn, sought to create a behavioral engineering institute at Stanford University. This finding comes amidst the Friday DOJ release of 3.5 million pages of the files concerning the case of the convicted sex
How an Élite University Research Center Concealed Its Relationship with Jeffrey Epstein
New documents show that the M.I.T. Media Lab was aware of Epstein’s status as a convicted sex offender, and that Epstein directed contributions to the lab far exceeding the amounts M.I.T. has publicly admitted.
Jeffrey Epstein’s links to Hong Kong
Subscribe to our YouTube channel for free here: https://sc.mp/subscribe-youtubeThis video has been republished to correct a typo in a caption on a previous v...
Here’s What the Latest Epstein Files Say About His Ties to Higher Ed
New documents released by the Department of Justice on Friday reinforce that long after his criminal convictions, many prominent professors continued to communicate with him.
Professors in the Epstein files say they hoped friendship would lead to research funding
A new trove of documents released by the Justice Department reveals that Epstein’s reach into academia was wider than previously known.
EXPOSING Physicians Who Are In the Epstein Files!
Watch me, a real holistic plastic surgeon, reveal actual physicians who are in the Epstein Files. Some of them you know, some of them you don't. But all of t...
Epstein’s Ties With Academics Show the Seedy Side of College Fund-Raising
Professors and presidents are often eager to raise outside cash. Some are now facing blowback after connecting with Jeffrey Epstein.
Epstein is everyone’s problem | activism should be, too
While elite academia has always been greased by the philanthropy of the wealthy, students — like our professors and our institution — are not morally exempt from critically examining the sources and use of our educational funding, especially when that funding is provided on the pretense of a certain political purpose.
The Secret Program That Built the Internet (Epstein, Harvard & DARPA)
In this episode of Off Air, Attorney Ron Chapman walks through the lesser-known origins of today’s digital world, tracing a direct line between government-ba...
REPORT CONCERNING JEFFREY EPSTEIN’S INTERACTIONS WITH THE MASSACHUSETTS INSTITUTE OF TECHNOLOGY
This Report’s findings are the result of Goodwin Procter’s review and analysis of all of
the information obtained in the investigation, including 73 interviews of 59 witnesses and a
review of more than 610,000 emails and other documents collected from 58 MIT custodians. Goodwin Procter established a hotline that members of the MIT community could use to submit information directly to us, without going through MIT’s administration and, as of the date of this
Report, at least 40 individuals have done so.
SECTION VII — INSTITUTIONAL SCANDALS, PRIVATE FUNDING & SHADOW ACCOUNTS
“What bypasses peer review rarely bypasses consequence.”
Science Without Transparency
This section examines how significant portions of high-impact research migrated away from public institutions and into private, lightly regulated ecosystems—often beyond the reach of peer review, public records, or democratic oversight. The Epstein files point to a pattern in which research was convened, funded, and advanced in environments designed to minimize disclosure. These were not illegal laboratories or secret bases; they were parallel knowledge spaces—private conferences, donor-funded labs, offshore entities, and invite-only networks operating alongside mainstream science.
The relevance of Jeffrey Epstein in this context is not technical contribution but facilitation. He appears adjacent to mechanisms that enabled research to proceed without the friction of institutional review, ethical boards, or publication requirements. This section shows how shadow funding does not require secrecy in the cinematic sense—only opacity, fragmentation, and jurisdictional distance. When science exits the public domain, accountability dissolves even as capability accelerates.
Importantly, this section rightly assume nefarious intent behind every private initiative. Many breakthroughs originate outside government funding. The risk emerges when structure replaces scrutiny—when results are decoupled from validation, and when incentives favor silence over disclosure. Section VII explains why some of the most consequential research leaves no public trace—and why that absence itself is a signal. This explains the use exclusive clubs, hosted events and seminars with a 737 corporate jet (Lolita Express) to advance relationship and expedite projects.
Science Without Transparency
1. Institutional Scandals, Fraud & Laundering Money Schemes
The case surrounding Jeffrey Epstein exposed significant institutional blind spots across banking, academia, and the justice system. Financial records revealed the use of shell companies, offshore accounts, and layered transfers that obscured the origin and movement of funds, prompting investigations into potential money laundering and compliance failures. Major institutions—including banks and universities—faced scrutiny over due diligence practices, reputational risk management, and why warning signs were missed or minimized.
While not all associated entities were found criminally complicit, the broader scandal highlighted how elite status, complex financial structuring, and fragmented oversight can enable misconduct to persist within otherwise established institutions.
2. Private Funding Strings & Coercion Strategies
Jeffrey Epstein used private donations and financial patronage to gain proximity to influential academics, executives, and institutions. In elite circles, funding can create subtle but powerful leverage—shaping access, influencing research priorities, opening doors to exclusive networks, and building reputational insulation. While direct coercion is not broadly established in court findings, the pattern shows how dependency on private capital can blur ethical boundaries and discourage scrutiny.
The broader lesson is structural: when prestige, funding, and power converge without transparency and oversight, soft influence can operate long before overt misconduct is recognized.
3. Private Conferences & Invite-Only Symposia
Private conferences function as idea accelerators without records. Attendance is curated, discussions are off-the-record, and outcomes are informal. These settings allow theorists, funders, and strategic actors to exchange insights without reputational or regulatory exposure. While intellectually productive, they bypass the transparency norms that protect scientific integrity.
4. Offshore Research Funding Channels
Offshore structures—foundations, trusts, and special-purpose entities—allow funding to move across borders with minimal disclosure. When applied to research, these channels obscure origin, intent, and accountability. Jurisdictional complexity makes oversight difficult and shields both donors and recipients from scrutiny that would apply in domestic grant systems.
5. Unpublished or Classified Research Outcomes
Not all research is meant for publication. In private ecosystems, results may remain proprietary, confidential, or classified—especially when they intersect with defense, intelligence, or competitive advantage. The files suggest that some work advanced to conclusion without ever entering the academic record, creating knowledge asymmetry between private actors and the public sphere.
6. When Peer Review Disappears
Peer review is science’s primary self-correcting mechanism. When it is absent, replaced by informal validation among insiders, error detection weakens and groupthink strengthens. Private funding environments often substitute trust and reputation for rigorous critique—raising the risk that flawed or biased models propagate unchecked.
7. Why Breakthroughs Remain Unnamed
Breakthroughs remain unnamed when disclosure carries more risk than reward. Publication invites scrutiny, regulation, ethical debate, and loss of control. In private systems, value accrues not through recognition but through possession—who knows first, who knows alone, and who can act before others understand what exists.
Wyden Releases New Analysis Detailing How Top JPMorgan Chase Execs Enabled Epstein’s Trafficking Operation
Continuing Epstein Investigation, Wyden Releases New Analysis Detailing How Top JPMorgan Chase Executives Enabled Epstein’s Sex Trafficking Operation
Scams, Schemes, Ruthless Cons: The Untold Story of How Jeffrey Epstein Got Rich
For years, rumors swirled about where his wealth came from. A Times investigation reveals the truth of how a college dropout clawed his way to the pinnacle of American finance and society.
France investigates ex-minister Jack Lang over Epstein links
The socialist grandee quits his role at a prestigious institute as he is investigated for the "laundering of tax-fraud proceeds".
Epstein Files Show Financial Ties to DOD Deputy Secretary Feinberg
DOD Deputy Secretary Steve Feinberg is referenced in 20 documents in the Epstein files, while the company he founded, Cerberus, appears in 360 files
Why The Epstein Story Never Goes Deeper | Whitney Webb
Why does the Epstein story never seem to go deeper?In this discussion, investigative journalist Whitney Webb explores how powerful institutions, intelligence...
"You Have No Idea About What's Really Happening" | Whitney Webb
This video examines the quiet rise of “pre-crime” governance and why Palantir represents far more than a conventional surveillance company. Drawing on the legacy of post-9/11 intelligence programs, it argues that modern data systems are no longer designed to monitor what people have done, but to algorithmically predict what they might do in the future.
SECTION VIII — HONEY POTS & COMPROMISE OPERATIONS
“Elite control begins where desire meets secrecy.”
How Leverage Is Created
This section examines one of the most structurally significant dimensions of the Epstein case: compromise as a long-term influence mechanism. In intelligence history, leverage is rarely loud or continuously applied. It is created once—through documentation, secrecy, or exposure risk—and then allowed to exist. The mere possibility that damaging material could surface is often enough to shape behavior, mute criticism, redirect funding decisions, or alter institutional alignments for years.
The relevance of Jeffrey Epstein here extends beyond criminal conduct. His residences, private island, ranch, Manhattan townhouse, and aircraft created controlled environments—spaces with curated guest lists, asymmetric information, restricted access, and alleged surveillance capability. Such architectures mirror classic compromise models: isolate, normalize, document, and retain optionality. This section does not presume a single intelligence sponsor or centralized command structure; rather, it analyzes why these environments are inherently valuable to power systems regardless of who ultimately exploits them.
Importantly, this is not a moral indictment of victims or even every associate named in records. It is an examination of structural vulnerability. When careers, reputations, research grants, board seats, security clearances, visas, tenure, and public trust are at stake, both consensual and non-consensual conduct can become leverage. Compromise evolves from isolated acts into infrastructure—where silence, reputational risk management, and institutional containment become the primary outcomes.
How Leverage Is Created
Leverage is created by combining private behavior with asymmetric visibility. One party knows; another does not know who knows. Documentation, witnesses, controlled settings, and selective memory convert moments into long-term influence. The leverage need never be used overtly—its mere existence reshapes choices.
1. Honey Pot Theory: Intelligence & Power History
Honey pots have long been used to identify, recruit, or neutralize targets. Historically applied to diplomats and politicians, the tactic has expanded to include scientists, technologists, and academics whose work influences future capability. The method persists because it is efficient, deniable, and scalable.
2. Sexual Compromise as Control Infrastructure
Sexual compromise functions as infrastructure when it is repeatable, documented, and embedded in trusted environments. It does not require coercion at the outset. Once reputational risk exists, individuals often self-regulate—avoiding scrutiny, declining controversy, or disengaging from oversight—without further prompting.
3. Why Scientists Are High-Value Targets
Scientists and theorists are valuable not for authority, but for trajectory control. Their ideas shape future technologies, policies, and markets. Unlike politicians, they are less trained in adversarial environments and more reliant on institutional protection—making them uniquely vulnerable to reputational pressure.
4. Consent vs. Coercion vs. Career Destruction
Consent does not eliminate leverage. Even fully consensual actions can be reframed when power, age gaps, funding dependency, or institutional rules are involved. The threat is rarely legal prosecution; it is career destruction—loss of funding, tenure, visas, or credibility. This gray zone is where most control operates.
5. Epstein’s Properties as Control Environments
Epstein’s residences and travel settings functioned as controlled environments: private, socially normalized, and insulated from external oversight. Such spaces allow boundaries to blur while maintaining plausible deniability for guests. The properties mattered less as locations than as contexts—where power, access, and vulnerability intersected.
Don't Get Seduced by a Woman - Honeypots and Honey Traps Explained
Honeypots and Honey Traps are operations used to spy and capture victims. This is also practiced in some government operations to catch high-value criminals ...
Brave Supermodel Exposes the Dark Side of Victoria's Secret
The business of beauty can be very ugly, especially in the cutthroat world of modelling. It's an industry that wants to portray itself as the epitome of health and happiness. The reality though is anything but. Anorexia, drug use and bullying are as routine as smiling for the cameras.
Whitney Webb on Epstein & Intelligence Filmed 2020
In this 2020 interview, Whitney Webb outlines the intelligence-linked networks surrounding Jeffrey Epstein, arguing that his operations reflected long-standing intersections between financial elites, academic institutions, and covert power structures rather than an isolated criminal enterprise.
Blackmail Programs & Targets
Whitney Webb EXPOSES How Intelligence Agencies Fund Sex Trafficking, Fascism, & Organized Crime
Whitney Webb on why the CIA teamed with organized crime during WWII, protecting corrupt interests and backing ethnonationalism.Watch the full interview here:...
Former Prince Andrew tried to facilitate Epstein-Gaddafi meeting - C4 News investigation
The Epstein files continue to make waves around the world, costing high-profile people their reputations and jobs. The latest to go is Sultan Ahmed bin Sulay...
Lutnick calls Epstein the 'greatest blackmailer ever' on podcast
Commerce Secretary Howard Lutnick called Jeffrey Epstein the "greatest blackmailer ever" while speaking on a New York Post podcast. Also, a new poll shows 77...
Was Jeffrey Epstein trying to blackmail people for Russia using compromising material? | DW News
Last Friday, US authorities released another batch of files related to Jeffrey Epstein. Epstein, if you need reminding, was a convicted sex offender. He died...
Zorro Ranch Deep Dive: Epstein’s Hidden Compound, Witness Allegations, and What the Files Reveal
Jeffrey Epstein’s Zorro Ranch in New Mexico has long been one of the most mysterious locations tied to his network — and newly released files and reports are...
Epstein’s Ranch Was Way Sicker Than We Thought [Full Overview]
Jeffrey Epstein’s isolated New Mexico property has become one of the most disturbing and least understood parts of this entire story. Online, it’s surrounded by claims - some grounded in documents, some speculative, some genuinely horrifying. I’m not here to give you closure — we’re here to explain why there isn’t any.
🚨DARK SECRETS of Epstein NM COMPOUND Finally EXPOSED!!!
MeidasTouch host Ben Meiselas exposes what really happening in Epstein’s Zorro Ranch in New Mexico and the ongoing cover up to hide it by Trump and others.Sa...
Allegations of bodies buried at Epstein's New Mexico ranch prompt investigation calls
New Mexico officials are urging an investigation into claims of bodies buried at Jeffrey Epstein's Zorro Ranch, following the release of documents related to...
Inside Zorro Ranch: The $24M City Built For Epstein
In a remote stretch of the New Mexico desert, sits a sprawling 10,000-acre compound: Zorro Ranch. But behind it's heavily guarded gates sits a luxurious city...
New Evidence at Epstein’s Ranch? 330 Gallons Of Sulphurıc Acıd Purchased REVEALED
New developments in the Jeffrey Epstein case are raising serious questions once again.Officials in New Mexico are reportedly urging a formal investigation in...
Nov. 12 Epstein files highlight New Mexico ties, Zorro Ranch
Nov. 12 Epstein files highlight New Mexico ties, Zorro RanchKOAT Action 7 News is your home for New Mexico breaking news and weather. For your latest New Mex...
Epstein Code Words (Child Abuse Codes, Ritual Sacrifice, Cannibalism)
People Have Found Epstein's Code Word..
Asmongold Clips / Asmongold Reacts To: After the massive drop of Epstein files people have been sifting through the mails and have found something insane.
Forensic Expert On Epstein's Code Words (Beef Jerky, Pizza, Grape Juice) w/ Dr. G
Mario Nawfal is the host of the largest show on X (formerly Twitter) with guests including Hunter Biden, Elon Musk, President Bolsonaro, President Novak, PM Imran Khan, RFK Jr, Bill Ackman, Marc Cuban, Marc Andreessen and Tucker Carlson reaching millions of people a week and leading the citizen journalism movement.
The “Lolita Express” – Mobility, Access, and Network Logistics
Private Jet Operations as Mobility Infrastructure
Epstein’s private aircraft—often referred to in media as the “Lolita Express”—served as logistical arteries connecting his properties and social network. Flight operations add a mobility dimension to compromise theory: movement across jurisdictions, curated passenger groupings, and compartmentalized travel records.
The Boeing 727 — became a central symbol of how mobility enabled the alleged trafficking network. Flight logs, pilot testimony, and passenger manifests have been scrutinized by investigators, journalists, and civil litigators seeking to map associations, travel patterns, and potential operational timelines.
Beyond the aircraft itself, the jet represents a broader structural question: how private aviation, jurisdictional movement, and elite access can complicate oversight and delay accountability. The aircraft allowed rapid international and domestic movement between key properties, including New York, Florida, the U.S. Virgin Islands, and New Mexico, reinforcing allegations of a geographically distributed operation.
1. FAA Flight Logs Disclosure
Federal Aviation Administration (FAA) flight records and related court-released logs have played a central role in mapping the travel patterns of Jeffrey Epstein, his associates, and passengers aboard his private aircraft. These documents help establish dates, locations, and frequency of travel, though logs alone do not confirm the purpose of trips or activities onboard.
2. Witness Testimonies (Flight Attendants)
Testimony from pilots and flight attendants has provided additional context to flight records, offering details about passenger lists, routing, and onboard procedures. Such accounts contribute to timeline reconstruction but vary in scope and evidentiary weight depending on whether they were sworn statements or media interviews.
3. Victim Reports (Massage Therapist Context)
Victim statements—many describing recruitment through “massage” pretexts—have been central to federal prosecutions. These accounts detail patterns of grooming, transportation, and abuse, forming the evidentiary backbone of trafficking charges brought against Epstein and later against Ghislaine Maxwell.
4. FBO Ground & Service Crew Reports
Fixed-Base Operators (FBOs)—private airport terminals servicing charter and private jets—maintain fueling, ground handling, and service logs. Personnel accounts and service records have occasionally been referenced to corroborate aircraft movements, though such documentation typically confirms logistics rather than passenger activity.
5. Hidden Manifest
The term “hidden manifest” refers to allegations that some passenger records were incomplete, redacted, or privately maintained. While partial manifests have been released through litigation, no verified master list has been publicly confirmed as intentionally concealed by federal authorities.
6. Secret Flights
“Secret flights” is a phrase often used to describe trips not widely disclosed at the time or involving high-profile passengers. However, most known flight data has emerged through court proceedings, civil suits, and investigative reporting. Assertions of undisclosed travel require careful distinction between documented evidence and speculation.
Just Now: Epstein Flight Logs Released — Billionaires Named, Legal Cases Taking Shape
#EpsteinFiles #FlightLogs #FederalInvestigation #epsteincase Newly released Epstein flight log documents have once again pushed high-profile names back into ...
Epstein Flight Logs Released — Billionaires Named, Legal Cases Taking Shape
Newly released Epstein flight logs are sending shockwaves through legal and financial circles after multiple high-profile names surfaced in official records. While inclusion in a flight log does not by itself imply wrongdoing, the disclosure is already reshaping ongoing civil claims, reputational risk assessments, and potential legal strategies.
Lolita Express Masseuse Reveals Lurid Details from Jeffrey Epstein's Private Plane
Chauntae Davis was the air hostess onboard the notorious private jet, Lolita Express, which was owned by billionaire Wall Street tycoon Jeffrey Epstein. INSI...
What really happened on Jeffrey Epstein's private planes | 60 Minutes Australia
Virginia Roberts Giuffre is determined that Jeffrey Epstein's terrible secrets will not be buried with him. Subscribe here: http://9Soci.al/chmP50wA97J Full ...
Epstein’s Plane Was Even Sicker Than We Thought
On the tarmac, it looked like any other jet — a plain white Boeing 727 parked in the Florida sun. But when its doors opened, the passengers weren’t just businessmen. They were presidents, princes, supermodels — and, according to survivors, young girls who never should have been there.
Just Now Epstein Flight Logs Released — Billionaires Named, Legal Cases Taking Shape
#BreakingNews #Epstein #LegalDevelopments #FlightLogsNewly released Epstein flight logs are sending shockwaves through legal and financial circles after mult...
SECTION IX — LITTLE SAINT JAMES – THE PRIVATE ISLAND
Elite Island Hedonistic Paradise, Satanic Ritual Practices
Jeffrey Epstein’s private island, Little Saint James, was more than a residence. It was a controlled environment—geographically isolated, privately owned, and operationally insulated. In systems analysis, geography matters. Physical isolation creates legal ambiguity, reduces oversight, and concentrates power within a defined perimeter. The island functioned as a closed-loop space where logistics, surveillance, and access could be managed without external friction.
Unlike mainland properties embedded in dense social and regulatory environments, a private island allows for total perimeter control. Entry and exit are deliberate. Staff roles can be compartmentalized. Movement is observed and monitored. Visitors operate within a curated ecosystem where norms are set internally. Testimony and court records describe repeated abuse, rape, sexual exploitation of minors and ritual sacrifices occurring there. What distinguishes the island is not merely that crimes happened—but that it was designed to optimize discretion.
This section treats Little Saint James as secret and one of the most secret elite clandestine infrastructures. It examines how controlled geography amplifies dark influence networks, shields illegal activity from scrutiny, and fragments jurisdictional accountability. The island was not symbolic—it was functional.
Elite Island Hedonistic Paradise, Satanic Ritual Practices
Investigations into Jeffrey Epstein revealed allegations that his private island functioned as an isolated environment where wealthy and powerful individuals socialized outside normal public scrutiny. Claims circulating in media, lawsuits, and online discourse range from documented criminal activity to unverified narratives involving ritualistic or organized elite behavior. Distinguishing proven criminal conduct from unsubstantiated claims remains critical in serious research.
1. Who’s Who Guest List | “A-List” Celebrities
Flight logs, photos, and visitor records have linked a range of high-profile individuals to Epstein socially or professionally. Presence in records does not, by itself, establish criminal activity, but mapping social networks has been central to investigative and civil case discovery.
2. Exclusive Female & Male Guests, Couples
Reports and testimony describe tightly controlled social environments with carefully curated guest lists. Allegations suggest selective invitation structures designed to maintain exclusivity and social leverage within elite circles.
3. Corporate Boondoggles | Elite Leaders of Industry
Epstein cultivated relationships with executives and industry leaders, often blending philanthropy, networking, and private events. These environments sometimes blurred lines between social, business, and personal relationships.
4. Top University Department Scientists & Scholars
Epstein funded and hosted academics and researchers, positioning himself as a patron of advanced science. This created reputational and ethical controversy when institutions later reassessed those relationships.
5. Global Financiers & Bankers
His network included individuals from major financial institutions and global investment circles. Investigations examined how financial infrastructure, compliance gaps, and reputation shielding may have enabled prolonged activity.
6. Hidden Cameras & Surveillance Allegations
Some lawsuits and investigative reporting have alleged surveillance within certain properties. These claims center on potential leverage collection, though full technical documentation has not been publicly verified in detail.
7. Targets Selected Prior to Arrival
Victim testimony in criminal cases described grooming pipelines and pre-selection patterns tied to travel, scheduling, and controlled environments.
8. “What Happens on the Island Doesn’t Stay on the Island” (Network Leverage Concept)
The broader investigative theory focuses on power, secrecy, and leverage networks — where information, relationships, and influence extended beyond any single location.
What’s on Jeffrey Epstein’s Private Island?
It's your first look at disgraced financier Jeffrey Epstein’s private island. The island, which is near St. Thomas in the Caribbean, is only accessible by bo...
THE EPSTEIN CASE | The Island Where Little Girls Were Taken And...
Today I will tell you the story of the most terrible island, which at one time was visited by many world stars, from Prince Andrew to US presidents. A crazy place where children were traded and real orgies were arranged with them for those who had money.
Jeffrey Epstein's Private Island Explained
For years, Jeffrey Epstein’s private island was hidden behind money, power, and silence... until newly released files finally exposed what was really there. ...
We Tracked Every Visitor to Epstein Island | WIRED
Even in death, the secrets of disgraced financier Jeffrey Epstein and his infamous private island remain tightly guarded. But in 2024 WIRED conducted an inve...
Inside The Secret Evil Structures of Epstein Island
Hidden deep within the Caribbean, the infamous Epstein Island holds far more than scandal and secrecy—it hides structures that were never meant to be seen. I...
Paris Hilton SNITCHES & EXPOSES Kim Kardashian’s Activities On Epstein Island| Snitching On EVERYONE
Paris Hilton SNITCHES & EXPOSES Kim Kardashian’s Activities On Epstein Island| Snitching On EVERYONESo, Paris Hilton has decided that if she’s going down bec...
Let’s Talk About Jeffrey Epstein’s Island.
A chilling breakdown of Jeffrey Epstein’s private island—its secrecy, survivors’ testimonies, powerful connections, and unanswered questions—examining how Li...
Inside Epstein Island: From abandoned bedrooms to strange objects, watch 'never-before-seen' videos
Dozens of newly released images and videos from Jeffrey Epstein’s private island, Little Saint James, have surfaced, offering the most detailed look yet at t...
Tour Every Building on Jeffrey Epstein’s Island
🗂️ Jeffrey Epstein's island has about two dozen structures littered across it. In this video, we examining each one, with archival photos and videos that wi...
The Strange Books Found on Epstein’s Island
📚 Books Found on Epstein’s Island — Full BreakdownIn this video, we analyze the reported book titles found on Jeffrey Epstein’s island based on public recor...
Whatever Happened To Epstein's Island?
Before his death, sex offender Jeffrey Epstein allegedly used his own private island to host scores of underage girls. Many things about Epstein are still mi...
IX.9 — Geography as Shield
Isolation creates delay. Law enforcement response requires transport coordination, warrants across jurisdictions, and logistical planning. Physical separation slows scrutiny and increases discretion for property owners.
IX.10 — Jurisdictional Complexity
Little Saint James sits within the U.S. Virgin Islands. Federal authority applies—but local governance structures, territorial administration, and maritime logistics create layers of oversight. Complex jurisdiction often dilutes enforcement clarity.
IX.11 — Controlled Access & Guest Management
Private air and maritime transport limited visibility into who visited and when. Flight logs and boat records provide partial transparency, but closed environments reduce incidental witnesses and third-party oversight.
IX.12 — Architectural & Surveillance Control | Strategic Blackmail Operations
Reports describe the island’s structures as private, fortified, and monitored. (cameras recording everything) While public speculation has targeted some architectural features, the essential fact remains: privately owned compounds allow for internally controlled observation and movement management. Setting up a massive blackmail entrap for unknowing island guest.
IX.13 — Staff Compartmentalization
Large private estates rely on layered staff—hospitality, maintenance, security, logistics. Compartmentalization ensures no single employee sees the full operational picture, reducing whistleblowing risk.
IX.14 — Social Normalization in Closed Environments
Closed social settings create accelerated normalization for secret (satanic) dehumanizing criminal behavior. When influential guests observe no visible resistance or external oversight, behavioral boundaries shift. Elite social dynamics reinforce silence through status hierarchy.
IX.15 — Post-Arrest Asset Liquidation & Narrative Shift
Following Epstein’s arrest and death, the island became both evidence and symbol. Its sale and media treatment shifted focus from structural questions to spectacle. Physical sites often focus public outrage while deeper institutional links remain diffuse. Its only a matter of time for these truths to rise to the surface.
Structural Takeaway
The private island was not an anomaly—it was an example of how controlled space magnifies asymmetrical power. When geography, capital, and social status converge, oversight weakens. Breading ground for hidden Satanic and nefarious activities. The lesson is broader than one property: isolated environments—whether physical, legal, or digital—are force multipliers for unaccountable systems.
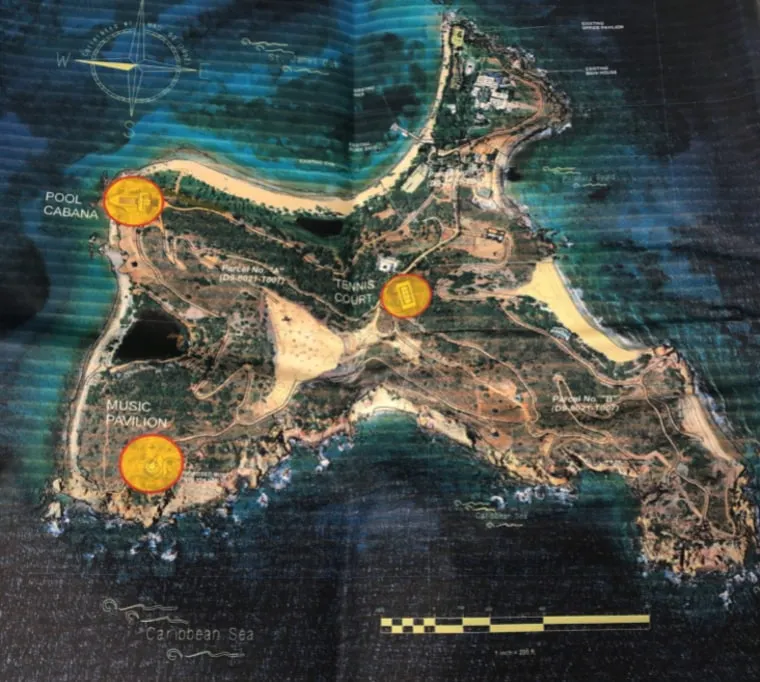
LITTLE SAINT JAMES: UNDERGROUND STRUCTURAL ALLEGATIONS & INFRASTRUCTURE CLAIMS
IX.8 — Underground Structures
Satellite imagery and drone footage have fueled claims of underground facilities beneath structures on Little Saint James. Public observers have pointed to unusual architectural features, hilltop constructions, and sealed entrances as potential evidence of subterranean space. Estimates of 5 to 7 underground levels with an undersea submarine base docking station.
However:
- No publicly released engineering documents confirm extensive underground rooms, facilities, and tunnel networks.
- No court filings have substantiated operational underground detention systems. Holding cells for trafficking?
- Speculation largely stems from fragmented witness testimony rather than verified structural plans. (secret underground facilities are never reported to authorities or architectural plans place in public records)
The unresolved question is not whether 5 stories of room, cells and ceremonial rooms existed—many large estate compounds include them—but whether significant concealed infrastructure existed beyond what has been documented in court filings to date?
At present, such claims remain SUPPRESSED AND SECRET. FBI has restricted access to all evidence confiscated into their custody.
IX.9 — Claims of Submarine Docking Facilities
One of the more persistent narratives suggests the existence of a hidden submarine docking port or underwater access tunnel connected to other island. There is conformation that Ghislaine Maxwell is a licensed submarine pilot.
To date:
- Private submarine operations have been confirmed operating around the islands of Little St James
- Suppressed maritime infrastructure filings indicate specialized docking installations.
- Unknown criminal proceedings introduced evidence of submarine-based transport.
The island did have private dock access suitable for yachts and smaller vessels, which is common for privately owned Caribbean islands. Assertions of submarine facilities remain an active research topic for verification and documentation.
IX.10 — Whistleblower Claims of Underground Infrastructure Persist
When institutional trust collapses, evidence and documentation disappears or remains hidden
Three factors fuel these narratives:
- Hidden undocumented arrivals and departures of trafficked women and children occurred on the island.
- Evidence of $27 million was spent destroying all underground facilities 12 month before the FBI raid on the island.
- Secret architectural opacity invites multiple interpretations of illegal activity.
- The scale of political (Intelligence Agency) protection around Epstein creates suspicion of deeper concealment.
The psychological leap from secrecy to subterranean systems is understandable—new research and evidence continues to come to light.
Structural Analysis Both Hidden or Suppressed
The verifiable infrastructure that mattered most was not subterranean—it was:
- Geographic isolation
- Controlled transport access
- Social Satanic normalization among elites
- Legal and institutional shielding
- Off limits demands to staff and maintenance workers
- Underground Access points confirmed by employees and island contractors
These elements are sufficient to explain how stories persisted.
The introduction of verified structural claims grows stronger as systemic analysis clearly identifies underground facilities
The Evil Design of Jeffrey Epstein Island
Jeffrey Epstein’s private island has long been surrounded by mystery, rumors, and disturbing allegations. But beyond the headlines and court documents lies a...
Inside The Secret Evil Structures of Epstein Island
Hidden deep within the Caribbean, the infamous Epstein Island holds far more than scandal and secrecy—it hides structures that were never meant to be seen. I...
Epstein's 'Tunnels of Terror' are MUCH worse than we thought
This is way more bigger than Epstein. There’s so many evil f**ks in this world that have the money & power to make everything go away.
Victim Testimony Epstein Island
Epstein Survivor: Cameras, Blackmail, A-List Celebrities & The Island | Lisa Phillips
Lisa Phillips is a survivor of the Jeffrey Epstein trafficking network. In this interview, we discuss the island, the recruitment and grooming process, the t...
Surviving Epstein: Lisa Phillips Opens Up About Grooming, Power, and Speaking Her Truth
Lisa Phillips, a former model and Epstein survivor, shares her powerful story in this Stepping Into The Shade Room exclusive interview. In this emotional sit...
SECTION X — NEW MEXICO ESTATE – ZORRO RANCH
“The most effective control systems attacks and destroys identity, not assets.”
Genetic Breeding Experiments & Adrenochrome Labs
Jeffrey Epstein owned a large, secluded property known as Zorro Ranch (now renamed Rancho de San Rafael or San Rafael Ranch), located near Stanley, New Mexico, approximately 30–35 miles southeast of Santa Fe in Santa Fe County. He purchased it in 1993 from the family of former New Mexico Governor Bruce King through entities like the Zorro Trust (later Cypress Inc.), transforming it into a high-desert compound spanning nearly 10,000 acres (core private land around 8,000 acres after adjustments), featuring rugged desert scrub with cholla cactus, grazing Angus cattle, and formerly leased adjacent state trust land (about 1,200–1,244 acres for agriculture/grazing, terminated in 2019). Key structures included a massive 26,700-square-foot mansion (with a large living room, 4,000 sq ft courtyard, and planned extensive amenities), a private airstrip/runway, hangar, helipad, ranch office, firehouse, heated garage, and other outbuildings—designed for extreme isolation and control, over a mile from the nearest public road, ideal for evading scrutiny while hosting victims and guests.
Abuse allegations at the ranch are central to Epstein’s case, with multiple survivors testifying to being groomed and sexually abused there as teenagers or young women. Annie Farmer recounted being lured to the ranch at age 16 in 1996 (via her sister Maria Farmer’s connections), expecting a group student trip but finding herself isolated with Epstein and Ghislaine Maxwell; Maxwell allegedly gave her an inappropriate nude massage, and Epstein groped/harassed her, amid patterns of trafficking, sexual assault, and exploitation facilitated by Maxwell. Other victims described similar experiences of being transported under false pretenses, subjected to escalating assaults in this remote setting, with no full FBI forensic raid ever conducted despite early reports dating to the 1990s.
The ranch features prominently in the recent 2026 Epstein file releases under the Epstein Files Transparency Act (totaling over 3.5 million pages by early February), with mentions exceeding 4,200 in some batches—including investigative records, photos of Epstein with a woman/girl and men/visitors on the property, and unverified sensational claims (e.g., a 2019 anonymous email alleging two “foreign girls” strangled and buried in nearby hills on orders from Epstein and Maxwell, prompting renewed calls for probes but lacking confirmation or follow-up action). These details have intensified scrutiny over institutional failures, including why federal searches were limited or absent, and have spurred New Mexico officials like State Land Commissioner Stephanie Garcia Richard (who urged state/federal investigation into the burial claims in February 2026) and lawmakers (pushing a bipartisan “truth commission” with proposed $2.5 million budget) to demand fuller accountability for alleged crimes, local ties, and unaddressed victim reports.
Current status (as of February 12, 2026): The property was listed for sale by Epstein’s estate in 2021 (initially $27.5 million, later reduced, rumored to ~$18 million), and sold in 2023 to an undisclosed buyer via San Rafael Ranch LLC for an undisclosed price (new owners protested assessed value in 2024, claiming far lower worth). Proceeds supported the estate, creditors, and victim compensation funds. The ranch remains private with no public access or identified owners, while surrounding former state-leased land (vacant since 2019) has been discussed for potential uses like a memorial for victims or wildlife sanctuary. Ongoing state legislative efforts for a truth commission (advocated by Reps. Andrea Romero, Mariana Anaya, and others) focus on unresolved questions, with Rep. Melanie Stansbury and others highlighting “dark” file contents and the lack of comprehensive probes, amid no major new charges but persistent demands for transparency and justice.
Genetic Breeding Experiments & Adrenochrome Labs
Acquisition and Development of Zorro Ranch Epstein acquired the nearly 10,000-acre property in 1993 through trusts and entities like Zorro Trust/Cypress Inc., expanding it with a massive mansion, airstrip, helipad, and outbuildings for maximum privacy and self-sufficiency. The remote high-desert location in Santa Fe County, surrounded by rugged terrain and formerly leased state land (terminated in 2019), was chosen partly for proximity to scientific communities like the Santa Fe Institute. This setup enabled Epstein to maintain seclusion while allegedly conducting exploitative activities away from public oversight.
1. Military–Industrial Complex Social Access
Epstein cultivated relationships with individuals connected to defense, technology, and scientific communities. Social proximity does not equal operational partnership.
2. Nationally Recognized Scientists & Physicists
He funded and hosted respected academics, including physicists and evolutionary theorists. This created ethical controversy, particularly after his 2008 conviction.
3. Main Compound (Approx. 28,000 sq ft Estate)
Zorro Ranch included a large main residence and additional structures, designed for privacy and high-level guests.
4. Private Airstrip
The property reportedly included an airstrip capable of accommodating private aircraft, consistent with Epstein’s broader travel patterns.
5. Alleged Government Connections (Unverified Claims)
Online narratives reference maglev systems and covert infrastructure links to federal labs. There is no publicly verified evidence supporting these claims.
6–7. Los Alamos & Sandia Laboratories
Los Alamos National Laboratory and Sandia National Laboratories are major federal research institutions located in New Mexico. No official documentation has established operational partnerships between these labs and Epstein’s ranch.
8. Underground Facility Claims
No publicly confirmed architectural records or legal findings support the existence of a major underground research complex at Zorro Ranch.
9–10. Genetic Breeding / Cloning Allegations
Epstein did express controversial ideas about genetics and transhumanist-style reproduction concepts in reported conversations in the Epstein files and records. However, the illuminati Satanic Cults have bred 1000’s of bastards for centuries. Technological advancements have created breeding farms with far greater success and numbers. The science has evolved into cloning labs, or biological experimentation facilities in deep unground labs on the property.
Adrenochrome Allegations
Claims involving adrenochrome harvesting or ritual extraction originate from witness testimony narratives and are supported by confirmation from multiple sources. Epstein niece and workers at the ranch.
Key Survivor Testimonies Linked to the Ranch Annie Farmer testified to abuse at age 16 in 1996, lured expecting a group educational experience but isolated for grooming and assault by Epstein and Maxwell. Maria Farmer reported early 1996 concerns after related incidents, including Epstein allegedly stealing nude images of the sisters. Other accusers, like Virginia Giuffre and various trial witnesses, described repeated trafficking and sexual abuse at the property over years.
1.3 Patterns of Grooming and Abuse at the Property Victims were often flown or transported to the ranch under pretexts like massages, work, or mentorship opportunities, then subjected to sexual assaults, groping, forced encounters, and group acts in isolated settings. The extreme remoteness amplified psychological control—limited escape, constant surveillance, and dependency on Epstein’s resources—eroding victims’ sense of agency and fostering shame. Testimonies underscore normalization of exploitation in this “private” desert compound.
1.4 Investigative Gaps and Lack of Full Searches Despite survivor complaints from the 1990s (e.g., Maria Farmer’s reports) and post-2019 scrutiny, no comprehensive FBI forensic search occurred at Zorro Ranch, unlike other Epstein properties. Recent 2026 file releases highlight this oversight through records and photos but no breakthroughs. New Mexico officials, including Land Commissioner Garcia Richard and Rep. Stansbury, criticize federal inaction and call for renewed probes into unaddressed crimes.
1.5 Recent Developments and Unverified Claims in 2026 Files The DOJ’s Transparency Act releases include ranch photos (e.g., Epstein with visitors/dogs), investigative notes, and a resurfaced 2019 anonymous email alleging burials of strangled girls, sparking Garcia Richard’s February 2026 call for investigation (forwarded to AG Raúl Torrez and U.S. Attorney). Claims remain unsubstantiated/sensational, with no confirmed evidence or charges. Officials urge caution amid privacy redactions while demanding answers on potential crimes.
1.6 Current Status and Calls for Broader Justice Sold in 2023 to private owners (San Rafael Ranch LLC), the ranch is inaccessible and renamed, but its history fuels advocacy for systemic change. State efforts push a truth commission to examine Epstein’s New Mexico activities, local enablers, and investigative failures. Survivors’ resilience drives demands for unredacted transparency, memorials on related lands, and prevention of elite-enabled exploitation in isolated sites.
Zorro Ranch Deep Dive: Epstein’s Hidden Compound, Witness Allegations, and What the Files Reveal
Jeffrey Epstein’s Zorro Ranch in New Mexico has long been one of the most mysterious locations tied to his network — and newly released files and reports are...
"Girls Were BURIED On Orders Of Jeffrey" - Volksgiest On The Zorro Ranch, MKUltra & CIA...
Mario Nawfal is the host of the largest show on X (formerly Twitter) with guests including Hunter Biden, Elon Musk, President Bolsonaro, President Novak, PM Imran Khan, RFK Jr, Bill Ackman, Marc Cuban, Marc Andreessen and Tucker Carlson reaching millions of people a week and leading the citizen journalism movement.
Bodies Buried on Epstein’s Ranch?
Newly released documents in the Epstein Files include an anonymous 2019 email claiming bodies may be buried near Jeffrey Epstein’s Zorro Ranch in New Mexico....
Los Horrores Depravados de la "Hacienda Secreta" de Epstein
Jeffrey Epstein tenía una hacienda secreta en Nuevo México llamada Rancho Zorro donde pasaron muchas cosas perturbadoras. En este video documental, veremos l...
Epstein’s Ranch Was Way Sicker Than We Thought [Full Overview]
Jeffrey Epstein’s isolated New Mexico property has become one of the most disturbing and least understood parts of this entire story. Online, it’s surrounded by claims - some grounded in documents, some speculative, some genuinely horrifying. I’m not here to give you closure — we’re here to explain why there isn’t any.
🚨DARK SECRETS of Epstein NM COMPOUND Finally EXPOSED!!!
MeidasTouch host Ben Meiselas exposes what really happening in Epstein’s Zorro Ranch in New Mexico and the ongoing cover up to hide it by Trump and others.Sa...
Allegations of bodies buried at Epstein's New Mexico ranch prompt investigation calls
New Mexico officials are urging an investigation into claims of bodies buried at Jeffrey Epstein's Zorro Ranch, following the release of documents related to...
Inside Zorro Ranch: The $24M City Built For Epstein
In a remote stretch of the New Mexico desert, sits a sprawling 10,000-acre compound: Zorro Ranch. But behind it's heavily guarded gates sits a luxurious city...
New Evidence at Epstein’s Ranch? 330 Gallons Of Sulphurıc Acıd Purchased REVEALED
New developments in the Jeffrey Epstein case are raising serious questions once again.Officials in New Mexico are reportedly urging a formal investigation in...
Nov. 12 Epstein files highlight New Mexico ties, Zorro Ranch
Nov. 12 Epstein files highlight New Mexico ties, Zorro RanchKOAT Action 7 News is your home for New Mexico breaking news and weather. For your latest New Mex...
SECTION XI — INTELLIGENCE AGENCY BLACKMAIL MECHANICS
“Accountability fails not by denial, but by controlled delays.”
Global Elite Entrapment Schemes; From Behavior to Compliance
This section explains how compromise matures into control—not through constant threats, but through durable uncertainty. In the Epstein files, leverage does not appear as repeated coercion or explicit demands. It appears as architecture: documentation capacity, selective witnesses, controlled environments, and the quiet understanding that exposure is possible. Once established, this architecture converts isolated behavior into long-term compliance without the need for overt enforcement.
The relevance of Jeffrey Epstein here is not limited to misconduct. His social ecosystem illustrates how blackmail functions in modern elite contexts: reputational risk outweighs legal risk; career damage outweighs criminal consequence; and silence is often the most rational response. This section clarifies why blackmail is effective even when it is never visibly used—and why its effects persist long after the compromising moment.
Crucially, Section IX reframes blackmail as an outcome, not an act. The objective is rarely obedience to specific orders. It is constraint—narrowing what targets will say, fund, publish, or challenge. When enough people self-censor, systems stabilize without visible coercion. This is how leverage scales.

Global Elite Entrapment Schemes; From Behavior to Compliance
From Behavior to Compliance
Behavior becomes leverage when it is captured within a context of power asymmetry. The transition does not require wrongdoing beyond the initial act; it requires only that one party controls the narrative and timing of disclosure. Compliance emerges not as submission, but as avoidance—avoiding scrutiny, controversy, and risk.
1. How Information Becomes Leverage
Information becomes leverage when it is exclusive, credible, and ambiguously held. The target need not know exactly what exists or who possesses it—only that exposure is plausible. This ambiguity multiplies power by forcing the target to assume worst-case scenarios in every decision.
2. Digital Evidence, Witnesses & Plausible Deniability
Modern blackmail relies on redundancy. Digital records, witnesses, and circumstantial proof create layers that are individually deniable but collectively persuasive. This structure protects the holder of leverage while increasing pressure on the target, who faces reputational judgment rather than a legal standard of proof.
3. Why Blackmail Doesn’t Require Constant Use
Effective blackmail is set-and-forget. Once leverage is established, reminders are unnecessary. The target internalizes risk and adjusts behavior proactively. Overt threats increase exposure; silence preserves control. The absence of action is often the clearest indicator that leverage exists.
4. Self-Censorship as the Real Outcome
The primary outcome of blackmail is not obedience—it is self-censorship. Targets withdraw from sensitive research, decline leadership roles, avoid public statements, or disengage from oversight. Over time, this creates informational voids that shape institutional direction without visible interference.
5. Silence as a Survival Strategy
For many targets, silence is rational. Speaking invites scrutiny, escalation, and secondary exposure. Institutions rarely reward whistleblowing when reputational risk is high. As a result, silence becomes a survival strategy—not evidence of innocence or guilt, but of structural pressure.
6. Files Expose Top Global Elites (identified)
Epstein Files; Court filings, civil depositions, unsealed records, and flight logs related to Jeffrey Epstein have identified a range of high-profile political leaders, business executives, academics, royalty, and celebrities who had social or professional contact with him. In some cases, names appear in travel logs, address books, email records, or testimony; however, inclusion in documents does not automatically imply criminal involvement.
The significance of these disclosures lies less in sensational exposure and more in understanding how elite social networks operated—how access, influence, philanthropy, and proximity to power intersected. Distinguishing documented association from proven misconduct remains essential when evaluating which figures were merely present in records and which faced legal scrutiny or credible allegations.
7. Israeli Intelligence Connections
There have been persistent allegations and media discussions suggesting possible links between Jeffrey Epstein and Israeli intelligence, often referencing the Mossad. These claims typically center on the theory that Epstein operated a blackmail network targeting powerful political, academic, and business figures. However, to date, no court ruling, official intelligence finding, yet witness and the alternative media confirmed that Epstein was working on behalf of Israeli intelligence and many other government agencies. The claims have grown from not just a commentary, but independent investigators, and associations with Maxwell and other known intelligence agents
It is also frequently noted that Epstein maintained relationships with prominent individuals connected to Israel, including former Israeli Prime Minister Ehud Barak, who acknowledged meeting Epstein but denied knowledge of criminal conduct. While such associations have fueled suspicion, association alone does not constitute proof of an intelligence operation. As with many aspects of the Epstein case, the gaps are closing as unverified evidence reveals significant proof of hidden connections to Israel.
Global Intelligence Ties
Epstein’s Israel links and everything else ignored by mainstream media | The Listening Post
The Epstein files dump has led to days of intense media coverage, revealing how powerful elites around the world engaged in either illegal or morally reprehe...
The Epstein Mossad Connections Have Gone Mainstream
Robert Maxwell was given a state funeral in Israel.. he stole my uncles pension, along with thousands of other uk workers. His offspring are, like him, vile, to the extreme.
The Government Is Hiding Something Much Worse Than Epstein — Former CIA Spy Explains
True Classic: Upgrade your wardrobe at https://trueclassic.com/impactShopify: Sign up for your one-dollar-per-month trial period at https://shopify.com/impac...
CIA Spy: "Jeffrey Epstein Was Most Likely A Foreign Spy" - Here's Why... | Andrew Bustamante
Ghislaine's father served the Mossad and Ghislaine was Jeffrey's handler.....do the math.
Epstein Files Reveal Scandal’s Global Reach. What’s Next for Europe’s Elite? | Amanpour and Company
A political crisis is unfolding in Britain after the latest release of the Jeffrey Epstein files revealed new details of former Labour politician Peter Mande...
Arms, Israel & Epstein: These Are The Facts
In the wake of the latest Mandelson revelations – including the leaking of sensitive government information to Jeffrey Epstein – questions are now quite righ...
PROOF: Epstein’s Disturbing Mossad Ties Explained by Nick Bryant
Journalist and author Nick Bryant dives into the horrific details of Epstein’s emails including arms deals with former Israeli Prime Minister Ehud Barak and ...
Global Elite Identified
Epstein Files | Top 100 Names
100 Celebrities from the Epstein Files.
Epstein merely was manager and scapegoat of a Israeli-secret service owned blackmail resorts making their international politics so "successful"
Epstein Files | 100 Famous Figures
The US Justice Department has released over 3 million pages, 2,000+ videos, and 180,000 images in the latest Epstein Files drop — the largest transparency pu...
The Billionaires Named In The Epstein Files
Epstein shared emails, flights, and meals with some of the richest people on the planet. Here's how these billionaires made their money and how they were con...
Epstein’s SICK Messages To Billionaire REVEALED
Support our work:http://novara.media/supportBuy Novara Media merch:https://shop.novaramedia.com/Discuss the show on Reddit:https://www.reddit.com/r/Novara_Me...
Joe Rogan EXPOSES ALL Celebrities NAMED in Epstein Files in Just 30 Minutes
#JoeRogan #EpsteinFiles #JeffreyEpsteinJoe Rogan EXPOSES ALL Celebrities NAMED in Epstein Files in Just 30 MinutesKeep watching for nonstop updates on celebr...
Jeffrey Epstein: How a Government Spy Blackmailed America
Go to https://buyraycon.com/MOONYTOPEN to get 20% off your order of Essential Open Earbud
25 Epstein Insiders Cut Secret Deals: Ghislaine Maxwell Bombshell Court Filing
Ghislaine Maxwell has filed a new court petition claiming that dozens of associates connected to Jeffrey Epstein were never charged and instead reached confi...
Bill Gates on the Run After Epstein Files EXPOSE HIM
While most people are focused on the Epstein files themselves, Bill Gates has been making moves quietly in the background — selling off pieces of his legenda...
The Terrifying Truth of Epstein’s "Inner Circle"
https://www.patreon.com/c/TheTeawithMyriamFrancoisWhy did some of the world's most powerful men engage in such a "depraved and terrifying" behaviour? In this...
The Epstein Files: Blackmail, Trafficking, and Money Laundering
Jeffrey Epstein's involvement in the BCCI network, given Jeffrey's involvement in the 1990s with all the foreign policy activities happening in the Middle East at that time, given Jeffrey Epstein's, you know, involvement through, you know, the the early 2000s Clinton era and everything, given his involvement in everything from Israeli to Saudi to British to French high level government officials, can you Jeffrey Epstein was investigated by the the SEC in the 1980s
Epstein Evidence: Blackmail Claims & Clinton Connection | REWIND
Newly unsealed Jeffrey Epstein documents reveal disturbing details, including Bill Gates’ “rambling” emails to Epstein, potential connections to Bill Clinton...
EU & British Royals Exposed
4 Royals Publicly Named in the Epstein Files | Shocking Royal Connections to Jeffrey Epstein | LIVE
Recently unsealed court documents connected to convicted sex offender Jeffrey Epstein have once again shaken the global elite — including members of royal fa...
Ghislaine Maxwell FINALLY Reveals the TRUTH on Meghan, and its DEVASTATING
The Tallahassee Tapes: 12 hours of censored secrets. "The Flower": Decoding Maxwell’s terrifying nickname for Meghan. Fergie’s Dark Role: Was...
Royal Sarah 'Fergie' Ferguson storms out of fiery interview | 60 Minutes Australia
Duchess of York Sarah Ferguson fires up when asked about her scandals. ► WATCH Full Episodes on 9NOW: https://9now.app.link/uNP4qBkmN6 ► Subscribe here: http...
Sarah Ferguson companies closing after connections to Epstein revealed
The former Duchess of York is seeking to dissolve six of her companies after DOJ documents revealed her close ties to Jeffrey Epstein and convicted associate...
Epstein In Threesome With Ex PM & Ghislaine Maxwell, Claims Royal Biographer
Oooh, scandalous threesome.... But what about the children and cannibals?? Mainstream Media continue to triple-down on the political scandal and not the victims- I'm going insane
She Stayed At Epsteins House -1000 Emails (Part 1)
The Norwegian royal family may be facing one of its biggest controversies in decades.New reporting says newly released Epstein related files and email record...
British Royal Prince Andrew
New claim Epstein sent woman to UK to have sex with Andrew is under police review | BBC News
Police are reviewing new allegations that Jeffrey Epstein sent a woman to Andrew Mountbatten-Windsor in the UK, for a sexual encounter at his residence, the ...
Epstein files: UK fallout over Andrew and Mandelson | Global News Podcast
Photos of Andrew Mountbatten-Windsor, formerly Prince Andrew have been scattered around an English village ahead of a visit by his brother, King Charles. Cop...
Prince Andrew: Fall From Grace | Timeline of Duke's Downfall | 9 News Australia Documentary
Prince Andrew. War hero, Queen Elizabeth's favourite son, the Duke of York. Born into a life of privilege and duty, destined to serve the Crown as a senior m...
Prince Andrew’s Life “Being Eroded" by Past Behaviour, says Giuffre Memoir Co-writer | BBC Newsnight
What is in Virginia Giuffre's memoir and what does it mean for Prince Andrew? Amy Wallace, co-writer of Virginia Giuffre’s posthumous memoir, speaks to Newsn...
Epstein's Royal Emails Exposed in New Doc Dump
A massive release of Justice Department records is exposing new details about Jeffrey Epstein’s ties to the British royal family, including post-conviction e...
Second Epstein victim claims she was sent to UK for sex with Andrew | BBC News
A second woman is alleging that she was sent to the UK by Jeffrey Epstein for a sexual encounter with Andrew Mountbatten-Windsor, her lawyer has told the BBC...
Andrew’s ‘REAL Timeline’ Revealed As Epstein Mansion Stay Lasted Nine Days, Not Four | WATCH
Newly analysed emails reported by the Daily Mail challenge Andrew’s account of his 2010 visit to Jeffrey Epstein’s New York mansion, revealing a nine-day sta...
Prince Andrew & the Epstein Scandal: The Newsnight Interview - BBC News
In a Newsnight special, Emily Maitlis interviews the Duke of York as he speaks for the first time about his relationship with convicted paedophile Jeffrey Ep...
SECTION XII — ELITE HUMAN TRAFFICKING & CHILD SEX ABUSE
“The most effective control systems attacks and destroys identity, not assets.”
Why Sex Is a Powerful Tool of Control
This section addresses the darkest and most legally substantiated dimension of the Epstein record: organized sexual exploitation, including trafficking and the abuse of minors. In the files, Jeffrey Epstein is not portrayed as an isolated offender acting impulsively. The evidence points to repeatable logistics—recruitment pathways, transportation, controlled residences, financial inducements, and silence mechanisms—that align with recognized trafficking patterns. The importance of this section is not sensationalism; it is understanding how sexual exploitation functions as infrastructure within elite power systems.
Sex is uniquely effective as a control mechanism because it operates at the intersection of shame, fear, secrecy, and identity. Unlike financial crimes, sexual crimes carry enduring reputational damage that does not expire with settlements or time. When abuse is embedded within elite social and professional environments, victims are isolated and perpetrators are shielded by status asymmetry. This section explains why trafficking networks that service powerful clients are resilient: they exploit psychological barriers that deter reporting, investigation, and accountability.
Crucially, Section X distinguishes documented facts from inference. Epstein’s trafficking and abuse are proven in court records, victim testimony, and corroborating evidence. What the files illuminate further is scale and facilitation—how such crimes persist when supported by money, access, mobility, and institutional failure. The objective here is not to expand blame indiscriminately, but to analyze why these crimes recur at elite levels and why exposure is so rare.
Why Sex Is a Powerful Tool of Control
1. Sexual Exploitation as a Control Mechanism
Sexual exploitation binds silence through shame. It compromises victims and witnesses while creating mutual vulnerability among perpetrators. Unlike financial leverage, sexual leverage attacks identity and social standing, making resistance psychologically costly and disclosure risky even years later.
2. Trafficking as a System, Not an Accident
The files indicate organized recruitment (often targeting the young and economically vulnerable), transport across jurisdictions, scheduled encounters, and payment structures. These are hallmarks of trafficking systems—not spontaneous abuse. Systems persist because roles are compartmentalized: recruiters, facilitators, transporters, hosts, and payers rarely intersect openly.
3. Jurisdiction Hopping & Legal Evasion
Movement across states and countries fragments enforcement. Differing age-of-consent laws, evidentiary standards, and prosecutorial priorities create gaps traffickers exploit. This mobility also intimidates victims, who face unfamiliar legal systems and limited support.
4. Financial Inducements & Dependency
Payments, gifts, housing, and promises of opportunity create dependency. Even modest sums can be coercive when paired with instability. Financial inducement blurs consent while masking exploitation as “choice,” a narrative that benefits abusers and complicates prosecution.
5. Institutional Failure & Shielding Effects
Elite status attracts institutional deference. Schools, employers, charities, and even law enforcement may hesitate, delay, or narrow inquiries to avoid reputational damage. This shielding effect does not require conspiracy—only risk aversion.
6. Silencing Mechanisms: NDAs, Settlements, and Intimidation
Non-disclosure agreements, civil settlements, and informal intimidation suppress testimony. While some mechanisms are legal, their cumulative effect is truth suppression, especially when victims lack resources for prolonged legal battles.
7. Victim Impact & Long-Term Harm
Trafficking and abuse produce durable harm—psychological trauma, disrupted education, health consequences, and lifelong vulnerability. These outcomes are not collateral; they are predictable results of exploitation systems and should inform accountability and restitution.
8. Why Exposure Is Rare—and Why It Matters
Exposure threatens not just individuals but networks. When crimes intersect with wealth, prestige, and mobility, incentives align to minimize scrutiny. Section X underscores why dismantling such systems requires structural reform: survivor protections, jurisdictional cooperation, transparency around settlements, and independent oversight.
What the newly released Jeffrey Epstein documents reveal about his sex-trafficking ring
Thousands of court documents tied to Jeffrey Epstein have been made public as part of a settled lawsuit involving one of his victims. The records detail Epstein’s sexual abuse and trafficking of underage girls and include the names of 150 people who were in contact with him. Geoff Bennett discussed more with Julie K. Brown, author of “Perversion of Justice: The Jeffrey Epstein Story.”
How Jeffrey Epstein Allegedly Built His Sex Trafficking Ring
"Epstein created a vast network of underage victims for him to sexually exploit in locations including New York and Palm Beach," prosecutors said.
New documents in the Jeffrey Epstein case detail how girls were recruited to his home
The records previously released include names of people in the late financier’s orbit and depositions from women who say they were recruited for his alleged sex trafficking network.
FBI concluded Jeffrey Epstein wasn’t running a sex trafficking ring for powerful men, files show
The FBI pored over Jeffrey Epstein’s bank records and emails
Pizza Gate was REAL: Epstein Was Behind it | With Ben Swann
Ben Swann joins the show to discuss breakthroughs in his Pizzagate investigation following the release of over 3 million Epstein files. Follow Ben on X: http...
The Epstein Files Expose Disturbing Wayfair “Orders”
Disturbing #Epstein #Trump Story revolving around the Wayfair conspiracy Subscribe to 'Stories With Matt' my new channel where these true crime stories (and ...
Richmond hotel named in Epstein files, alleged site of child sex trafficking
A Richmond hotel was named in the most recent batch of investigative files on Jeffrey Epstein, with an anonymous individual claiming they and other children ...
SHOCKING New Files Show Codeword for EATING People
►Grab some brand new VFT merch here https://valhallavft.myshopify.com►Sign up for our Patreon For Exclusive and Behind the scenes content: patreon.com/Valhal...
Epstein Photos & Video Files
DO_NOT_RELEASE_Jeffrey_Epstein_3950_photos.mp4
Jeffrey Epstein files releasedMusic in video https://open.spotify.com/album/3ISYuW9erQ6mQskezh103r
30 Photos from Epstein Dump That Will Blow Your Mind
A new release of photographs tied to Jeffrey Epstein is raising fresh questions — and a lot of speculation. The images, obtained by House Oversight Committee...
19 'Intimate' Epstein Videos Hidden in Files Drop
More than 2,000 videos have been released under the Epstein Files Transparency Act. We dug through the hours of footage to find the most disturbing clips. La...
What the Epstein Files Show on Video
13 days ago
Someone said if they release everything the system will collapse and I’m like SO WHAT? If this is the stuff the system is doing, protecting, hiding, IT ALL DESERVES TO BURN!!!
Videos in Epstein files reveal disturbing look into Jeffrey Epstein's private life
The videos released in the latest batch of Epstein files provide a disturbing look into the convicted sex offender's life. The Free Press video journalist Ta...
OMG: 100+ Epstein Videos Release & It's INSANE 😳
Here are all the videos and footage from the Epstein Files that have been released! Here is my reaction and thoughts on the situation.Original video: https:/...
SECTION XIII — SATANIC ELITE RITUAL SACRAFICE | WORSHIP OF BAAL
“The most effective control systems attacks and destroys identity, not assets.”
Elite Satanic Cults, Secret Clubs & Private Institutional Infiltration
Claims of satanic ritual sacrifice practices among global elites have circulated for decades, often framing powerful figures in politics, finance, entertainment, and business as participants in secret cults that engage in child abuse, torture, and ritualistic killings to gain supernatural power or maintain control. These theories frequently invoke ancient deities like Baal or Moloch—historically linked in some religious texts to child sacrifice—and allege that modern elites revive such practices through hidden networks, blending sexual exploitation with occult symbolism. In the context of Jeffrey Epstein’s case, recent 2026 file releases under the Epstein Files Transparency Act have reignited speculation, with unverified mentions (e.g., a bank account reference to “Baal,” rare religious artifacts like Kiswa cloth from Mecca, or anonymous tips) interpreted by some as evidence of demonic worship or ritual abuse, despite no corroboration in official records.
These narratives draw from historical moral panics, including the 1980s–1990s “Satanic Panic,” where widespread but unsubstantiated allegations of ritual abuse in daycares and communities led to wrongful convictions before being largely debunked by investigations finding no evidence of organized satanic cults committing mass sacrifices. Modern iterations, amplified by QAnon and related movements, portray Epstein’s trafficking network as part of a broader “satanic cabal” involving adrenochrome harvesting, child sacrifice, or Luciferian rituals to harvest power from innocence. While Epstein’s documented crimes involved sex trafficking and abuse of minors, no credible evidence from court records, FBI investigations, or the millions of released pages supports claims of literal satanic rituals, human sacrifice, or occult ceremonies—terms like “occult” appear only in mundane medical contexts (e.g., occult blood tests).
The persistence of these theories reflects deeper societal anxieties about elite impunity, institutional failures, and the erosion of trust in powerful institutions, often merging legitimate outrage over Epstein’s enablers with unsubstantiated supernatural elements. Fact-checkers and researchers note that such claims frequently recycle antisemitic tropes (e.g., blood libel recast as modern child exploitation) or sensationalize isolated details without proof. While survivors’ accounts of psychological manipulation and control in Epstein’s network align with mechanisms that destroy identity through trauma and dependency, extending this to organized global satanic sacrifice remains in the realm of conspiracy without evidentiary support.
Elite Satanic Cults, Secret Clubs & Private Institutional Infiltration
1. Luciferian vs. Modern Satanism
Luciferianism and modern Satanism are often conflated but differ significantly. Contemporary organizations like the Church of Satan (founded by Anton LaVey) are largely atheistic and symbolic, emphasizing individualism rather than literal devil worship. Luciferian traditions, in some interpretations, treat “Lucifer” as a symbol of enlightenment or rebellion. Scholarly analysis distinguishes symbolic philosophy from claims of literal ritualistic activity.
2. Ritual Practices & Transgressive Symbolism
Across history, various religious and esoteric traditions have used ritual, inversion, or taboo symbolism as psychological or initiatory devices. In modern discourse, “ritual” is frequently used metaphorically, while allegations of organized elite ritual abuse require evidentiary support and careful verification.
3. Power Acquisition & Elite Networking
Secret societies, exclusive clubs, and elite networking environments have historically functioned as relationship-building mechanisms. From fraternal orders to policy think tanks, these networks consolidate influence — though presence in exclusive circles does not equate to occult activity.
4. Archetypes of “Demonic Entities”
Figures described as “demonic” in theology often represent archetypes — chaos, ego, temptation, shadow — within mythological or psychological frameworks. Scholars frequently interpret these symbols through literary, Jungian, or comparative-religion lenses rather than literal ontology.
5. Baal & Ancient Ritual Symbolism
Baal was a title associated with ancient Near Eastern deities, particularly in Canaanite traditions. Biblical texts portray Baal worship polemically, often linking it to idolatry or moral corruption. Modern references to Baal are typically symbolic or rhetorical rather than tied to verified contemporary worship structures.
6. Evidence Classification Protocol
When researching sensitive subjects, a disciplined evidence framework is critical: Tier 1: Court-verified facts and convictions. Tier 2: Documented associations (logs, financial records, sworn testimony). Tier 3: Civil allegations not criminally proven. Tier 4: Unverified claims or internet-origin narrative.
The Terrifying True Story Behind The Rothschild Surrealist Ball
The Terrifying True Story Behind The Rothschild Surrealist BallDo you think the Rothschild Surrealist Ball was just a weird 1970s elite costume party—rich pe...
Who Is Baal According to Islam: And Why Do The Elites Worship Him ?
Who was Baal, and why does the Quran mention him by name?Baal is often described online as an ancient pagan god, a demon in occult texts, or even a secret sy...
Inside Bohemian Grove: Rituals, Power, and Secrets of the ELITE
Every July, the world's most powerful men vanish into the redwoods of Northern California for a secretive retreat known as Bohemian Grove. Presidents, CEOs, ...
Epsteins Dinner Rituals With Celebrities Have Been Named
Epsteins Dinner Rituals With Celebrities Have Been NamedX: https://x.com/TruRedpolitics
The #1 Darkest Ritual the Global Satanic Cult Performs | Ian Carroll
Is there a secret satanic cult operating in the U.S.? Investigative journalist Ian Carroll exposes shocking claims about a global network of occult elites wh...
Paul Hutchinson: “Epstein Was Groomed to Join a Century-Old Luciferian Network”
Was Epstein groomed to serve a centuries-old Luciferian network? In this eye-opening sit-down, Paul Hutchinson reveals how Epstein's rise wasn’t just shady—it was engineered. From intelligence ties to blackmail ops, and a headmaster who wrote about ped*phile aliens controlling the world, Hutchinson outlines the chilling possibility that Epstein was part of a deeper, organized power structure.

Anya Wick | Jeffrey Epstein’s Niece
Anya Wick, who identifies herself as Jeffrey Epstein’s niece, has publicly shared detailed and disturbing allegations involving ritualistic abuse and elite networks. In interviews, including one with Shaun Attwood, she claims that members of her family were involved in a generational cult referred to as the “Cult of Baal,” characterized by satanic practices and the ritual abuse of children. Wick describes being subjected to abuse from a young age, often in settings involving powerful individuals, and suggests that these practices were part of a broader system of control and secrecy.
Wick’s accounts include assertions that prominent figures, including politicians and entertainment industry leaders, were either participants in or complicit with these alleged practices. She recounts experiences at locations like Bohemian Grove and mentions encounters with individuals such as Bill Clinton, implying their involvement in the broader network of abuse. However, it’s important to note that these claims are based on her personal testimony and have not been independently verified.
While Wick’s allegations are serious and have garnered attention, they tell a hidden pattern of evil. New calls for official investigations and legal proceedings. The Department of Justice’s released Epstein files do not contain evidence supporting claims of satanic rituals or organized occult activity connected to Epstein or his associates. As such, while Wick’s testimony contributes to the discourse on abuse of children and evil based power structures, it should be approached with new calls for witness to come forward to further substantiate her claims.
1. Survivor Testimony & Pattern Analysis
Examines recurring behavioral, environmental, and psychological patterns reported across survivor accounts in elite abuse cases. Focus includes grooming escalation models, dependency creation, isolation tactics, and power imbalance exploitation. Also evaluates cross-case consistency while recognizing the complexity and variability of trauma narratives and memory recall under stress.
2. Forensic & Evidentiary Threshold Challenges
Analyzes structural barriers to proving organized abuse networks in court. Includes absence of centralized crime scenes, multi-jurisdiction evidence fragmentation, delayed reporting timelines, witness intimidation risk, and evidentiary standards required to prove coordinated criminal conspiracy versus individual criminal acts.
3. Institutional Response Patterns
Studies how major institutions historically react when allegations intersect with power, wealth, or political influence. Focus includes delayed investigative action, internal reputation risk management, legal settlement strategies, and how bureaucratic inertia or risk aversion can slow or fragment accountability processes.
4. Historical Moral Panic vs Documented Crime
Separates historically documented abuse crimes from large-scale social fear cycles. Examines how moral panics can distort investigative priorities while also analyzing how real abuse cases can be dismissed or obscured when they become entangled with exaggerated or unverified claims.
5. Elite Power Shielding Mechanisms
Explores how high resource concentration can influence legal outcomes, media framing, and social credibility. Includes legal defense asymmetry, access to crisis reputation management, social status bias, and how elite network structures can slow external scrutiny or discourage whistleblowing.
6. Information Warfare & Narrative Weaponization
Examines how abuse allegations can be amplified, distorted, or exploited within political, geopolitical, or social conflict environments. Includes narrative seeding, disinformation blending with real cases, strategic media amplification, and weaponization of moral outrage for influence operations.
7. Psychological Trauma & Memory Reliability Research
Reviews peer-reviewed research on trauma encoding, memory fragmentation, delayed recall, and the effects of coercion and fear on witness reporting. Also examines legal debates around recovered memory testimony, expert witness methodology, and evolving neuroscience of trauma recall.
8. Closed Social Network Risk Environments
Analyzes environments where oversight is limited due to social exclusivity, private funding, or controlled access. Focus includes how isolation, social hierarchy pressure, and lack of external observation can create conditions where misconduct is harder to detect or report.
9. Financial Flow Mapping in Abuse Investigations
Focuses on tracing financial structures that may support or conceal criminal behavior. Includes shell corporations, layered foundation funding, donor influence pathways, offshore asset protection, and transaction pattern analysis used in modern financial crime investigations.
10. Jurisdictional Safe-Zone Dynamics
Examines how legal and geographic boundaries can complicate enforcement. Includes differences in international law, extradition delays, fragmented investigative authority, and how remote or privately controlled locations can reduce routine law enforcement visibility.
11. Media Framing & Public Perception Cycles
Studies how media ecosystems shape public understanding of elite crime allegations. Includes sensational framing risk, narrative suppression claims, algorithm amplification, and how public trust in institutions influences belief formation around high-profile cases.
12. Intelligence / Kompromat Risk Models (Evidence-Based Framing)
Examines historically documented use of leverage and compromise material in intelligence and political influence operations. Focuses on verified Cold War and modern examples of kompromat strategy, not speculative ritual narratives, and how such leverage can intersect with financial or sexual misconduct cases.
Baal, Global Elites & Revelation’s Final Warning.
In 2016 THEY, the elites made 3D printed versions of the gate of Baal/Bell to be displayed world wide in many large wicked cities. I really do think this opened portals to the spiritual world.... after this the world went very very dark, right before the Great Revelation 12 sign that happened on Sept 23, 2017, on the Feast of Trumpets that the book of Revelation prophesied would happen...
WHO THE ELITES WORSHIP - WHO DID EPSTEIN WORK FOR? #epsteinfiles
The Epstein files surely feels like a major distraction made by the elites. They just exposed the ones that are unimportant to them or their heinous cause. Dajjal is the final culmination of these cults. So, we should prepare ourselves for his arrival and deception.
Epstein Might Have EATEN PEOPLE
Disturbing coded messages have emerged from the Epstein files that will shake you to your core.Follow the show for more content on your favorite platforms!LI...
The super model that vanished after exposing everything she saw | The story of Gabriela Rico Jiménez
The story of Gabriela Rico Jiménez is one that’s filled with mystery and wonder and in this video we talk about it.
Trafficked Human Hunting Events
Human Hunting: The Darkest Epstein Files Rumor Explained
Disturbing #Epstein #Trump StorySubscribe to 'Stories With Matt' my new channel where these true crime stories (and more) will be living: @StoriesWithMatt ?...
Man Who Hunted Humans As a Game In Real Life
Who was this horrible man who hunted humans as a game and why did he do it? Lets take a look in the year 2019 at the horrible sport of hunting humans. 🎬 MAK...
Human Hunting?! The SHOCKING Truth About What Rich Elites Did for Fun
Rich People paid money to hunt humans in Sarajevo#news #worldnews #breakingnews #viralvideo #trending #fyp #foryoupage #youtuber #vlog #vlogging #wow #usa #d...
SHOCKING Deathbed Confession: Human Beings Hunted for Sport in Northern Canada
On July 20th, 2024, a disturbing deathbed confession appeared on the ‘Politically Incorrect’ discussion board of the website 4Chan.com describing a chilling ...

SECTION XIV — GHISLAINE MAXWELL – MADAME VS. PROCUREMENT AGENT?
“The most effective control systems attacks and destroys identity, not assets.”
CONVICTED CHILD SEX TRAFFICKER: Role, Facilitator, and Institutional Blind Spots
Ghislaine Maxwell, once a prominent British socialite and longtime associate of Jeffrey Epstein, emerged as a pivotal figure in one of the most notorious sex-trafficking operations of the modern era. From the mid-1990s through the early 2000s, she functioned as Epstein’s confidante, recruiter, and enabler, leveraging her elite connections, charm, and apparent normalcy to draw vulnerable teenage girls into a web of exploitation. Convicted in December 2021 on five federal felony counts—including sex trafficking of a minor, conspiracy to entice minors to travel for illegal sex acts, and transportation of a minor for criminal sexual activity—Maxwell was sentenced to 20 years in federal prison in June 2022. Her trial in the Southern District of New York relied heavily on the harrowing testimonies of four primary accusers (pseudonymously “Jane,” “Kate,” “Carolyn,” and Annie Farmer), who described a pattern of grooming, normalization of sexual abuse, and direct participation by Maxwell in assaults on girls as young as 14.
Maxwell’s role extended far beyond passive facilitation; prosecutors portrayed her as Epstein’s “partner in crime,” responsible for scouting girls from disadvantaged backgrounds, building trust through gifts, promises of opportunity, and mentorship-like attention, then escalating interactions into sexual exploitation. She scheduled “massages” that routinely turned abusive, paid victims to recruit others, and participated in sexualized encounters, all while fostering dependency and silence through intimidation tied to Epstein’s wealth and influence. As of February 2026, Maxwell remains incarcerated at a minimum-security federal prison camp in Bryan, Texas, following a recent transfer. Her appeals have been largely unsuccessful—the Second Circuit affirmed her conviction in 2024, and the Supreme Court declined review—though she has continued seeking relief, including recent high-profile attempts to invoke Fifth Amendment rights during congressional depositions tied to ongoing Epstein file scrutiny, while hinting at cooperation in exchange for clemency.
The Maxwell saga underscores profound institutional blind spots that allowed the abuse to persist for years: delayed federal action despite earlier red flags, the controversial 2008 non-prosecution agreement in Florida that shielded potential co-conspirators, and the elite networks that provided cover. Recent releases under the Epstein Files Transparency Act (totaling nearly 3.5 million pages by January 2026) have included additional materials from her case, such as investigative records and media, but have not yielded major new charges or revelations altering her conviction. Accountability has largely halted at Maxwell herself, leaving survivors’ calls for broader justice amid ongoing debates over redactions, victim privacy, and unprosecuted enablers.
Role, Facilitation, and Institutional Blind Spots
Maxwell’s 2021 conviction in the Southern District of New York for sex trafficking and related offenses reframed her public image from socialite to central facilitator within Jeffrey Epstein’s criminal enterprise. The legal record establishes recruitment, grooming, and coordination roles; broader questions remain about network enablement and institutional failure.
1. The Facilitator, Not the Figurehead
Evidence at trial positioned Maxwell as an operational actor—recruiting and normalizing contact—rather than a symbolic accessory.
2. Recruitment, Grooming & Normalization
Testimony described a pattern: identifying vulnerable minors, building trust, reframing boundaries as mentorship, and gradually escalating abuse.
3. Enforcement Through Trust & Threat
Accounts referenced psychological pressure—loyalty, access, social elevation—alongside implied consequences that discouraged disclosure.
4. Social Engineering of Silence
Isolation, normalization, and reputational intimidation functioned as silence mechanisms, particularly in elite environments.
5. Elite Proximity & Protective Shielding
Maxwell’s access to influential circles amplified perceived legitimacy, complicating victim credibility and external scrutiny.
6. Legal Focus Narrowed to One Actor
Prosecutors secured a conviction against Maxwell; critics argue that the scope did not fully examine all potential participants or beneficiaries.
7. Missing Accountability: Clients & Beneficiaries
While flight logs and contact books identified many associates, presence alone is not proof of criminal conduct—yet the absence of broader charges fuels public skepticism.
8. Why Her Conviction Was Necessary—but Insufficient
The conviction affirmed accountability for a facilitator role; it did not resolve every question about network dynamics.
9. Structural Lesson in Elite Child Sex Trafficking
The case highlights systemic blind spots: prestige bias, institutional risk-aversion, and fragmented oversight can allow exploitation to persist when power and reputation intersect.
Who is Ghislaine Maxwell - the British socialite turned Epstein sex trafficker
She’s the socialite who was a big name in American and British high society for decades, hosting glamorous dinner parties and hanging out powerful people.(Su...
GhislaineMaxwell: From socialite to Epstein accomplice • FRANCE 24 English
Ghislaine Maxwell, the longtime associate of sex offender Jeffrey Epstein, is set to be questioned behind closed doors by the US congress. Born into a life o...
Who Is Ghislaine Maxwell? | Jeffrey Epstein: Filthy Rich | Netflix
On one hand, Ghislaine Maxwell was known as a graceful socialite. On the other, according to her accusers, she was a woman who lurked at the edge of high soc...
Who Is Ghislaine Maxwell | Power, Privilege, and the Woman Behind the Curtain
Ghislaine Maxwell is a British socialite born on December 25, 1961, in Maisons-Laffitte, France, and the youngest child of media tycoon Robert Maxwell. Raise...
Prince Andrew: what next after Ghislaine Maxwell guilty verdict? - BBC News
Prince Andrew is facing more scrutiny of his longstanding friendship with Ghislaine Maxwell following her conviction in New York for sex trafficking on behal...
Notorious: Ghislaine Maxwell l 20/20 l Parts 1 – 5
Notorious: Ghislaine Maxwell l 20/20 l PART 1
Ghislaine Maxwell grows up privileged before meeting Jeffrey Epstein: Part 1The daughter of a billionaire media mogul, she was given jobs in her father’s bus...
Notorious: Ghislaine Maxwell l 20/20 l PART 2
Ghislaine Maxwell’s father implicated in pension fund scandal after his death: Part 2Robert Maxwell died during a yacht trip near the Canary Islands. His son...
Notorious: Ghislaine Maxwell l 20/20 l PART 3
Ghislaine Maxwell meets Jeffrey Epstein after father’s death: Part 3Maxwell met Epstein, a wealthy financier, and they started dating. They were both seen so...
Notorious: Ghislaine Maxwell l 20/20 l PART 4
Annie Farmer allegedly lured to Jeffrey Epstein’s New Mexico ranch: Part 4Farmer publicly identified herself as one of the underage victims in the criminal c...
Notorious: Ghislaine Maxwell l 20/20 l PART 5
2 women allege Ghislaine’s Maxwell lured them to Jeffrey Epstein: Part 5Chauntae Davies and Teresa Helm were training to become masseuses when they claim Max...

10. Maxwell’s Central Role in the Epstein Trafficking Network Ghislaine Maxwell operated as Jeffrey Epstein’s closest collaborator and household overseer for nearly two decades, using her socialite status to lend credibility to the operation. She was convicted as the key architect of recruitment and grooming efforts that targeted underage girls, often from unstable or low-income backgrounds. Her elevated position in elite circles helped normalize access to Epstein’s properties and lifestyle, creating an environment where abuse could flourish under the guise of opportunity and privilege.
11. Methods of Recruitment and Grooming: Building Trust and Normalizing Abuse Recruitment typically involved approaching girls with offers of money for “massages,” shopping sprees, travel, or educational support, positioning Maxwell as a caring mentor. She discussed personal matters to build rapport, then introduced sexual topics casually, undressing in front of victims or encouraging group settings to desensitize them. This gradual erosion of boundaries made escalation to abuse feel routine, while payments and promises fostered indebtedness and reduced the likelihood of disclosure.
12. Direct Participation in Sexual Abuse Victim testimonies established that Maxwell not only facilitated but actively joined in sexual encounters, including touching victims’ bodies, participating in group acts, and praising their appearances to benefit Epstein. In specific incidents, she fondled or massaged minors, was present during Epstein’s assaults, and directed behaviors in locations like Palm Beach, New York, and New Mexico. Prosecutors highlighted her hands-on involvement as evidence of conspiracy beyond mere enabling.
13. Types of Abuse Endured by Victims and Survivors Victims described repeated sexualized “massages” that progressed to molestation, groping, masturbation by Epstein on them, and forced penetration or group encounters. Psychological abuse included manipulation through gifts, threats of reputational harm, and normalization of exploitation as “what powerful people do.” Long-term effects reported by survivors encompass severe trauma, eroded self-worth, substance issues, dissociation, and persistent fear of authority figures.
14. Enforcement, Control, and Long-Term Impacts: Destroying Identity Through Silence and Dependency Maxwell enforced compliance by leveraging status differences, creating emotional/financial reliance, and instilling shame or guilt to prevent reporting. The system deliberately attacked victims’ sense of self, isolating them from support and fostering internalized blame. This identity destruction—prioritizing psychological domination—ensured prolonged silence, with many survivors only coming forward years later amid broader revelations.
15. Accountability Gaps: Why Justice Largely Stopped with Maxwell’s Conviction Despite her 20-year sentence, no major additional prosecutions of alleged co-conspirators have followed, partly due to prior agreements, investigative delays, and protections for high-profile associates. Recent 2026 file releases have sparked renewed scrutiny and congressional inquiries, but redactions for victim privacy and lack of corroborated new evidence have limited breakthroughs. Maxwell’s case exemplifies how institutional failures and elite influence can confine accountability to a single figure, leaving systemic enablers largely untouched.
Ghislaine Maxwell’s Testimony Comes with Strings Attached
Federal criminal defense attorney Ronald Chapman analyzes the legal and political implications of Ghislaine Maxwell’s conditional offer to testify before Con...
WATCH: Ghislaine Maxwell refused to answer questions about Epstein in House deposition, Comer says
Watch PBS News for daily, breaking and live news, plus special coverage. We are home to PBS News Hour, ranked the most credible and objective TV news show.Si...
All the New Details We Learned About Ghislaine Maxwell From the Epstein Files
MK True Crime hosts Phil Holloway and Ashleigh Merchant are joined by retired FBI agent Jennifer Coffindaffer to discuss what the latest Epstein files tranch...
SECTION XV — EPSTEIN VICTIMS, SURVIVORS, AND PLAINTIFFS
“The most effective control systems attacks and destroys identity, not assets.”
Testimony, Legal Proceedings & Systemic Accountability
The victims and survivors of Jeffrey Epstein’s sex-trafficking network represent a diverse group of young women, many groomed as teenagers from vulnerable backgrounds, who endured years of sexual abuse facilitated by Epstein and Ghislaine Maxwell. Their stories, revealed through court testimonies, civil lawsuits, and public statements, highlight patterns of recruitment via promises of opportunity, financial support, or mentorship, followed by escalating sexual exploitation across Epstein’s properties in Palm Beach, New York, New Mexico, and elsewhere. Key figures emerged prominently during Maxwell’s 2021 federal trial, where four women provided detailed accounts that formed the core of the prosecution’s case, leading to her conviction on five felony counts related to minor sex trafficking and conspiracy.
Beyond the trial, numerous survivors pursued civil litigation against Epstein’s estate and associates, resulting in settlements from a victims’ compensation fund and individual claims. Prominent accusers like Virginia Roberts Giuffre filed high-profile suits alleging trafficking to powerful figures, including Prince Andrew (settled in 2022), while others, such as Annie Farmer, have advocated publicly for transparency and reform. Tragically, some survivors faced ongoing trauma, with reports of overdoses and suicides (including Carolyn Andriano in 2023 and Virginia Roberts Giuffre in 2025), underscoring the long-term devastation. As of February 2026, recent Epstein file releases under the Transparency Act have renewed attention, with survivors demanding fuller accountability despite redactions and privacy concerns.
These women’s courage in coming forward—often after decades of silence—has driven partial justice, including Maxwell’s 20-year sentence, but broader institutional failures persist: delayed investigations, protective agreements for enablers, and incomplete prosecutions. Survivors continue organizing, including compiling unofficial associate lists and testifying in congressional hearings, to ensure their experiences reshape accountability for elite exploitation networks.
Testimony, Legal Proceedings & Systemic Accountability
The legal aftermath of Jeffrey Epstein’s crimes centers on survivor testimony, federal prosecution, and the broader question of institutional accountability. Court proceedings and civil litigation brought forward detailed accounts that reshaped public understanding of how trafficking networks operate within elite environments. The focus now extends beyond individual wrongdoing toward systemic failures that allowed abuse to persist.
1. Documented Victim Testimonies
Federal indictments and sworn statements described patterns of recruitment, grooming, coercion, and repeated abuse. These testimonies formed the evidentiary backbone of criminal charges and civil claims.
2. Civil Lawsuits & Plaintiff Classifications
Numerous survivors filed civil suits against Epstein’s estate and associated parties. Plaintiffs were categorized through individual suits, class actions, and participation in compensation programs.
3. Criminal Charges & Federal Prosecution
Epstein faced federal sex trafficking charges in 2019 before his death in custody. Ghislaine Maxwell was later convicted in federal court for sex trafficking and related offenses tied to the network.
4. Financial Settlements & Compensation Funds
Epstein’s estate established a victim compensation program, distributing millions of dollars to approved claimants. Settlements provided financial redress but did not substitute for full criminal accountability.
5. Institutional Failures
Investigations revealed breakdowns in oversight across law enforcement, financial institutions, and academic environments. The controversial 2008 non-prosecution agreement in Florida remains a focal point of criticism.
6. Survivor Advocacy & Trauma Recovery
Advocates and legal representatives amplified survivor voices, shifting public discourse from scandal to systemic reform. Long-term trauma recovery remains an ongoing process for many victims.
7. Sealed Records & Ongoing Litigation
Court-ordered redactions and sealed filings continue to limit full public visibility. Civil litigation related to associated parties remains active in various jurisdictions.
8. Public Figures Named vs. Charged
Names appearing in flight logs or court documents do not automatically indicate criminal conduct. Distinguishing between documented association, allegation, and formal charges is essential for maintaining legal and evidentiary clarity.
Epstein Victim Describes What Really Happened Behind Closed Doors
The video discusses the Jeffrey Epstein case, focusing on the types of men involved in the trafficking (0:04), Epstein's motivations (0:56), and the disturbi...
The Epstein survivors speak out: Linsey Davis reports
Women who say they are survivors of Epstein's sexual abuse and trafficking sit down with Linsey Davis for a powerful interview including one woman who is pub...
Nobody's Girl: 10 Devastating Reveals from Virginia Giuffre's Posthumous Memoir
Virginia Roberts Giuffre’s posthumous memoir uncovers stunning and heartbreaking truths about her harrowing experiences. From her dark beginnings and exploit...
Jeffrey Epstein Accuser Shares Story Of Alleged Rape For 1st Time | TODAY
In a TODAY exclusive, Jennifer Araoz shares with Savannah Guthrie her chilling account of alleged sexual assault by billionaire Jeffrey Epstein, which she sa...
"Childhood Size Genitalia" | Epstein Survivor Rina On "Harem", Baby Farms & Ghislaine...
Mario Nawfal is the host of the largest show on X (formerly Twitter) with guests including Hunter Biden, Elon Musk, President Bolsonaro, President Novak, PM Imran Khan, RFK Jr, Bill Ackman, Marc Cuban, Marc Andreessen and Tucker Carlson reaching millions of people a week and leading the citizen journalism movement.
ESCAPE FROM HELL: How I Left Epstein's Island And Why They're Still Trying To Silence Me
I was 17 years old when a woman in a Chanel suit approached me after a casting call and promised me the modeling career of my dreams. What followed was a nig...
They Filmed Me Begging To Stop | 4 Nights On Epstein's Island That Broke Me
This shocking and emotional story dives deep into the dark reality behind the headline: “They Filmed Me Begging To Stop – 4 Nights On Epstein’s Island That B...
From School to EPSTEIN ISLAND: The KIDNAPPING Story That Wasn't BELIEVED
This is my true story of kidnapping and survival on Epstein Island. I was 12 years old, walking home from school – just four blocks that I had walked a thous...
I SURVIVED EPSTEIN ISLAND — THE TRUTH THAT WAS HIDDEN
I was 17 years old when I accepted what seemed like a dream opportunity — $20,000 for seven days of resort work on a private Caribbean island. I was an orpha...
"THEY EXPERIMENTED ON ME": The Testimonies Of Juliette & Beatrice | EXPOSING Epstein Files Deep Dive
Today's episode of the show is incredibly special. In this episode, I interview 2 Epstein survivors who shared with me their harrowing stories of survival, a...
Epstein Files: Youngest Survivor Demands Justice, Lambasts Redactions, & Orders Accountability
Epstein Files: Youngest Survivor Demands Justice, Lambasts Redactions, & Orders Accountability The recent release of Epstein files by the US Department of Ju...
Survivors and families speak out after release of Epstein files
Some survivors of the abuse by Jeffrey Epstein, and the survivors’ families, are speaking out after the Justice Department released the Epstein files. NBC Ne...
Jeffrey Epstein survivor breaks silence, detailing years of abuse starting at 14
Marina Lacerda, one of the key people responsible for putting Jeffrey Epstein behind bars, is stepping forward to tell her story, hoping it will inspire othe...
Epstein survivors call for release of remaining files | BBC News
Survivors of convicted sex offender Jeffrey Epstein appear in a new video calling for more files relating to the criminal investigation into the late financi...
Karen Mulder - the Original EPSTElN Whistle Blower Who Was Silenced
Karen Mulder - the original EPSTElN whistle blower who was silencedTo support this channel:Cashapp: $karinealourdePayPal: @karinealourde https://www.instagra...
The Suspicious Death of Ruslana Korshunova; The Young Model Who Visited Epstein's Island as a Teen
Also… I can’t verify it (yet)… but the last boyfriend of Ruslana, Mark Kaminsky is nagging at my brain.Why? Mark I. Kamisky (1932-2007) was an infamous US sp...
Epstein Files: Victim Video Interviews (Public Record, No Commentary) - Part 1
In this episode of the Epstein Files, I am presenting video interviews with victims as they appear in publicly released case materials.These interviews are s...

PHOTO ESSAY: Epstein Survivors Confront Congress, Demand Transparency
Survivors of Jeffrey Epstein and Ghislaine Maxwell united in Washington, D.C., demanding truth, accountability and release of federal files.
Key Victims, Survivors, and Legal Plaintiffs The following section lists prominent individuals who have publicly shared accounts as victims or survivors, testified in court, or pursued legal action. Many used pseudonyms for privacy during proceedings.
1.1 “Jane” (Pseudonym, Minor Victim-1) “Jane” testified she met Epstein and Maxwell at age 14 in 1994 at a Michigan arts camp where Epstein was a benefactor. She described frequent abuse over years, including group sexual encounters where Maxwell participated, normalizing exploitation through grooming and participation. Her emotional testimony highlighted the destruction of her sense of safety and identity.
1.2 “Kate” (Pseudonym, Witness-3) “Kate” met Maxwell in London at age 17 around 1994, introduced through an older boyfriend, and was encouraged to give Epstein sexualized massages that escalated to abuse. She recounted Maxwell scheduling encounters and fostering dependency over several years. Though over the age of consent in the UK for some acts, her account illustrated grooming tactics across borders.
1.3 “Carolyn” (First Name Used, Minor Victim-4) Carolyn began abuse at age 14 in Palm Beach, recruited via a friend, giving frequent “massages” to Epstein that involved sexual acts, scheduled by Maxwell who groped her and praised her body. She recruited others under pressure and testified tearfully about years of exploitation tied to financial hardship. Tragically, Carolyn died of an accidental overdose in 2023 at age 36.
1.4 Annie Farmer (Full Name Used) Annie Farmer, abused at age 16 in 1996, met Epstein and Maxwell through her sister; Maxwell gave her a nude massage at Epstein’s New Mexico ranch, groping her breasts under the guise of relaxation. As the only trial witness using her real name, she has since become a vocal advocate for survivors. Farmer has spoken publicly about long-term trauma and the need for systemic change.
1.5 Virginia Roberts Giuffre Virginia Roberts Giuffre alleged recruitment at age 17 while working at Mar-a-Lago, claiming trafficking by Epstein and Maxwell to high-profile individuals including Prince Andrew (settled civilly in 2022). She filed key lawsuits and spoke publicly for years. Giuffre died by suicide in Australia in 2025 at age 41, with her family continuing advocacy efforts.
1.6 Other Notable Survivors and Plaintiffs Additional survivors include Maria Farmer (who reported abuse in 1996 involving her family), Jennifer Araoz (abused as a teen in New York), and others like Marina Lacerda (who spoke publicly in 2025 about abuse from ages 14-17). Many joined civil suits or the Epstein Victims’ Compensation Program for settlements. Recent 2025-2026 advocacy, including Capitol Hill testimonies, has focused on unredacted files and broader justice demands.
This structure maintains sensitivity, focusing on substantiated trial and public accounts while emphasizing resilience and ongoing pursuit of justice. If you’d like expansions, adjustments for tone, or additions based on specific aspects (e.g., more on civil cases), let me know!
Babies & Children Abuse Victims
BOMBSHELL: Epstein Disturbing ‘Baby Emails’ Explained by Nick Bryant
Katie talks to journalist and author Nick Bryant, who first published Epstein's black book and is himself mentioned in the Epstein files as someone who Jeffr...
Child Abuse Code Language
INTERVIEW: The Epstein code
A decade ago investigator Ben Swann was slammed for claiming that many of the words used by Jeffrey Epstein were also code words used by pa*dophiles. Vindica...
SECTION XVI — THE MASTERMIND DOWNFALL OF WESTERN CIVILIZATION
“Power prefers foresight to confrontation.”
Where Global Control Meets Diabolical Intent
This section examines how advanced research domains—public health modeling, artificial intelligence, behavioral science, data analytics, and frontier physics—can converge into powerful systems of prediction and influence. When knowledge enhances the ability to forecast crises, shape decision-making, or optimize populations at scale, it naturally draws the attention of state actors, private power centers, and security institutions. The shift is rarely dramatic or openly declared; it emerges gradually through funding priorities, advisory roles, and cross-sector collaboration.
The dynamic is not necessarily driven by overt malice, but by structural incentives. Pandemic modeling, AI governance systems, behavioral economics, predictive policing tools, and advanced energy research all carry dual-use potential. Insights designed for public benefit—disease mitigation, efficiency, safety, sustainability—can also strengthen surveillance architectures, strategic planning systems, or demographic policy tools. The same algorithms that prevent fraud can assess ideological risk; the same bioscience that improves health outcomes can inform population-level management strategies.
The structural tension lies in visibility and accountability. National security relevance often appears without labels, contracts, or uniforms—embedded instead in data partnerships, research grants, or policy integration. As oversight frameworks lag innovation, the boundary between civilian research and strategic application becomes increasingly porous. The result is not dramatic conspiracy, but normalized convergence—where technological capacity expands faster than public debate, and foresight quietly becomes leverage.
Where Global Control Meets Diabolical Intent
1. Pandemic Modeling & Bio-Systems Research
Pandemic modeling and bio-systems research sit at the intersection of health, logistics, and governance. Models that forecast spread, resource allocation, and behavioral response can save lives—but they also inform control levers: mobility restrictions, supply prioritization, and emergency powers. Because models are probabilistic, their assumptions carry policy weight. Early access to these assumptions confers influence over response design long before public debate begins.
2. Artificial Intelligence & Predictive Governance
AI’s earliest value proposition was prediction: pattern recognition, anomaly detection, and optimization under uncertainty. When applied to governance, these tools shape anticipatory decision-making—allocating attention, resources, and enforcement before events occur. The strategic appeal lies not in automation, but in forecasting leverage. As models improve, they quietly recalibrate what policymakers consider “necessary,” often without transparent audit.
3. Human Behavior Modeling & Decision Theory
Behavioral modeling translates psychology into math: incentives, biases, thresholds, and cascades. Decision theory formalizes choice under uncertainty. Together, they enable simulations of compliance, panic, persuasion, and fatigue. In civilian contexts, this improves design and communication. In strategic contexts, it informs influence operations—how narratives spread, when resistance breaks, and which interventions minimize backlash.
4. Human Data Collection, Patterns, & Pre-crime
Human data collection has expanded dramatically in the digital era, with governments and corporations gathering behavioral, financial, biometric, and location-based information at scale. Advanced analytics and AI systems use this data to detect patterns, predict trends, and assess potential risks. While these tools can enhance security, fraud detection, and public safety, they also introduce concerns about privacy, bias, and due process.
The concept of “pre-crime” emerges when predictive models attempt to intervene before wrongdoing occurs—raising ethical questions about punishing probabilities rather than proven actions. The core challenge is balancing technological capability with legal safeguards that protect civil liberties.
5. Energy, Materials & Exotic Physics
Advances in energy systems, materials science, and exotic physics redefine constraints. New materials alter sensing, shielding, and mobility; energy breakthroughs shift logistics and autonomy. These domains mature quietly and reveal impact late, making them attractive to strategic actors who value long lead times and surprise. Dual-use here is inherent: the same discovery that lowers costs or improves efficiency can transform defense posture.
6. Why National Security Appears Without Labels
National security rarely announces itself at the research stage. Labels invite scrutiny, compliance burdens, and political friction. Proximity avoids all three. Advisory roles, informal briefings, and funding interest allow security stakeholders to track progress without ownership. By the time labels appear—if they do at all—the science is already embedded in systems, standards, or policy assumptions.
7. Eugenics & Population Control
Eugenics emerged in the late 19th and early 20th centuries as a movement claiming that human populations could be “improved” through selective breeding and reproductive control. It gained traction in parts of the United States and Europe, influencing forced sterilization laws and, most infamously, the racial policies of Nazi Germany. After World War II, the term became widely discredited due to its association with coercion, racism, and human rights abuses.
Modern discussions about population control tend to focus instead on public health, family planning, and demographic sustainability, though ethical concerns remain whenever reproductive autonomy intersects with state or institutional power.
8. Cryonics & Transhumanism
Cryonics and transhumanism are linked by a shared premise: human biological limits are not final. Cryonics focuses on preserving legally deceased individuals at ultra-low temperatures, typically through vitrification, in the hope that future medical advances may repair cellular damage and restore life. Organizations such as Alcor Life Extension Foundation and Cryonics Institute operate on the belief that identity is embedded in brain structure and that preserving that structure preserves the possibility of future revival. Transhumanism expands that horizon further, advocating the use of emerging technologies—genetic engineering, artificial intelligence, nanotechnology, and brain-computer interfaces—to enhance cognition, extend lifespan, and potentially redesign aspects of human biology itself.
Together, these movements represent a philosophical shift from accepting mortality as inevitable to treating it as a technical challenge. Influential futurists such as Ray Kurzweil argue that accelerating technological growth may radically transform what it means to be human within this century. Supporters view this trajectory as the next stage of evolution—intentional, engineered, and expansive. Critics question feasibility, ethics, inequality, and the preservation of human identity. At their core, both cryonics and transhumanism force a defining question: are we meant to adapt within nature’s constraints, or are we entering an era where we attempt to rewrite them?
How Does Cryonics Fit Into Transhumanism? - Philosophy Beyond
How Does Cryonics Fit Into Transhumanism? In this thought-provoking video, we will explore the fascinating relationship between cryonics and transhumanism. D...
Epstein: A Forensic Reconstruction of the Transhumanist Research Network Concealed by Scandal
Epstein: A Forensic Reconstruction of the Transhumanist Research Network Concealed by ScandalBlogger:
Frozen Legacy – Epstein’s Dark Obsession with Cryogenics
Here's a 10-point summary of the YouTube video transcript about Jeffrey Epstein's obsession with cryogenics and immortality:• **Cryogenic Preservation Plan**...
Jeffrey Epstein's Demonic Transhumanist Fantasy
#Logos #Epstein #Christianity This video is a clip from my stream "Drama Alert: Epstein Files, Trump, Pam Bondi, Steve Bannon, and MORE!" If you would like ...
Epstein’s Secret Science: Plan to Create Genetically Superior Humans | WION
Epstein’s Secret Science: Jeffrey Epstein reportedly planned to create a "genetically superior" human race using advanced genetic engineering and artificial ...
Major Epstein Twist: The Super Human Race Plan Gets Exposed | WION
Jeffrey Epstein, the convicted sex offender, reportedly aimed to create a “super-race” of humans by using his own DNA, according to a New York Times investig...
Cold Harbor: Eugenics, Epstein and Big Tech
In the recent cache of Jeffrey Epstein emails unveiled by Bloomberg, Epstein’s connections to the elites of academia illuminate his interest in transhumanism, or neo-eugenics — a philosophy that has become commonplace among Big Tech oligarchs and ruling class elites.
Epstein emailed with Silicon Valley elites about racist, eugenicist ideas
Recently released emails show Epstein discussed the appeal of fascism and population control through climate change with AI theorists who have ties to prominent tech billionaires.
What Is Transhumanism and Why Do People Associate It With Eugenics?
A primer on the philosophy, popularized by Jeffrey Epstein, which encompasses immortal cyborgs, baby ranches and parenting licenses.
The billionaires' eugenics project: how Epstein infiltrated Harvard, muzzled the humanities and preached master-race science
Edge - Jeffrey Epstein's favourite intellectual salon - was sold to me as a gathering of the world's finest minds, writes Virginia Heffernan. The files reveal it was something far darker: a decades-long project that cloaked eugenics, race science and sexual misconduct in Ivy League respectability
Epstein’s Plan to Impregnate 20 Women at Once
20 Women at a Time? Epstein’s Plan to Freeze Himself After Death #Epstein #eugenics #cryonics
20 Women at a Time? Epstein’s Plan to Freeze Himself After DeathSome billionaires want power.Some want influence.But what happens when someone dreams of cont...
Epstein IMPREGNATED 20 Women at Once? DIRTY Superhuman Race Secret EXPOSED! What Was Epstein's Plan?
Jeffrey Epstein allegedly planned to create a ‘superhuman race,’ reportedly aiming for 20 women to be pregnant simultaneously at his New Mexico ranch. His co...
Revealed: Epstein had secret BABY with TEEN girl who felt like a 'human incubator'
Jeffrey Epstein may have had multiple secret children, including one with a teenage girl who claims she felt like a “human incubator”.Bombshell files related...
SECTION XVII — ARCHITECTURE & ENGINEERING of FINANCIAL CORRUPTION
“Capital does not command discovery—it conditions and manipulates it.”
Funding Science, Steering Outcomes
This section returns to the financial backbone that quietly connects earlier sections: the architecture of money that enables influence without overt control. The Epstein files reinforce a broader reality—science does not move on curiosity alone. It moves on funding structures, incentives, and risk management. When capital is structured to flow around oversight rather than through it, outcomes can be shaped without issuing directives. This is not corruption in the crude sense; it is financial design.
What makes this architecture effective is subtlety. Funds are rarely tied to explicit demands. Instead, they reward certain research questions, accelerate specific pathways, and deprioritize others. Over time, entire fields drift toward what is fundable, not necessarily what is most transparent, ethical, or socially beneficial. In this context, figures like Jeffrey Epstein matter less as individuals and more as examples of how capital can be positioned upstream of discovery.
Section XII clarifies that financial influence does not require secrecy—only complexity. Layered entities, charitable vehicles, and emergency frameworks diffuse accountability while preserving directional control. When crises emerge, these structures are already in place, ready to activate.
Funding Science, Steering Outcomes
1. Donor-Advised Funds & Research Influence
Donor-advised funds (DAFs) allow contributors to receive immediate tax benefits while retaining long-term influence over how capital is deployed. In research contexts, DAFs can route money into universities, labs, and initiatives with minimal public disclosure. This creates a soft form of influence: projects aligned with donor priorities flourish, while others struggle—without any explicit interference.
2. Philanthropy as Risk Shield
Philanthropy functions as reputational armor. Funding framed as charitable reduces scrutiny, discourages skepticism, and reframes influence as benevolence. When controversial outcomes arise, philanthropic intent provides plausible deniability. The risk is not that philanthropy exists, but that it absorbs accountability that would otherwise apply to commercial or governmental actors.
3. Financial Incentives Embedded in Discovery
Incentives shape discovery. Equity stakes, licensing agreements, milestone payments, and downstream royalties embed financial outcomes directly into the research process. These incentives can accelerate innovation—but they also bias inquiry toward monetizable results. Over time, scientific agendas align with return profiles rather than public need.
4. Crisis Monetization & Preparedness Markets
Preparedness has become a market. Pandemic readiness, climate resilience, cybersecurity, and biosecurity now attract standing capital, insurance products, and forward contracts. When crises occur, funds deploy automatically. This creates a structural tension: systems designed to mitigate risk may also benefit from its persistence, incentivizing readiness over resolution.
5. When Science Serves Capital First
The final risk emerges when science becomes a service layer for capital rather than a public good. When funding, career advancement, and institutional survival depend on financial alignment, dissent narrows and alternative pathways disappear. This does not require bad actors—only systems that reward compliance and speed over reflection and transparency.
6. Global Money Laundering & Hiding $$$ Schemes
Global money laundering typically involves layering financial transactions across jurisdictions to obscure the origin of funds. Common mechanisms include shell companies, offshore accounts, nominee directors, complex trust structures, trade-based laundering, cryptocurrency mixers, and cross-border transfers routed through secrecy havens. The objective is to separate illicit proceeds from their source, integrate them into legitimate financial systems, and reduce traceability. Enforcement agencies rely on anti–money laundering (AML) regulations, suspicious activity reports, and international cooperation to detect these patterns—but fragmented oversight and regulatory arbitrage remain persistent challenges.
7. 501(c)(3) Foundations Used as Front Operations
In rare but documented cases, nonprofit entities organized under U.S. 501(c)(3) status have been misused to disguise financial flows, inflate charitable deductions, or route funds for improper purposes. Because nonprofits can receive tax-deductible donations and often operate across borders, they may be vulnerable to exploitation if governance, transparency, and board oversight are weak. However, the vast majority of registered charities operate lawfully and provide legitimate public benefit. The key risk factors involve poor internal controls, related-party transactions, lack of independent auditing, and insufficient regulatory scrutiny.
BREAKING: The Epstein Files Illuminate a 20-Year Architecture Behind Pandemics as a Business Model
Inside the JPMorgan-Gates-Epstein Pipeline: Donor-Advised Funds, Vaccine Finance, and the Architecture of Pre-Positioned Profit
Jeffrey Epstein’s Former Business Associate: I Want To Assist Victims
Steven Hoffenberg spent 18 years in prison for running a Ponzi scheme. He says his former business partner Jeffrey Epstein should have been there too.
The Epstein files reveal that a vast global conspiracy actually exists – sort of
The documents confirm what many have long assumed: elites live by their own special rules and codes of immunity
The Clinton Foundation’s Epstein Problem
🔗 Learn more about Ron Chapman’s work:— Visit the official website: https://ronaldwchapman.com/— Grab a copy of Truth and Persuasion in a Digital Revolution...
Time Is Up for Hillary Clinton
Time Is Up for Hillary Clinton.What began as a financial scandal tied to Jeffrey Epstein has unraveled into a far-reaching investigation into the Clinton Fou...
Newly Unsealed Documents Reveal How Jeffrey Epstein Amassed $580M Fortune - National Today
Newly released federal documents have shed fresh light on how convicted sex offender Jeffrey Epstein amassed a $580 million fortune that powered his criminal empire and attracted the attention of the ultra-wealthy. The documents reveal details about Epstein's opaque financial entities, including a '1953 Trust' that concealed the identities of over 40 beneficiaries, and his relationships with high-profile clients like Les Wexner and Leon Black who funneled hundreds of millions of dollars to Epstein.
SECTION XVIII — MSM Censorship, ACADEMIC PROTECTION & SHIELDS
“What cannot be framed simply is often ignored deliberately.”
Why This Thread Rarely Makes Headlines
This section examines why the most consequential threads in the Epstein files—science funding, elite academic pipelines, and systems-level influence—receive the least sustained media attention. The absence is not accidental, nor does it require coordinated censorship. It emerges from overlapping incentives within media and academia that discourage scrutiny of complex, credential-heavy domains. Scandal is easy to report; systems are not. When stories demand technical literacy, long timelines, and cross-domain synthesis, they exceed the risk tolerance of most outlets.
At the academic level, protection is often passive rather than conspiratorial. Universities, journals, and professional societies are optimized to preserve credibility, funding, and donor relationships. When allegations or uncomfortable questions threaten those pillars, institutions default to containment—narrowing scope, emphasizing uncertainty, and discouraging inquiry that could implicate respected fields or figures. This section explains how silence can be produced without orders, simply by aligning incentives toward caution.
The result is a feedback loop: media avoids complexity; academia avoids controversy; and the public receives fragmented narratives that isolate misconduct from the systems that enable it. Section XIII shows how this loop sustains itself—and why breaking it requires structural, not individual, change.
Why This Thread Rarely Makes Headlines
Stories that involve frontier science, financial instruments, and academic governance lack clear villains and simple timelines. They require sustained investigation and technical translation, which are costly and risky. As a result, coverage gravitates toward episodic revelations rather than systemic analysis—leaving deeper threads underreported.
1. The “Too Smart to Question” Bias
Elite credentials create deference. When subjects are Nobel laureates, Ivy League professors, or prominent researchers, skepticism is socially discouraged. Questioning them risks being framed as anti-science or ignorant. This bias elevates authority over accountability and shields entire domains from scrutiny.
2. Credential Protection & Career Risk
Academia is reputation-driven. Careers depend on grants, citations, peer approval, and institutional standing. Speaking publicly about sensitive funding sources or ethical gray zones can jeopardize tenure, visas, collaborations, and future funding. The rational response for many is silence—or strict adherence to officially sanctioned narratives.
3. Why Journalists Avoid Scientific Complexity
Modern newsrooms are under-resourced and deadline-driven. Investigating complex science-finance intersections requires expertise many outlets no longer maintain. Editors often favor stories that can be verified quickly and explained simply. When complexity rises, interest falls—especially if legal exposure increases.
4. Narrative Containment Strategies
Containment does not mean suppression. It means framing: limiting stories to narrow facts, emphasizing uncertainty, and avoiding connective analysis. By keeping topics siloed—crime here, science there, finance elsewhere—institutions prevent pattern recognition without denying any single fact.
5. Manufactured Disinterest
When stories are consistently framed as niche, speculative, or too technical, public interest erodes. Over time, audiences internalize the signal that “this doesn’t matter” or “it’s unknowable.” Disinterest becomes manufactured not by force, but by repetition and omission.
6. Censorship of True Facts & False Stories
Jeffrey Epstein received significant mainstream media coverage, particularly after his 2019 arrest and death. However, critics argue that certain elements—such as elite associations and institutional failures—were framed cautiously or explored unevenly due to legal risk and editorial standards.
At the same time, unverified claims spread widely online, creating parallel narratives that complicated public understanding. The tension is less about total censorship and more about selective emphasis, liability concerns, and the challenge of separating proven facts from speculation in high-profile cases.
Epstein’s Israel links and everything else ignored by mainstream media | The Listening Post
The Epstein files dump has led to days of intense media coverage, revealing how powerful elites around the world engaged in either illegal or morally reprehe...
The Epstein Files and the Art of Drowning the Truth
The mass release of millions of files related to Jeffrey Epstein serves as a metaphor for a wider crisis of the digital age: an overabundance of information that obscures rather than illuminates the truth. In an era where data floods replace traditional censorship, citizens risk becoming less informed, underscoring the vital role of professional journalism in filtering noise into meaningful knowledge.
Epstein files scrubbed to protect 'elite, powerful men,' Rep. Ro Khanna says
Explore how some lawmakers are seeking justice for the survivors included in the Epstein files
Why The Media Won’t Cover The Epstein Files
A former TV news producer reveals why mainstream media won’t touch the latest Epstein files report.
Jeffrey Epstein: how US media – with one star exception – whitewashed the story
The Miami Herald exposed a vast criminal network and a government cover-up – but why the silence elsewhere?
What the Epstein Files Media Discourse Misses About How Power Operates
Media discourse on the Epstein files prioritizes salacious, sidelining survivors and the structure that enables this abuse.
SECTION XIX — LAWFARE & INSTITUTIONAL FIREWALLS
“Institutions protect continuity and status quo before truth.”
Why No One Wants Discovery or Exposure
This section explains why, despite extensive documentation and repeated civil actions, the Epstein ecosystem rarely reached full judicial discovery. The barrier was not a lack of allegations or evidence—it was risk concentration. Discovery threatens to expose funding flows, internal communications, donor relationships, institutional decision-making, and prior knowledge across multiple sectors simultaneously. For large institutions, discovery is not a legal phase; it is an existential event.
The Epstein files reveal a pattern in which legal exposure was managed, not resolved. Civil suits were steered toward settlement, criminal cases were narrowed in scope, and jurisdictional fragmentation prevented unified prosecution. This did not require overt collusion. Each institution—universities, banks, nonprofits, foundations, and government bodies—acted rationally to minimize its own risk. The cumulative effect was a system that absorbed shock without yielding transparency.
Section IX reframes “firewalls” as structural features of modern power. Legal insulation, contractual silence, and procedural delay are not anomalies; they are designed outcomes. This section clarifies how accountability is deflected not by denying facts, but by preventing those facts from ever being fully assembled in court.
Why No One Wants Discovery or Exposure
In high-stakes litigation involving powerful institutions, the legal system can become both a shield and a battleground. “Lawfare” refers to the strategic use of legal processes—motions, jurisdictional challenges, delays, sealed filings, and procedural barriers—to contain risk, manage exposure, or avoid broad discovery. Institutions often prioritize reputational containment and financial predictability over prolonged public litigation.
1. Weaponization of the Legal System
Complex procedural tactics, aggressive motions to dismiss, and venue strategies can narrow cases before discovery reaches sensitive internal communications.
2. Limited Liability Exposure in Scientific Funding
Universities and research institutions often structure grants and donor agreements to limit institutional liability, separating academic research from donor misconduct.
3. Civil Settlements & NDA Culture
Confidential settlements and non-disclosure agreements reduce public scrutiny but can prevent systemic issues from surfacing in open court.
4. Why Universities Avoid Court
Extended litigation risks reputational damage, donor flight, accreditation scrutiny, and exposure of internal compliance failures—creating incentives to settle quietly.
5. The Risk of Precedent
A single adverse ruling can establish legal precedent, expanding future liability across sectors, which makes institutions cautious about allowing broad discovery.
6. Structural Immunity
Sovereign immunity doctrines, statutory protections, insurance layers, and institutional governance structures often insulate large entities from full accountability, limiting how far litigation can penetrate systemic networks.
7. Why No One Wants Discovery
7Discovery compels disclosure under oath. Emails, donor records, internal deliberations, and third-party communications become subject to scrutiny. For institutions intertwined with elite finance, science, and philanthropy, discovery threatens to reveal not just wrongdoing, but systemic governance failure. Avoidance becomes the priority.
8. Liability Exposure in Scientific Funding
Scientific funding creates shared liability. When donors influence research direction, ethics oversight, or institutional decision-making, legal responsibility can extend beyond individuals to departments and boards. Institutions therefore limit inquiry into funding origins to avoid retroactive exposure.
9. Civil Settlements & NDA Culture
Civil settlements offer closure without clarity. Non-disclosure agreements silence victims, witnesses, and sometimes entire institutions. While legal, this culture converts justice into a financial transaction—resolving cases privately while preserving public ignorance and institutional reputation.
10. Why Universities Avoid Court
Universities are uniquely vulnerable in court. Discovery could expose donor vetting failures, ethics lapses, and internal conflicts of interest. Litigation also threatens accreditation, public funding, and alumni trust. As a result, universities prioritize containment over confrontation, even when allegations are serious.
11. The Risk of Precedent
Precedent is more dangerous than penalties. A single adverse ruling can establish obligations that ripple across sectors—forcing transparency in funding, governance, and ethics. Institutions therefore settle early to prevent legal standards that others could invoke later.
12. Structural Immunity
Structural immunity emerges when legal, financial, and reputational defenses overlap. No single action grants immunity; it is produced by layers—jurisdictional complexity, arbitration clauses, NDAs, settlements, and time. Together, they form a firewall that protects systems even as individuals fall.
The curious case of ‘missing’ Epstein files
The US Department of Justice will not release the remaining files, which could contain more serious allegations against rich and powerful men, as the hope for justice for Jeffrey Epstein victims fades
DoJ accused of cover-up after lawmakers view unredacted Epstein files | First Thing
Jamie Raskin, House judiciary ranking member, says ‘mysterious redactions’ obscure abusers’ names. Plus, RFK Jr accused of misleading Senate
US lawmakers accuse justice department of 'inappropriately' redacting Epstein files
Republican Thomas Massie and Democrat Ro Khanna say the DOJ is not complying with their transparency law.
New Epstein files fail to quell outrage as advocates claim documents are being withheld
Advocates call for further disclosures after Trump’s justice department released more than 3m files last week
Jamie Raskin accuses DoJ of cover-up after viewing unredacted Epstein files
Ranking member of House judiciary panel said ‘mysterious redactions’ in files obscured names of abusers
SECTION XX — EMERGING PATTERNS OF GLOBAL NETWORK
“When patterns repeat across domains, coincidence and illusions collapses.”
What the Files Reveal Collectively
This section synthesizes the entire record—not by adding new allegations, but by identifying the recurring structural patterns that become visible only when finance, science, academia, media, law, and intelligence-adjacent behavior are analyzed together. Read in isolation, individual documents appear mundane, fragmented, or inconclusive. Read collectively, they reveal a consistent architecture of power that operates indirectly, favors deniability, and persists precisely because it avoids overt command-and-control.
The Epstein files do not point to a single conspiracy or centralized operator. Instead, they expose a repeatable model—one that can function with different actors, in different eras, and across different domains. This model does not depend on secrecy alone. It depends on incentives, prestige, access, and asymmetrical information. Section XV articulates this model clearly so readers can recognize it beyond this case.
Most importantly, this section reframes the story’s significance. The danger is not what was done once, but what can be done again—quietly, legally, and with broad institutional participation that no single entity fully controls or admits.
What the Files Reveal Collectively
1. Science as a Strategic Asset
Across the files, science consistently appears not merely as knowledge, but as positioning. Early access to frontier research confers long-term advantage—economic, political, and security-related. Funding science upstream allows influence over downstream outcomes without ever touching implementation. In this model, discovery is not neutral; it is terrain.
2. Intelligence Interest Without Fingerprints
Intelligence involvement rarely appears as ownership or command. It appears as adjacency—attendance at events, advisory overlap, funding curiosity, or post-hoc relevance. This minimizes exposure while preserving situational awareness. The absence of fingerprints is not evidence of absence; it is evidence of design.
3. Power Prefers Prediction Over Force
Force is costly, visible, and destabilizing. Prediction is quiet, efficient, and scalable. The consistent investment in modeling—pandemics, behavior, systems, markets—reveals a preference for anticipatory control. When outcomes can be forecast and nudged, coercion becomes unnecessary. Power moves earlier in the timeline.
4. Control Through Access, Not Orders
The dominant pattern is not command, but gatekeeping. Who gets funding, who gets invited, who gets published, who gets protected. Access shapes possibility. Orders create resistance; access creates alignment. This is why intermediaries, brokers, and institutions matter more than directives.
5. Why This Model Persists
This model persists because it distributes responsibility and concentrates benefit. Each participant acts rationally within their role—seeking funding, prestige, security, or stability. No single actor bears full moral or legal weight, and no single reform dismantles the system. Persistence is not driven by malice alone, but by structural reward.
6. Key Individuals Involved In Epstein’s Cover-Up
The network surrounding Jeffrey Epstein included a mix of direct associates, legal defenders, financial enablers, and institutional actors whose decisions shaped the outcome of his cases. Ghislaine Maxwell was convicted for her role in recruiting and grooming victims. Former U.S. Attorney Alexander Acosta approved the controversial 2008 non-prosecution agreement that shielded Epstein and unnamed co-conspirators, while attorney Alan Dershowitz was part of the legal team that negotiated the deal. Billionaire Leslie Wexner provided Epstein with financial authority and credibility during key years of his rise. At the time of Epstein’s death in custody, Bill Barr oversaw the Department of Justice, which faced scrutiny over jail failures.
Beyond individuals, systemic breakdowns played a central role. The Federal Bureau of Investigation and the United States Department of Justice were criticized for investigative lapses and the handling of the plea agreement, while the Metropolitan Correctional Center in New York documented severe staffing and procedural failures the night Epstein died. The enduring pattern is not a single mastermind but a combination of legal shielding, elite social insulation, institutional negligence, sealed records, and delayed transparency — conditions that allowed misconduct to persist and continue raising questions long after his death.
Tucker Names Two Key Individuals in the Epstein Cover-up
Tucker exposes Bill Barr and Mike Pompeo’s suspicious connection to the Epstein cover-up.
Closing Orientation
Section XV is not an endpoint; it is a lens. Once these patterns are recognized, they become visible elsewhere—beyond Epstein, beyond science, beyond this moment. The files do not merely expose past behavior. They offer a blueprint for understanding how modern power organizes itself when it seeks influence without accountability.
Tucker on the Terrifying Consequences of the Epstein Files
Tucker shares his big picture concerns about America’s future after the release of the Epstein Files.
The Epstein Files: Mapping the Global Network of Influence🤔🤮🤢
This infographic titled “The Epstein Files: Mapping the Global Network of Influence” visualizes reported allegations surrounding Jeffrey Epstein’s network, i...
Whitney Webb: EPSTEIN, Intelligence & the Global Network of Power | Peter McCormack Show
Whitney Webb is one of the world’s most fearless investigative journalists.In this episode, we go deep into the truth about Jeffrey Epstein and the global cr...
The Epstein Files: Exposing the Elite’s Darkest Secrets - David Icke
🏦 Invest In Luxury Dubai Property https://londonreal.tv/dubai-ytd 🍿 Watch the full interview for free at https://londonreal.tv/rose-icke-xi-silenced-censor...
Epstein’s global reach: The countries that have launched investigations so far
Jeffrey Epstein’s ties to global figures have prompted multiple probes far beyond the United States. James C. Reynolds reports
Epstein files fallout takes down elite figures in Europe, while U.S. reckoning is muted
Unlike in Europe, officials in the U.S. with ties to Epstein have largely held their positions of power.
Epstein files fallout: The high-profile people burned by past dealings with a predator
Jeffrey Epstein killed himself in a New York City federal jail in 2019. But more than six years later, people are still losing their jobs because of him.
"A FINANCIAL LOCKDOWN IS NEAR!" - Whitney Webb’s Shocking Discovery
Check out Whitney Webb's bestselling book exposing the criminal rise of Jeffrey Epstein (One Nation Under Blackmail): https://amzn.to/4kcNCdICredit to Tom Bi...
It Begins: This Is Their Plan For 2026 (and they're not hiding it) | Whitney Webb
This video confronts a hard truth many prefer to ignore: Bitcoin’s future is being quietly shaped not as a revolutionary currency, but as a compliant storage technology for global finance. Drawing connections between Wall Street figures, intelligence networks, and political theater, the discussion argues that elections and ideological branding mask a deeper continuity of power, one in which bankers dominate both the public and private sectors while presenting new financial architectures as liberation.
SECTION XXI — QUESTIONS STILL UNANSWERED
“What remains hidden defines the true boundary of power.”
The Most Dangerous Unknowns
This final section addresses what the Epstein files do not resolve—and why those gaps matter more than any single revelation. After patterns are identified and structures mapped, uncertainty itself becomes the signal. In complex systems, omissions are rarely random. They reflect jurisdictional limits, incentive conflicts, classification boundaries, and deliberate risk management. Section XVI treats unanswered questions not as speculation, but as analytical pressure points—areas where accountability, transparency, and governance failed to keep pace with power.
The Epstein files close many loops while opening others. They show how influence operated, but not always where it ended. They reveal funding pathways, but not every outcome they enabled. They document proximity to science, finance, and institutions, but not every decision shaped in those spaces. This section catalogs those unknowns so readers understand where certainty ends—and why.
The “who” remains unanswered not because evidence is absent, but because systems are structured to diffuse responsibility. Power at the global level rarely resides in a single individual, group, ideology, or command center. It operates through overlapping networks of finance, institutions, legal protections, and cultural deference that make attribution difficult by design. As scrutiny increases, these systems instinctively move to protect themselves—limiting discovery, narrowing narratives, and framing exposure as isolated misconduct rather than structural failure. What the Epstein files have done is destabilize that containment. They have shifted the conversation from individual crimes to systemic enablement, and that shift is what threatens entrenched interests of the entire system
Claims of a singular, centuries-old “hidden hand” reflect a deeper intuition: that the scale, persistence, and protection surrounding elite abuse cannot be explained by coincidence alone. Whether interpreted through ideological, cultural, or historical lenses, the underlying signal is the same—concentrated power resists transparency, especially when exposure would implicate multiple pillars at once. The Epstein disclosures are not the conclusion of this reckoning; they are an opening phase. As systems lose their ability to compartmentalize information and suppress pattern recognition, collapse does not arrive as spectacle, but as erosion—confidence, legitimacy, and authority draining away faster than narratives can contain them.
Importantly, unanswered questions are not accusations. They are requirements for future inquiry. When systems discourage discovery, the absence of answers becomes part of the architecture. Section XVI makes those absences explicit.
The Most Dangerous Unknowns
1. What Research Was Never Published?
Not all research enters the public record. Some projects conclude without papers, some remain proprietary, and others are halted quietly. The files raise the possibility that high-impact work—especially in modeling, bio-systems, AI foundations, and materials—advanced without peer review or disclosure. The question is not whether this happens, but how often and with what consequences.
2. What Discoveries Changed Policy Quietly?
Policy shifts sometimes precede public justification. Models inform decisions before data is released; assumptions shape rules before debate occurs. The files suggest proximity between research insights and policy environments that may have altered outcomes without transparent attribution. Identifying those inflection points remains unresolved.
3. Who Retained Data Control? Who Took Control of the Epstein Empire?
Control over data determines power over interpretation. Who owned datasets? Who set access rules? Who decided what could be shared, archived, or deleted? The files hint at fragmented custody across institutions and private entities, complicating oversight and auditability. Data control is governance—often invisible, always decisive.
4. What Technologies Were Shelved—or Weaponized?
Some technologies disappear not because they fail, but because they succeed too well—or threaten established interests. Others migrate from civilian contexts into strategic applications. The record does not fully answer which paths were taken, where work was paused, or how discoveries were repurposed. The fork in the road is rarely documented.
5. Why Epstein Was Protected for So Long
The most persistent question is not about guilt, which was established, but about duration. Why protections held across jurisdictions and institutions. Why warnings were ignored. Why accountability stalled. The files suggest no single guardian, but overlapping incentives that discouraged exposure. Protection emerged as an outcome of structure, not a single decision.
6. Growing Public Awareness of Adrenochrome Production Networks
Whistlerblower testimonies surrounding adrenochrome production have circulated widely in alternative research communities, often linked to elite child trafficking narratives. The rampant use by Hollywood and Industry elites is clear evidence that substantiated the existence of organized “adrenochrome factories.” However, the persistence of evidence signals deep mistrust rooted in documented abuse, secrecy, and institutional exposure of satanic practices of blood doping as a youth drug? From an analytical standpoint, the relevant question is not belief—but why extreme satanic practices are now being revealed to the public in a blatant stand to normalize all practices of child trafficking and sexual abuse.
Analytical threshold required:
Verified supply chains, forensic evidence, financial records, or corroborated whistleblower testimony subjected to independent validation.
7. Organ Transplant Exploitation & Illicit Trafficking Risks
The global organ transplant industry is a documented site of human trafficking risk, particularly in regions with weak regulation. While no direct evidence links Epstein to organ trafficking, the broader concern remains unresolved: how elite medical demand, global inequality, and opaque supply chains intersect. The Epstein files raise structural questions about mobility, money, and access that mirror known vulnerabilities in illicit organ markets.
Key unresolved issue:
Whether elite protection mechanisms observed elsewhere also shield medical exploitation networks from scrutiny.
8. Human Trafficking Beyond Sexual Exploitation
Sexual exploitation is only one dimension of human trafficking. Forced labor, medical exploitation, and coercive dependency networks remain underreported and under-prosecuted globally. The Epstein case exposes how status and capital can suppress investigation, prompting inquiry into whether similar shielding exists across other trafficking domains.
Analytical focus:
Structural similarities—not direct attribution—between known trafficking systems and elite-enabled protection patterns.
9. Existing Laboratories of Human Cloning or Experimental Human Research
Exposure of human cloning labs or experimental human research programs remain unsubstantiated in MSM, yet new testimony and revelation confirm the science and clones does exist. The cloning of animals (secretly humans) has existed for over 30 years? However, these claims persist in discourse due to real documented witness testimony of Hollywood Clone Labs for the Stars and Elite Class. Eyewitnesses over the past 10 years have been leaking information on a consistence basis about major changes in younger looking clones, questionable public actions, and degraded character of major public figures.
Threshold required:
Public-reviewed evidence, whistleblower corroboration, or government documentation confirming human experimentation beyond legal and ethical bounds.
10. Bioweapons Research & Classified Bio-Labs
Bioweapons research exists across a broad spectrum within military-controlled frameworks, often under classified designations. The Epstein files raise indirect questions about how bio-research, funding, and policy influence interact—not about specific weaponization claims. The unresolved concern is proper governance and transparency does not existence.
Key unknown:
Where civilian bio-research ends and classified application begins—and who oversees the transition.
11. Allegations of Human Breeding Farms or Controlled Population Experiments
History of “human breeding farms” goes back 100’s of years, as with persistent allegations emerging from distrust in elite secrecy societies. These narratives reflect the expansion of elite control provided by 1000’s of human DNA offsprings (bastard children) for the purpose of infiltration of all top positions in governments, military, industry, and all key institutions. These elite breading farms serves to map an ecosystem of control, validate by 100’s of witness claims.
Analytical relevance:
Extreme narratives emerge where verified abuses meet systemic opacity.
12. Genetic Engineering Research & Transhuman Future Race
Unlike other subtopics, genetic engineering research (Transhumanism) is well-documented and rapidly advancing. The unresolved question is not its existence, but whether ethical oversight keeps pace—especially in private (robotic), military (super solder technology), or international contexts. The Epstein files highlight how funding, access, and secrecy can weaken accountability mechanisms across domains.
Key inquiry:
Who sets ethical boundaries when research is privately funded, globally distributed, and strategically valuable?
13. New Evidence Epstein is Still Alive?
There is no verified or credible evidence that Jeffrey Epstein is still alive. Multiple independent investigations, official medical examinations, and court proceedings have concluded that he died in federal custody in August 2019. Claims that he survived are based on speculation, inconsistencies in prison oversight, and distrust of institutional narratives—not documented proof. Extraordinary claims require verifiable evidence, and to date, none has been produced that withstands scrutiny.
14. Epstein’s Marriage proposal Karina SulIak? Assets Left to Her in the Will?
Jeffrey Epstein reportedly had connections to a woman named Karyna Shuliak (often misspelled in media), who was described in court filings as his girlfriend and was associated with properties he controlled. After his death, documents revealed he had transferred certain assets into trusts and entities, and Shuliak was reportedly connected to some of those property arrangements, including a Paris apartment. Public records do not show a legally recognized marriage between Epstein and Shuliak, and there is no confirmed evidence of a formal marriage proposal documented in court proceedings. Most of Epstein’s estate, valued in the hundreds of millions of dollars, was placed into a trust shortly before his death, complicating direct beneficiary claims and shielding detailed distribution information from public view.
Closing Orientation
Unanswered questions are not failures of analysis; they are maps of resistance. They reveal where power hardens, where incentives align against transparency, and where institutional architecture actively deflects scrutiny. In complex systems, what remains obscured often matters more than what is revealed. These gaps are signals—pointing not to randomness, but to pressure zones where accountability encounters structural limits.
Throughout this report, the pattern is consistent: when inquiry approaches areas that threaten prestige, capital, or long-term strategic advantage, visibility drops. Documents fragment. Jurisdictions blur. Oversight disperses. Silence becomes normalized. This is not because truth is unknowable, but because access is constrained. The unanswered questions cataloged in Section XVI mark the boundaries of permitted inquiry—and, by extension, the frontiers where future investigation will be most consequential.
Section XVI does not close the record; it orients the next phase. It defines where researchers, journalists, legal advocates, and truth seekers must focus if systemic accountability is to advance. The investigation does not end with disclosure. It continues wherever resistance is strongest—because that is where power is most invested, and where understanding matters most.
Who Took Over Epstein's Empire? - Whitney Webb
This is a clip from the Before Skool Podcast with Whitney Webb. See full podcast here https://www.youtube.com/watch?v=B1pTej2QPd0&t=4329sWhitney Webb has bee...
Protecting Pedophile Predators: Carole Cadwalladr on Jeffrey Epstein & the Elite's Veil of Silence
Support our work: https://democracynow.org/donate/sm-desc-ytLawmakers on Capitol Hill are accusing the Justice Department of covering up the names of co-cons...
What NO ONE's telling you about the Epstein Files | The News Agents USA
In an exclusive interview with Emily, Amy Wallace - who co-authored Virginia Giuffre's posthumous memoir - warns that lives are being put in danger by the wa...
Craziest Parts of the Epstein Files YOU MISSED | Jay Dyer & Shaun Attwood
Shaun Attwood sits down with Jay Dyer to talk about the crazyest part of the Epstein files, Vatican Connections, Bill Clinton being compromised.In this lives...
SECTION XXII — DISCLOSURE ORIENTATION FOR TRUTH SEEKERS
“Truth requires structure, emotional regulation, and the courage to see clearly without becoming consumed.”
Disclosure Without Discipline Becomes Noise
This section establishes the operating discipline for engaging material of this magnitude and sensitivity. High-risk research demands more than curiosity—it requires restraint, structure, and internal coherence. The purpose of this orientation is not to tell readers what to think, but how to think clearly under pressure, especially when evidence implicates powerful systems and evokes strong emotional responses. Without orientation, inquiry degrades into reaction; with it, investigation remains grounded and productive.
GAR’s approach treats truth seeking as a practice, not a performance. The goal is durability—maintaining clarity across long timelines, incomplete data, and institutional resistance. This section equips readers to engage responsibly, avoiding both naïveté and cynicism, while preserv Save ing the capacity to recognize patterns without collapsing into speculation.
Disclosure Without Discipline Becomes Noise
1. How GAR Handles High-Risk Research
GAR prioritizes systems-level analysis over event-driven sensationalism. High-risk research is approached incrementally, with emphasis on document provenance, incentive mapping, and cross-domain correlation. Claims are weighted by evidentiary strength, not emotional impact. Where certainty ends, GAR marks boundaries explicitly rather than filling gaps with conjecture.
2. Evidence vs. Inference Discipline
Evidence is what can be verified. Inference is what can be reasonably concluded from patterns. GAR maintains a strict separation between the two. This discipline preserves credibility and prevents overreach. Inference is allowed—but only when labeled, bounded, and grounded in multiple independent signals. Precision here protects the investigation from discrediting shortcuts.
3. Avoiding Hero–Villain Simplification
Complex systems rarely operate through singular villains or saviors. Reducing analysis to heroes and enemies obscures structure and misallocates responsibility. GAR avoids moral caricature, focusing instead on roles, incentives, and architectures. This does not excuse wrongdoing; it clarifies how wrongdoing persists without requiring constant intent.
4. Emotional Regulation in Dark Material
Exposure to exploitation, abuse, and institutional failure can overwhelm judgment. Emotional regulation is not detachment; it is capacity management. GAR encourages pacing, reflection, and grounding practices to prevent burnout and reactive conclusions. Clear thinking requires nervous-system stability, especially when confronting disturbing truths.
5. Why Precision Matters More Than Outrage
Outrage is understandable—but it is transient and easily redirected. Precision endures. Institutions adapt to outrage; they struggle against coherent, evidence-based critique. Precision builds legal, journalistic, and historical records that outlast news cycles and resist dismissal. GAR prioritizes accuracy because it compounds over time.
6. Staying Grounded While Investigating Power
Power systems rely on intimidation, complexity, and fatigue. Staying grounded means maintaining context, community, and purpose. Truth seeking is not isolation—it is alignment with shared standards of rigor and integrity. Section XVII closes the report by reinforcing a simple principle: clarity is strength. Those who remain calm, precise, and patient are the hardest to deter.
What is a Seeker? | Spirituality for Seekers
A Seeker is someone who investigates spiritual matters for themselves, rather than blindly adopting the ‘truth’ of any existing tradition. According to the dictionary, a seeker is a person who tries to find something by searching for it. In the sense that I use the word, a Seeker (capitalised) is an individual who is actively looking to discover and use spiritual truths with the intention of living a richer, happier and more meaningful life.
How Professional Truth Seekers Search for Answers
Nine experts describe how they sort signal from noise. The answer to questions about human life isn't a certain thing, like measuring how a stone drops to the ground in exactly so many seconds. If it were, it probably would not be life. It would be a stone. Within biomedicine, it's tricky finding out if an effect is real—there are different standards across different fields. Not all tools will work for every question, and there are different levels of complexity for what we know before we even start a study.
What It Really Means to Be a Seeker of TRUTH
We are all whistleblowers if we want to be. It starts with keeping ourselves accountable. As I watch my own mother decline in a state of extended, deteriorating health, a woman who was couched in the modern medical paradigm as a registered nurse, and who once helped the local police solve a murder with psychic knowledge in her youth, I split the hairs between what is ‘real’ and ‘unreal’ on a daily basis.
The Epstein Event: What It Reveals About Reality | Shunyamurti Wisdom Teaching
Watch the full teaching for free! This is an excerpt from a longer teaching posted on our Members Section. Sign up for your free 10-day trial now: https://bi...
Orientation Forward
This report is not an endpoint. It is a framework for continued inquiry—measured, disciplined, and resilient. Truth seekers do not rush to conclusions. They build understanding slowly, withstand pressure, and keep their footing as the terrain grows more complex. In an era of compressed timelines and amplified narratives, orientation matters more than speed. The work is not to react to every signal, but to discern which signals matter, which threads are forming, and which patterns are durable. Clarity is earned through patience, cross-verification, and the willingness to revise assumptions when stronger evidence emerges.
Moving forward requires both intellectual rigor and emotional steadiness. Inquiry without discipline becomes noise; conviction without evidence becomes fragility. Our task is to remain grounded while exploring difficult material—neither dismissing prematurely nor accepting blindly. The landscape will continue to shift. New information will surface. Contradictions will appear. That is not a failure of the process; it is the process. Stay observant. Stay precise. And above all, remain committed to truth as a pursuit, not a possession.
APPENDICES (Living)
These appendices are designed to evolve as new documents, disclosures, and peer-reviewed materials emerge.
Appendix A — Scientific Fields Referenced
This report references multiple scientific domains that consistently attract dual-use interest, elite funding, and strategic attention. The list below reflects fields repeatedly appearing across funding patterns, institutional partnerships, and policy relevance—not allegations of misuse.
Key Fields & Reference Gateways:
-
Epidemiology & Pandemic Modeling
-
Agent-based modeling
-
Network contagion theory
-
R₀ estimation and behavioral response modeling
-
Public references: WHO modeling frameworks, NIH/NIAID publications, Imperial College London reports
-
Systems Biology & Bioinformatics
-
Host–pathogen interaction modeling
-
Genomic sequencing and data integration
-
References: Nature, Cell, NIH Genomic Data Commons
-
Artificial Intelligence (Foundational / Pre-Boom Era)
-
Machine learning theory
-
Pattern recognition and anomaly detection
-
References: arXiv (cs.AI, stat.ML), early DARPA AI research archives
-
Complexity Science & Chaos Theory
-
Nonlinear systems
-
Emergent behavior in social and biological systems
-
References: Santa Fe Institute publications, Complexity journal
-
Human Behavior Modeling & Decision Theory
-
Advanced Mathematics & Predictive Modeling
-
Materials Science & Exotic Physics
-
Novel materials
-
Energy storage and transfer
-
Sensing and shielding technologies
-
References: DOE national labs, Physical Review journals
Appendix B — Funding Structures Glossary
This appendix defines financial mechanisms referenced throughout the report, emphasizing structure rather than intent.
Key Structures:
-
Donor-Advised Funds (DAFs):
Charitable vehicles allowing donors to retain influence over distributions with limited disclosure.
-
Private Foundations:
Entities that fund research, policy, and institutions while shaping agendas through grant criteria.
-
Program-Related Investments (PRIs):
Investments made by foundations that blend financial return with mission alignment.
-
Public–Private Partnerships (PPPs):
Collaborative arrangements between governments, universities, and private capital.
-
Special Purpose Vehicles (SPVs):
Isolated entities used to compartmentalize funding, liability, or research objectives.
-
Reinsurance & Catastrophe Bonds (Contextual):
Financial instruments tied to crisis events (e.g., pandemics, natural disasters).
Appendix C — Known & Suspected Research Venues
This appendix catalogs institutional categories repeatedly appearing in funding and collaboration networks. Inclusion does not imply wrongdoing; it reflects relevance to systemic analysis.
Venue Categories:
-
Elite Universities & Research Institutes
-
Ivy League and peer institutions
-
Major global research universities
-
Interdisciplinary institutes bridging science and policy
-
Private Conferences & Invite-Only Symposia
-
Independent & Private Labs
-
Policy-Adjacent Think Tanks
-
International & Multilateral Research Bodies
Appendix D — Methodology & Source Integrity
This report follows a strict evidence hierarchy to preserve credibility and avoid speculative collapse.
Methodological Standards:
-
Primary Sources First
-
Secondary Sources (Contextual Only)
-
Inference Rules
-
Inference is labeled explicitly
-
Requires multiple independent signals
-
Never substitutes for documented fact
-
What Is Excluded
-
Anonymous claims without corroboration
-
Ideological framing not supported by evidence
-
Sensational narratives lacking structural support
-
Living Review Process
-
Appendices updated as documents are released
-
Errors corrected transparently
-
New material appended, not retrofitted
Orientation Note
These appendices are not an endpoint. They are navigation tools—designed to help researchers, journalists, and truth seekers separate domains, verify claims, and maintain precision as new material emerges.
The 3 C’s of Life: “Choices, Chances, and Changes”,
You must make a choice to take a chance or your life will never change. – Zig Ziglar










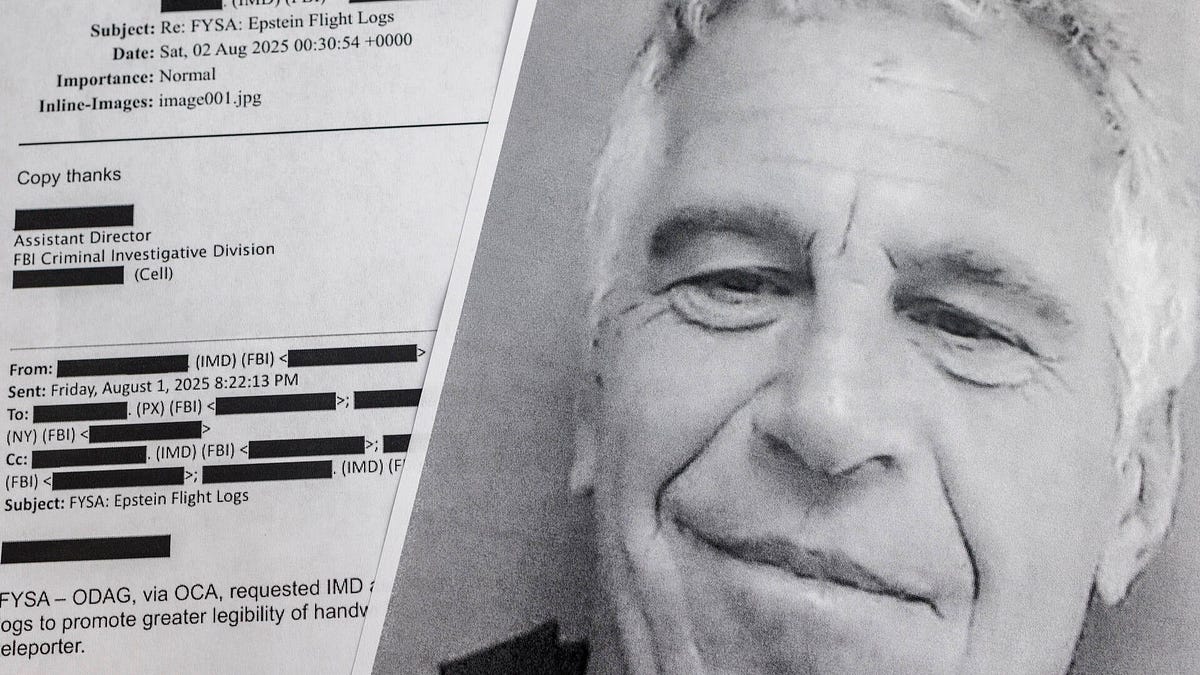























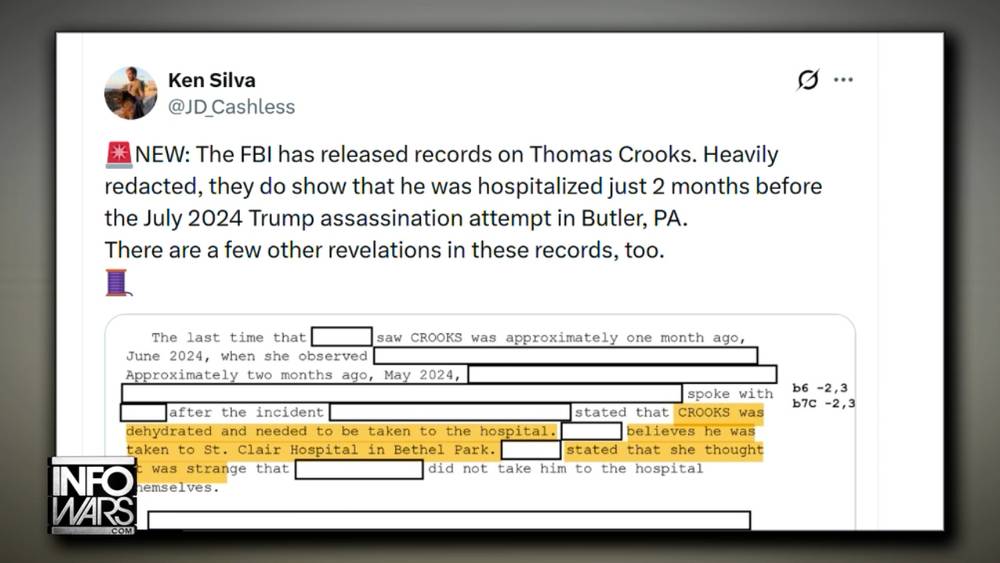



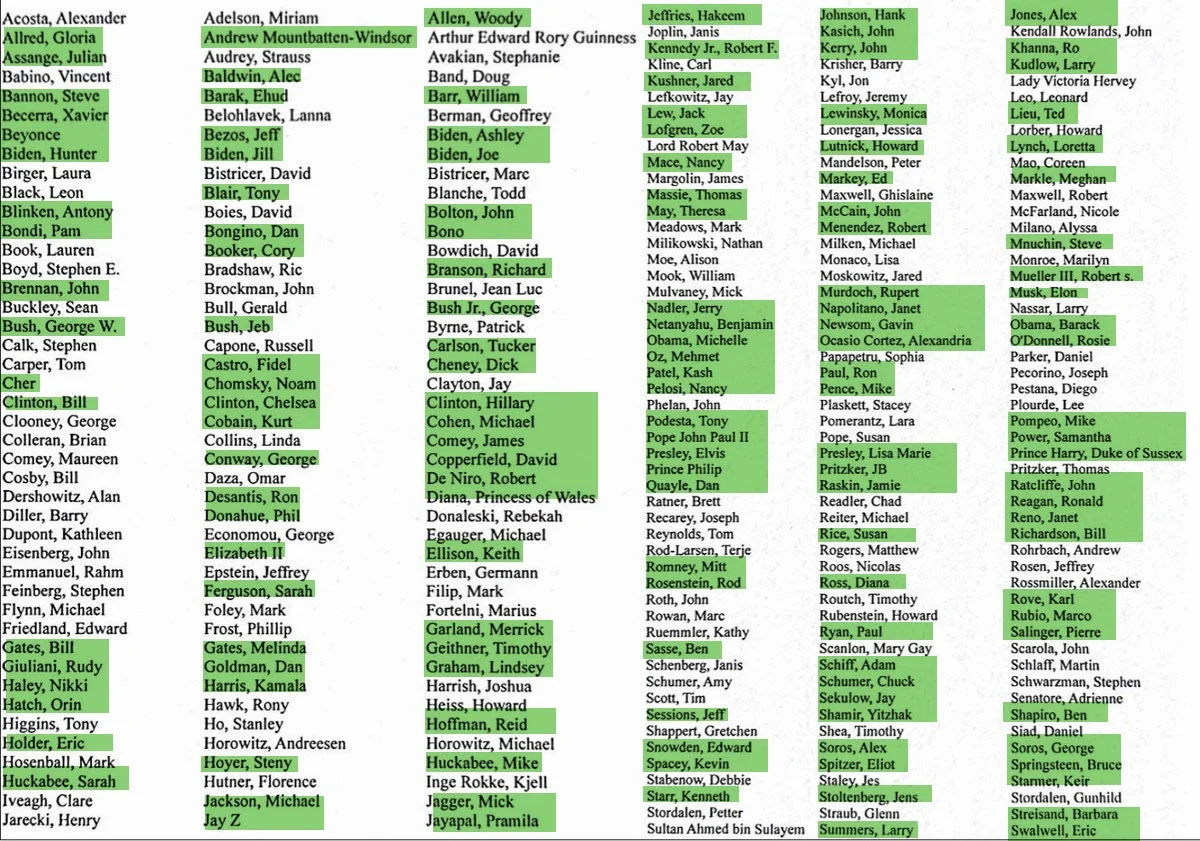



























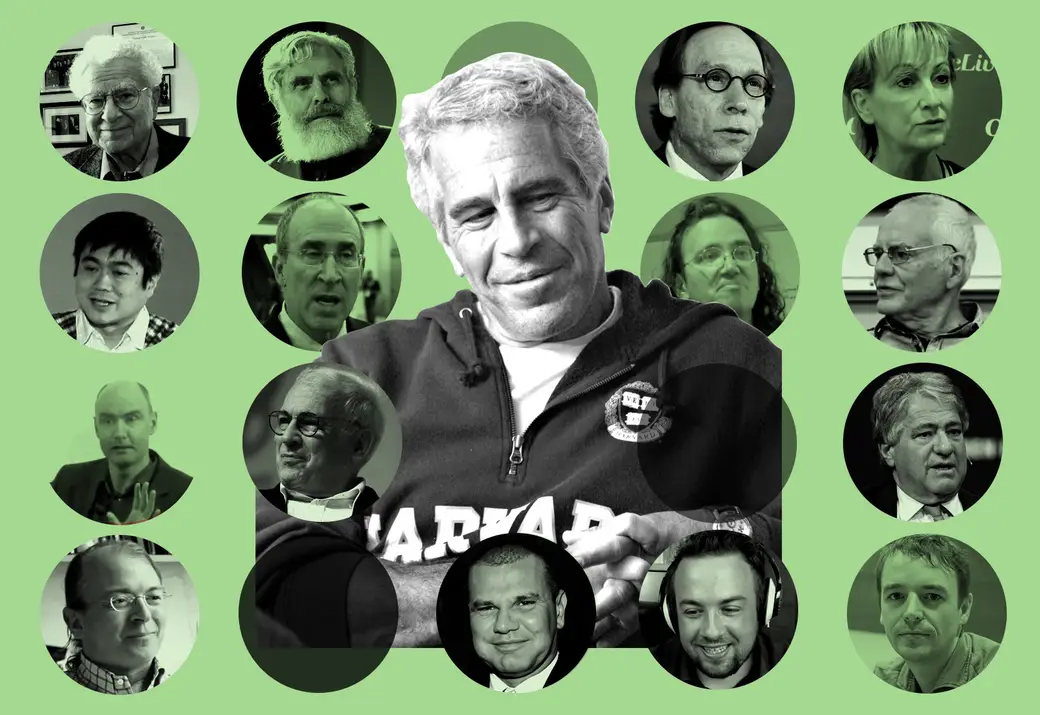
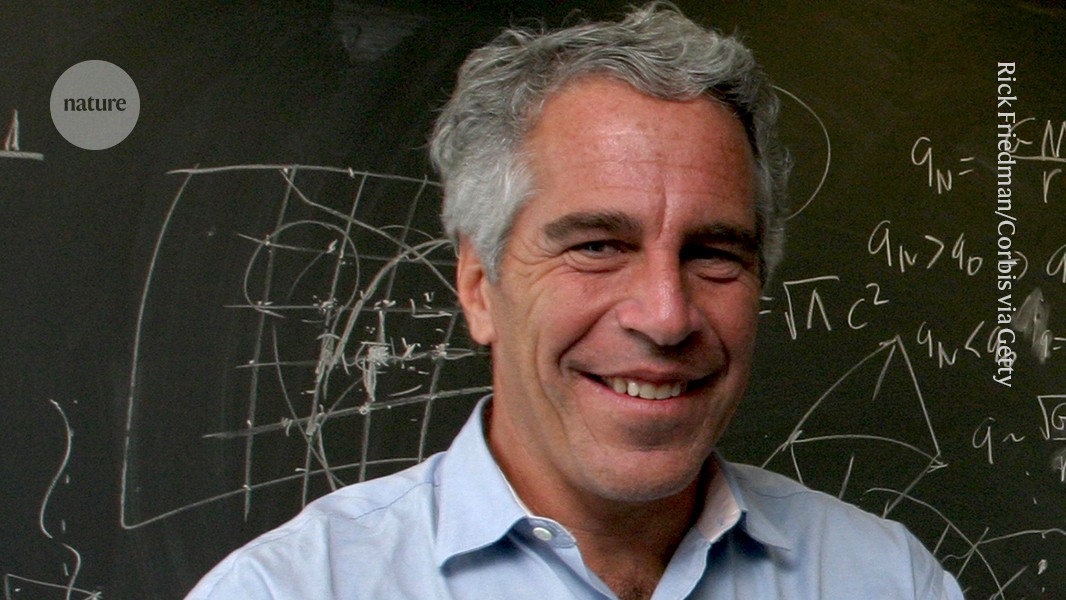














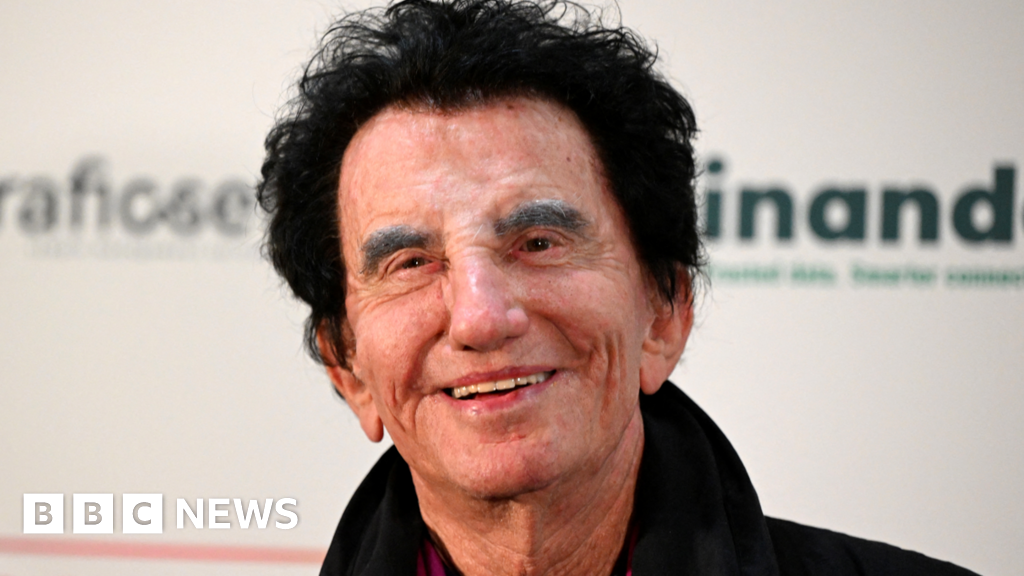


































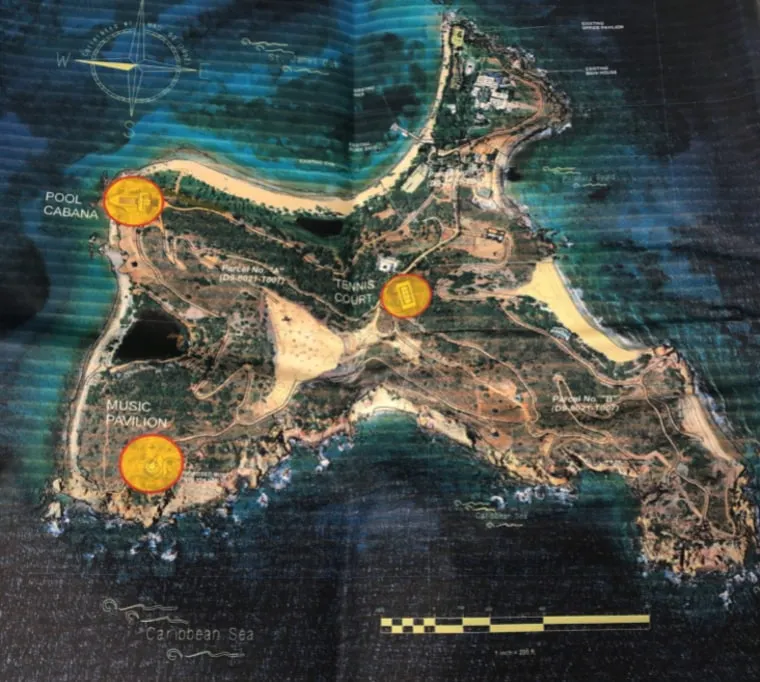






































































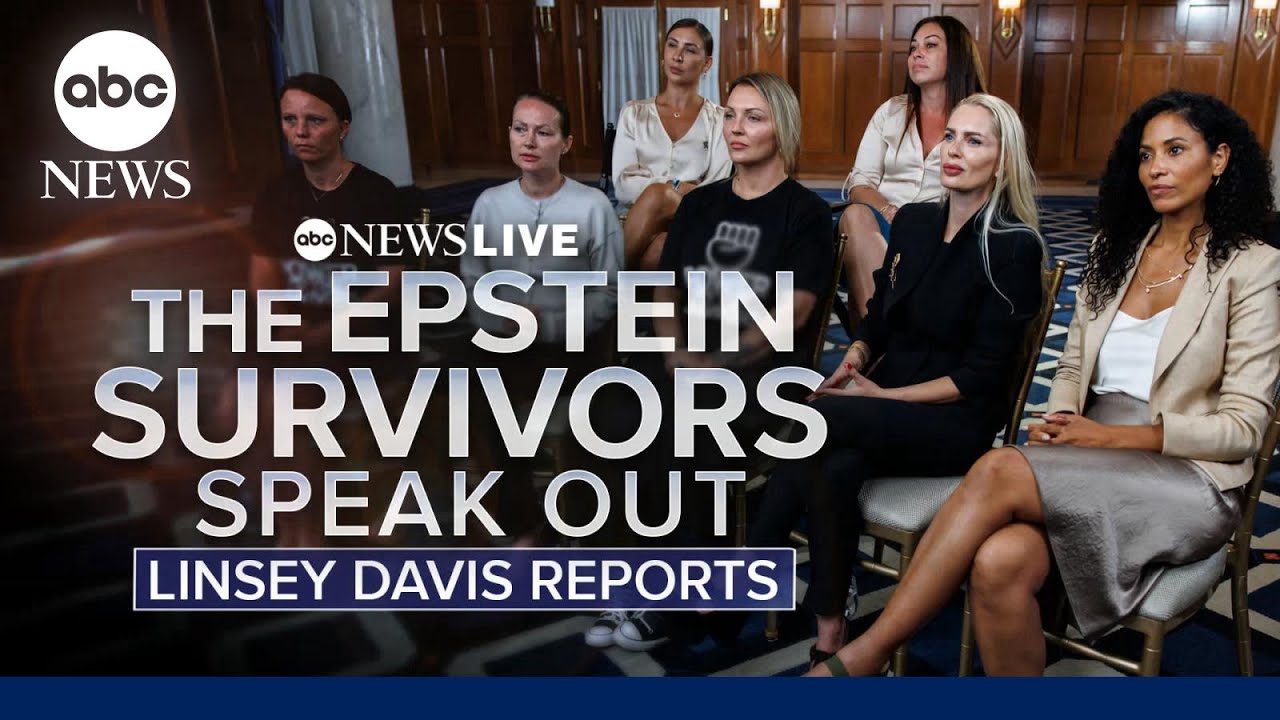




























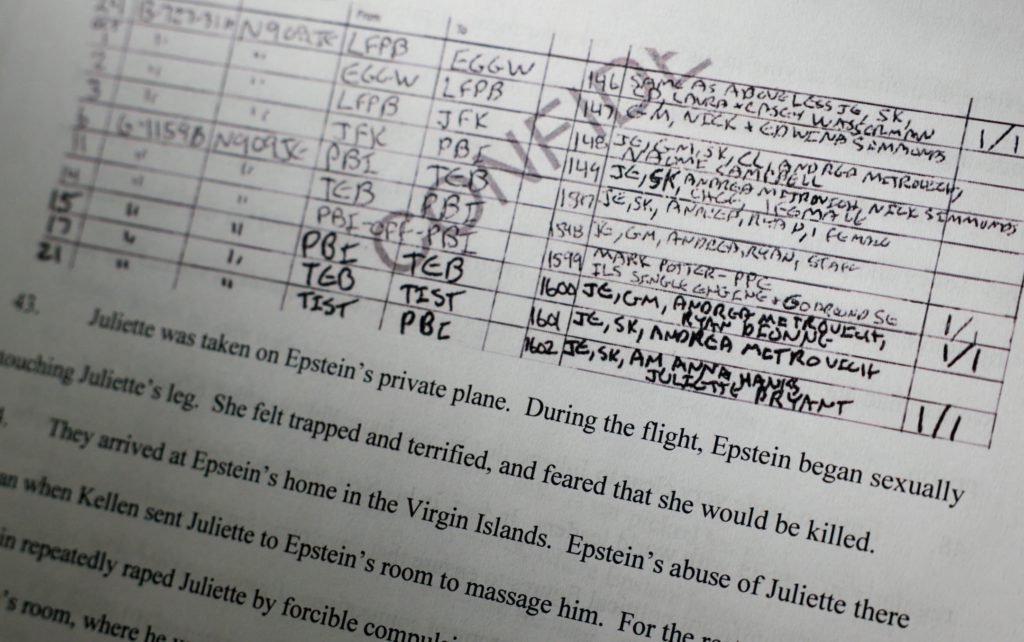


)









.jpeg?trim=0,0,0,0&width=1200&height=800&crop=1200:800)